Cofense Intelligence
@cofenseintel
#Phishing and #malware analysis from Cofense Research, Cofense Intelligence and the Phishing Defense Center.
ID: 847956750
https://cofense.com/product-services/phishing-intelligence/ 26-09-2012 19:15:29
3,3K Tweet
2,2K Followers
92 Following




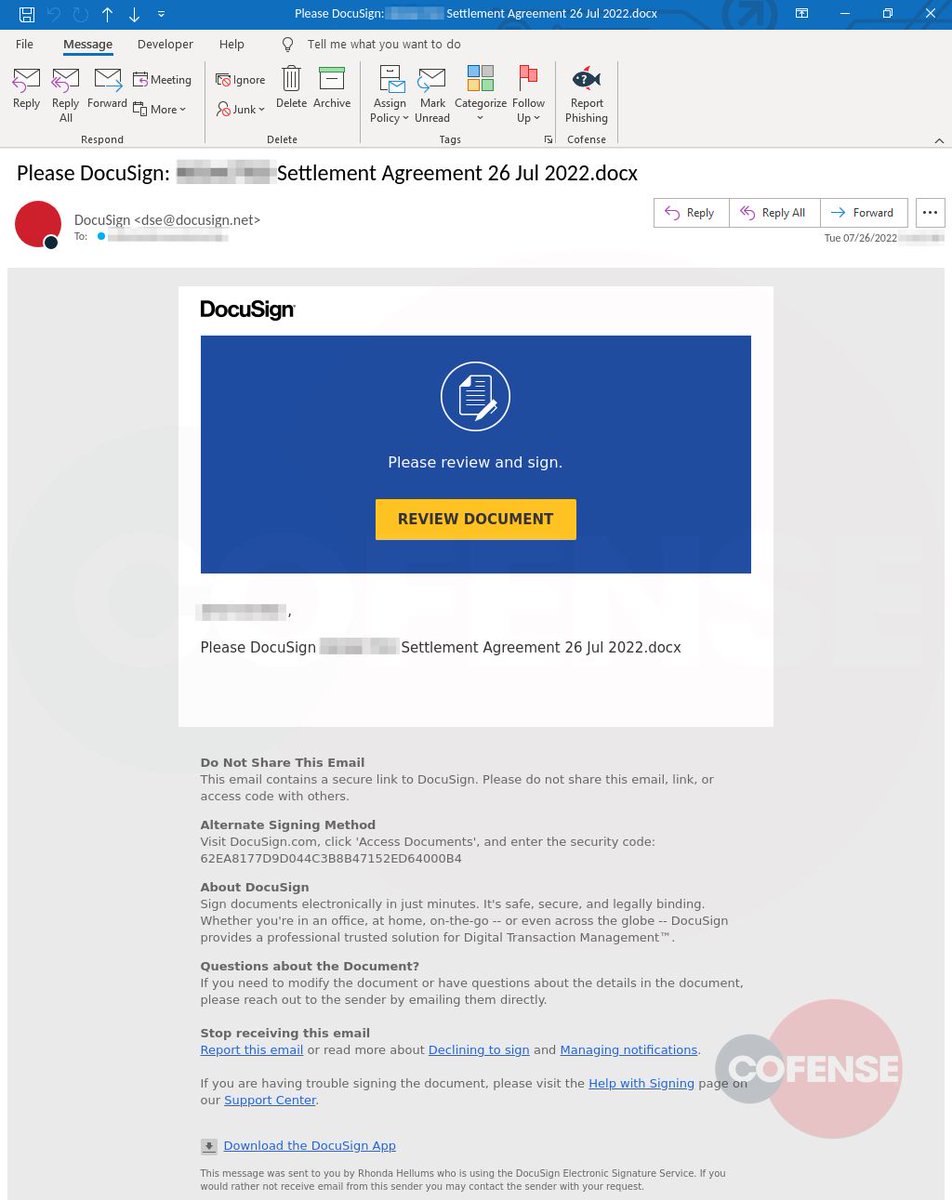
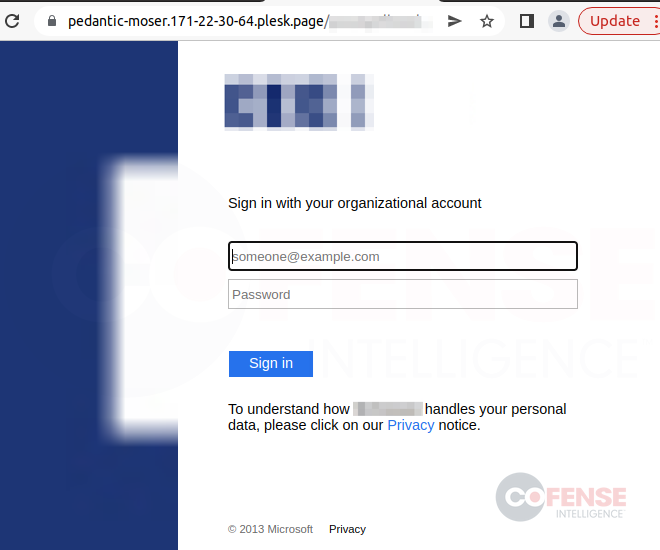
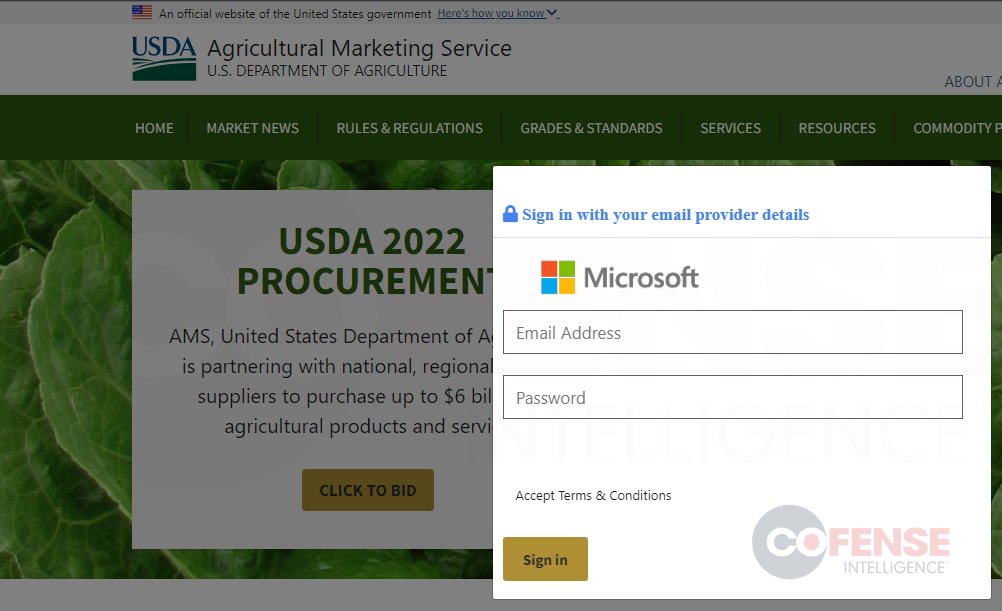
A well-crafted credential #phishing campaign is specifically targeting the food manufacturing industry, spoofing Dept. of Agriculture. Images below are of the original phish and subsequent landing/harvesting pages. Cofense Intelligence customers can find details in Cofense ThreatHQ.



