Aiden Mitchell
@amitchell516
Moved to threads.net/@amitchell516
ID: 1468466465409961985
https://aiden.lgbt 08-12-2021 06:24:32
375 Tweet
87 Followers
1,1K Following



This is so sick. Email -> Attached EML -> Embedded image -> OCR -> NLU to identify a financial request. Outlook/many clients will render an attached EML in the *original* message, making this an effective evasion technique. We've seen this in the wild recently. h/t Aiden Mitchell
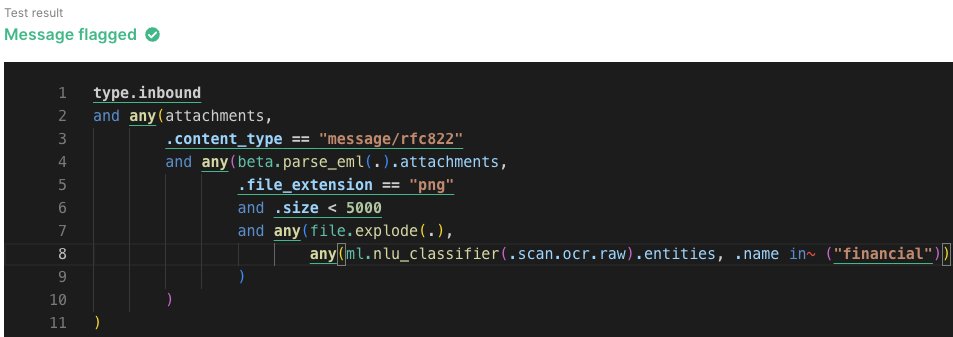








EML attachments are a clever way to bypass traditional analysis because they automatically get rendered and embedded in the original message, without user interaction, by most mail clients: sublime.security/blog/hidden-cr… h/t Aiden Mitchell