Blackwing Intelligence
@blackwinghq
Security Analysis | Vulnerability Research | Reverse Engineering | R & D
ID: 280839031
https://blackwinghq.com 12-04-2011 03:43:32
29 Tweet
310 Followers
6 Following


I use stickers to distinguish my endless stack of research notebooks. Just found this gem of a sticker buried somewhere Hex-Rays SA. Don't know about the company Blackwing but your marketing game is on point Blackwing Intelligence
I'm excited to welcome Josh Pitts (Josh Pitts) to my team Blackwing Intelligence! Welcome Josh!! 🎉
w00t! Teräs and l will be speaking at Microsoft BlueHat next week. More details shortly, but this was fun research and should be a fun talk -- HW, SW, FW RE and lots of pwn. 😈 microsoft.com/bluehat/ Blackwing Intelligence

Our own Jesse D'Aguanno and Teräs will be presenting "A Touch of Pwn" at Microsoft BlueHat next week! 🎉 Stay tuned for more info... #BlueHat #Blackwing
Stoked to be able to talk about this research our team Blackwing Intelligence did for Microsoft! We examined the security of the most popular embedded fingerprint sensors used for Windows Hello. We’ll discuss our vuln research process, challenges, and the critical vulns we found (+demos)😉
Boom! Windows Hello fingerprint authentication bypassed on top three devices: - Dell Inspiron - Lenovo ThinkPad - Microsoft Surface Pro Still waiting for recordings from our BlueHat talk to drop, but here's our writeup: blackwinghq.com/blog/posts/a-t… #infosec #security #vulnresearch



Windows Hello fingerprint security failures! Great work from Blackwing Intelligence "We initially implemented this attack on a Raspberry Pi 4, but reimplemented it in TamaGo on the USB armory since the RPi4 takes too long to boot and we wanted a quicker demo. 😜" blackwinghq.com/blog/posts/a-t…
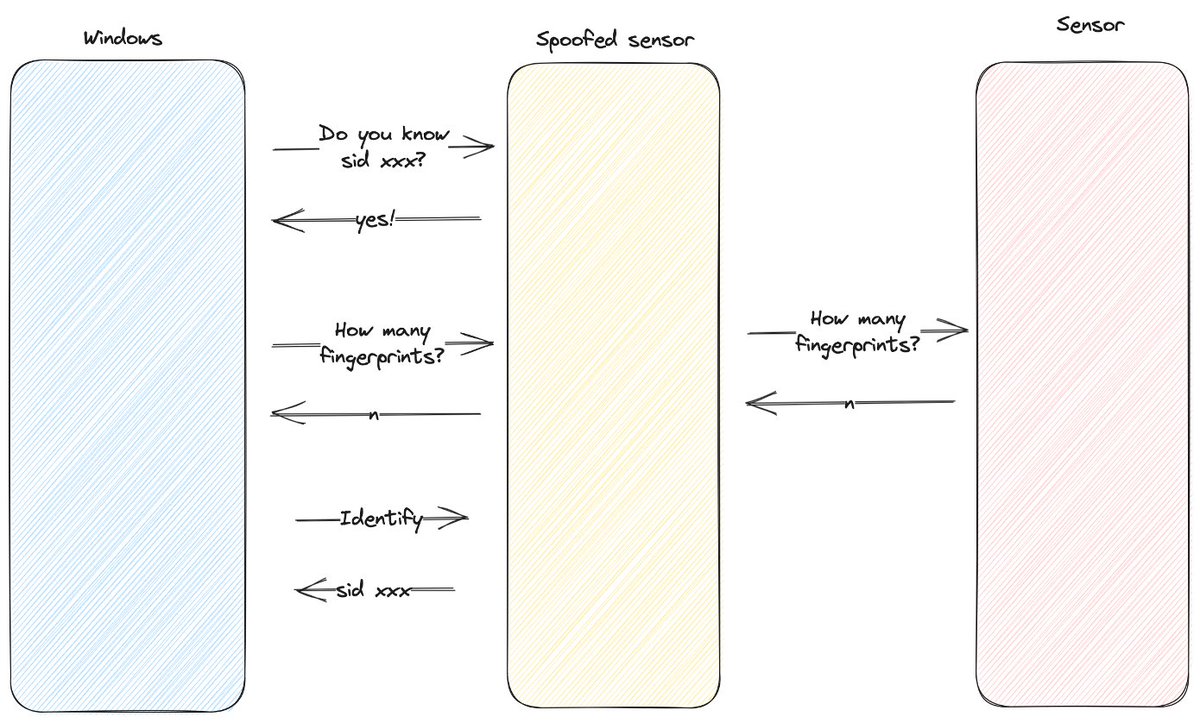

Quality research and an incredibly easy to follow writeup by Blackwing Intelligence on bypassing windows hello fingerprint authentication: blackwinghq.com/blog/posts/a-t… While the attacks require physical access, the creativity in them is excellent and I'm sure not the last we will hear on this.
We’ve been thinking about putting on some training around Apple vuln research and exploitation (stay tuned Blackwing Intelligence). In that spirit, Josh Pitts created a tool to play with libmalloc interactively to better understand its internals. Check out his new blog here:

My second sticker (from Blackwing Intelligence) obtained by begging someone on Twītter after seeing someone post a picture (also their FemtoCTF is neat)


Research Blog Announcement! 📢 After finding a media parsing bug in a little-known binary, our own Franco Belman (Franco Belman) goes hunting for variants across the internet. In this post he details his process for "Finding Vulnerability Variants at Scale" blackwinghq.com/blog/posts/fin…