#Lampion malware is back, this time targeting WeTransfer. We found this #phishing attack in environments using #Microsoft as their standard email security. Bill Toulas BleepingComputer #malware #cybersecurity

Uber hack updates from Ronnie Tokazowski 👇 VPN credentials compromised via social engineering and hard-coded credentials in scripts led to the compromise of Uber's infrastructure. Also, make sure you use MFA on your VPN and train your users not to leak VPN credentials. #cybersec


Microsoft 365 phishing attacks impersonate U.S. govt agencies - Bill Toulas bleepingcomputer.com/news/security/…




❗NEW #BEC REPORT❗ 𝗪𝗵𝗮𝘁 𝗵𝗮𝗽𝗽𝗲𝗻𝘀 𝘄𝗵𝗲𝗻 𝘆𝗼𝘂 𝗴𝗶𝘃𝗲 #𝗕𝗘𝗖 𝘀𝗰𝗮𝗺𝗺𝗲𝗿𝘀 $𝟱𝟬𝟬 𝘄𝗼𝗿𝘁𝗵 𝗼𝗳 𝗴𝗶𝗳𝘁 𝗰𝗮𝗿𝗱𝘀? That's what Ronnie Tokazowski wanted to find out. Shocker, they move extremely fast. Read the full report 📝 bit.ly/3DOURUD




"Human intuition is often much better at recognizing these differences, so training employees to be vigilant against phishing threats is a critical element of good cyber defense." Another great discovery from Cofense Intelligence. Written by Tara Seals. bit.ly/45oflAh

Major U.S. energy org targeted in QR code phishing attack - Bill Toulas bleepingcomputer.com/news/security/…

🚨 New “Complaint Stealer” Malware Escalates, Targeting Cryptocurrency Wallets & Hospitality Sector🚨 Cofense Intelligence has seen an increase in the last few days in the newly christened #ComplaintStealer malware. Here's what we know so far 👇 cofense.com/blog/new-compl…