h4x
@c0ner0ne
Guy from the late 70’s - former software cracker at CORE - nowadays fighting malware and still interested in breaking things
ID: 3065725185
http://r3v3rs3r.com 01-03-2015 18:37:04
6,6K Tweet
367 Takipçi
457 Takip Edilen




Spread the word! Phrack Zine CFP with demoscene cracktro is live. Turn up the volume and enjoy the awesome stylings of Piotr Bania with some hopefully inspiring text from phrack staff :) phrack.org










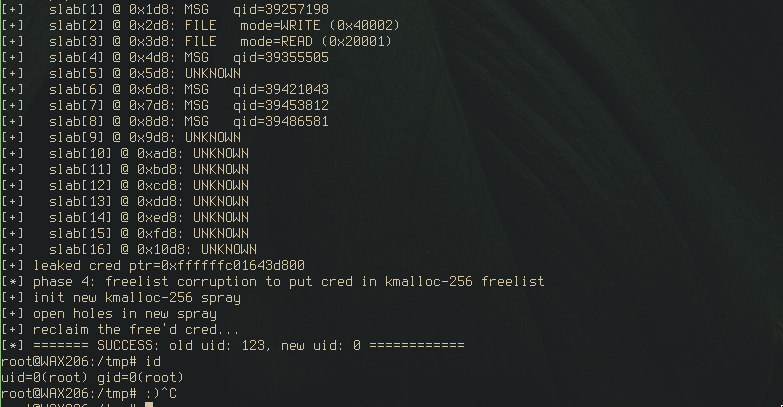
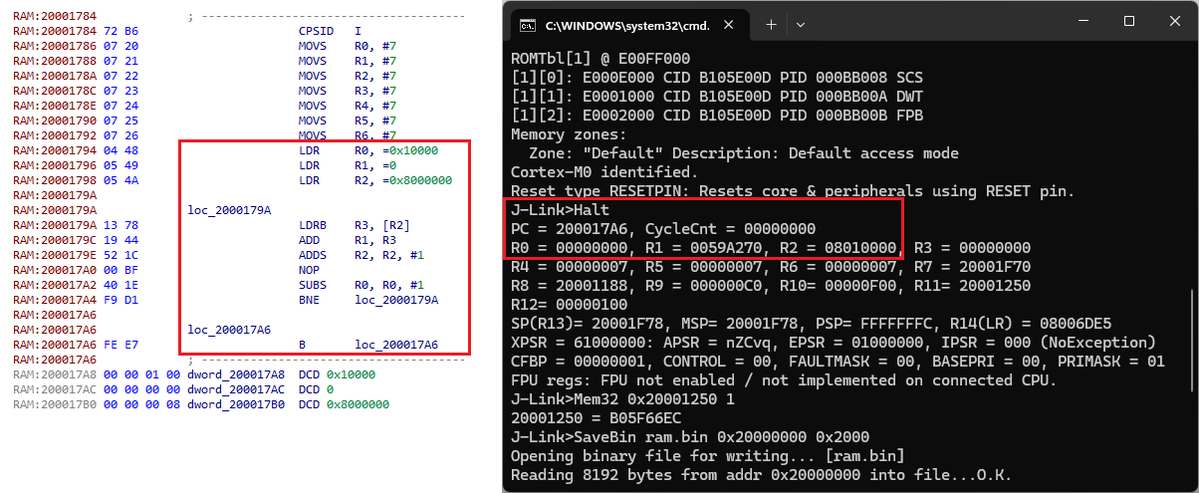
New post is up! This one uses CVE-2025-20741 (a heap overflow in the MediaTek MT76xx driver) to show how a bit of kernel alchemy can turn a heap OOB write into a number of stronger exploit primitives, up to page-level r/w via pipe_buffer corruption :) blog.coffinsec.com/0day/2026/04/0…