World Watch (OCD)
@worldwatch_ocd
World Watch CTI team from @CERTcyberdef (@OrangeCyberDef)
ID: 1371496188889939969
https://research.cert.orangecyberdefense.com/ 15-03-2021 16:19:34
39 Tweet
77 Followers
409 Following




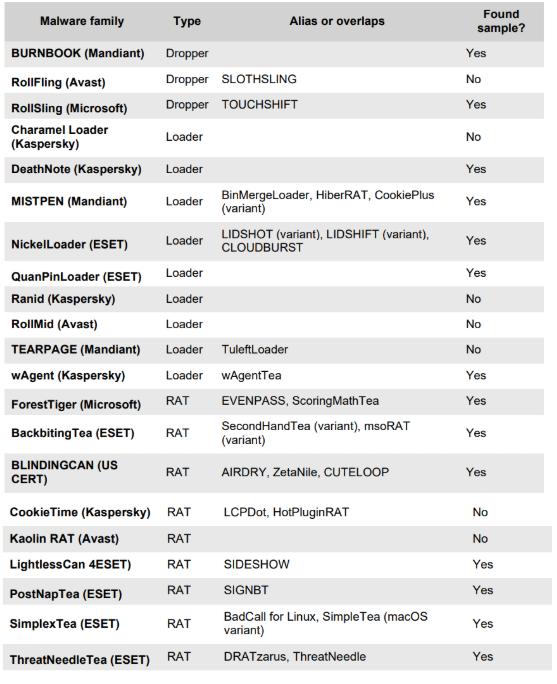
New NailaoLocker ransomware used against EU healthcare orgs - Bill Toulas bleepingcomputer.com/news/security/… bleepingcomputer.com/news/security/…





Happy to join the 2025-2026 Virtual Routes European Cybersecurity Fellowship 🇪🇺☺️


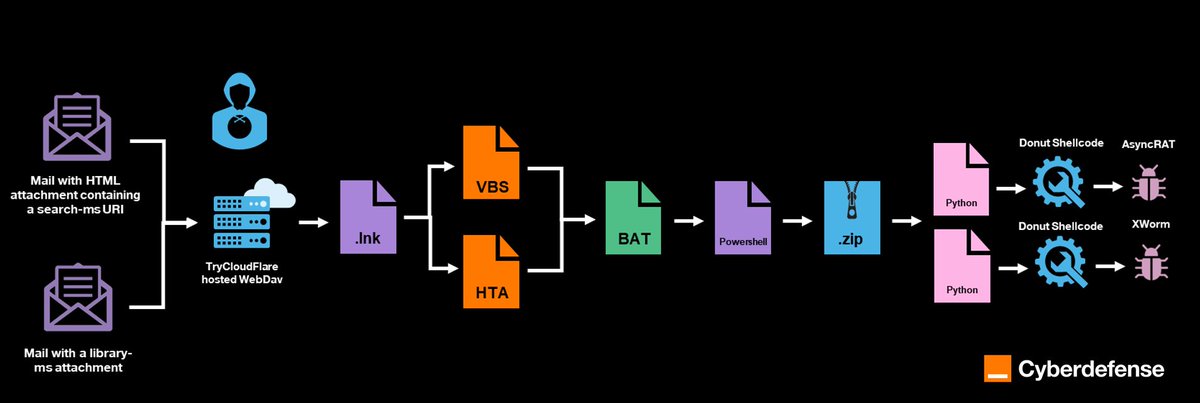
🆕 Just released a blogpost on a #Sorillus RAT campaign our CERT Orange Cyberdefense observed in March. Likely 🇧🇷 threat actors, use of numerous tunneling services like ngrok[.]app, ngrok[.]dev, ngrok[.]pro, localto[.]net, ply[.]gg, campaign still active… ➡️ orangecyberdefense.com/global/blog/ce…
![Mar_Pich (@mar_pich) on Twitter photo 🆕 Just released a blogpost on a #Sorillus RAT campaign our <a href="/CERTCyberdef/">CERT Orange Cyberdefense</a> observed in March.
Likely 🇧🇷 threat actors, use of numerous tunneling services like ngrok[.]app, ngrok[.]dev, ngrok[.]pro, localto[.]net, ply[.]gg, campaign still active…
➡️ orangecyberdefense.com/global/blog/ce… 🆕 Just released a blogpost on a #Sorillus RAT campaign our <a href="/CERTCyberdef/">CERT Orange Cyberdefense</a> observed in March.
Likely 🇧🇷 threat actors, use of numerous tunneling services like ngrok[.]app, ngrok[.]dev, ngrok[.]pro, localto[.]net, ply[.]gg, campaign still active…
➡️ orangecyberdefense.com/global/blog/ce…](https://pbs.twimg.com/media/GtvhD8yWcAAc1df.jpg)