AB
@anittude
#DFIR lead @News_CRA. Ex @PwC, Husband, Dad, Tea and (now Coffee) addict, runner, and biker. International affairs @warstudies. Tweets my own.
ID: 103346655
09-01-2010 18:53:41
1,1K Tweet
109 Followers
214 Following

Excellent summary and analysis 👇 Fog of war: how the Ukraine conflict transformed the cyber threat landscape @google blog.google/threat-analysi… Shane Huntley Mandiant (part of Google Cloud)



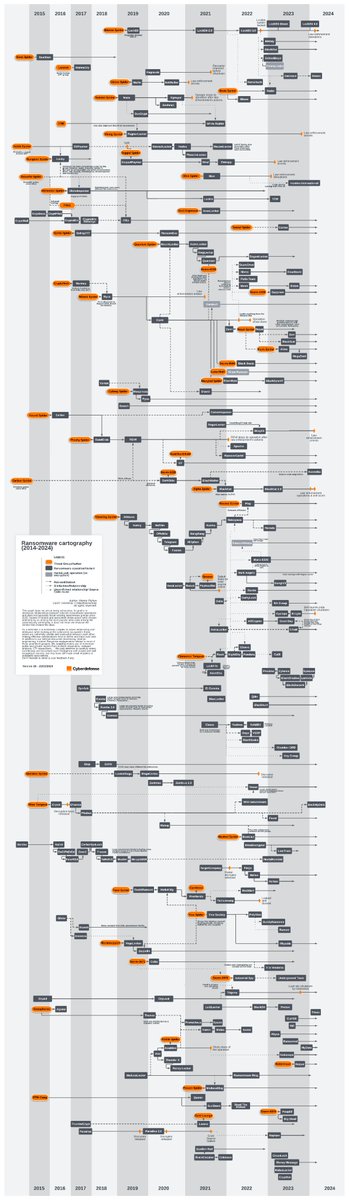
6 months ago, I started working on a way to better map the #ransomware ecosystem and its evolution, including rebrands.🔎 I am really happy to share this handmade cartography, which is based on Orange Cyberdefense resources, #OSINT and reverse engineering. ➡️ github.com/cert-orangecyb…


In partnership with Cybersecurity and Infrastructure Security Agency, we're announcing new steps to protect our customers and improve the security of Microsoft cloud platforms. Learn how this will help defend against nation-state cyber threats: msft.it/6016gfokq #CloudSecurity #IncidentResponse




💢Active Directory: Advanced Threat Hunting - In-depth investigation and analysis of the Active Directory with ADRecon!💢 Microsoft GitHub ATT&CK Microsoft Security Prashant Mahajan ADRecon #Microsoft #ActiveDirectory #MITREATT&CK #Windows #mvpbuzz 👇👇 github.com/tomwechsler/Ac…





"Microsoft Signed my Malware" Doug Bienstock (Jared Wilson), Mandiant Jared Wilson (Doug Bienstock) , Mandiant Barry Vengerik (BarryV), Mandiant 14/15


Our #CTI World Watch (OCD) team just updated their #ransomware families tree. This 26th version includes many newcomers as well as updated relationships.🧐 Again, feel free to share your feedback! ➡️github.com/cert-orangecyb… Mar_Pich Orange Cyberdefense #rebrand



As far as pivoting is concerned in CTI, you can pretty much do it all between VirusTotal, Censys & urlscan.io 🐧 I have taken all Artifact types and their features from the Awesome Pivot Atlas maintained by Amitai Cohen & mapped it against sources & where to find them Links ⬇️