Ahsan Sheikh
@snshyk
Bug Hunter | Synack Red Team Member | Security Consultant | CEH
ID: 1242851834156417026
25-03-2020 16:32:44
120 Tweet
491 Followers
243 Following








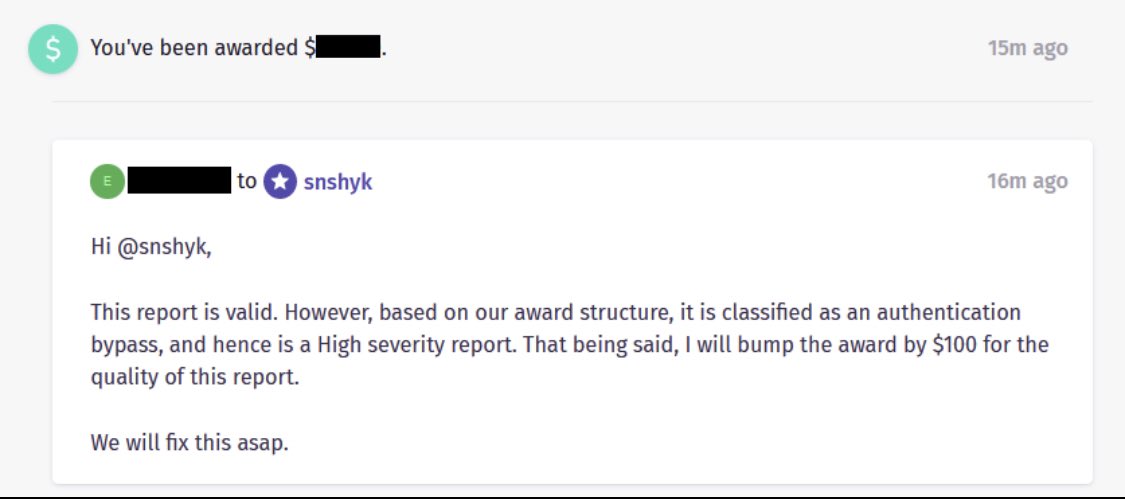
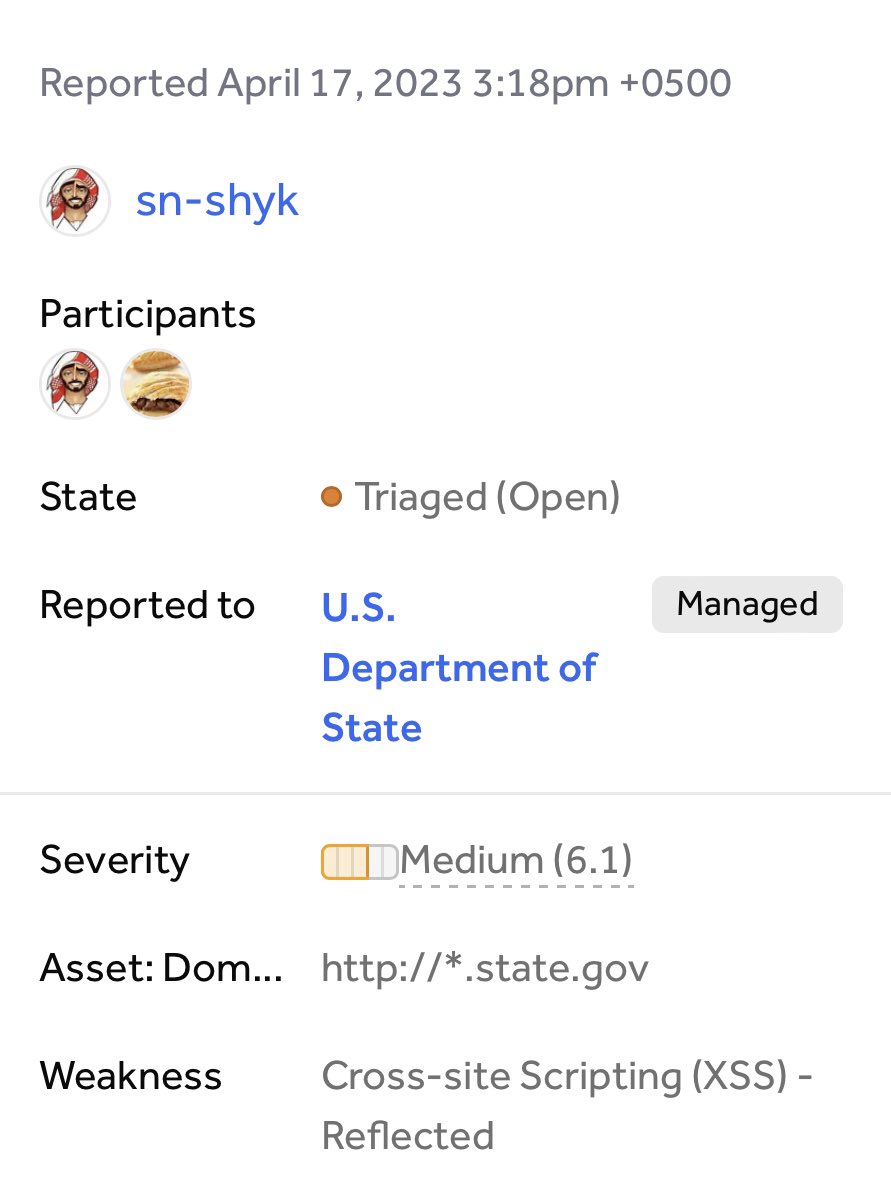
Vulnerability accepted! Department of State Vulnerability: Reflected XSS Tip: Try second or third level URL encoding if application won’t allow you to use simple XSS payload. #infosec #CyberSecurity









Godfather Orwa 🇯🇴 Eslam Salem 3️⃣ We Hacked Apple for 3 Months: Here’s What We Found A classic write-up by 5 talented researchers that briefly talked about their experience hacking Apple for 3 months! samcurry.net/hacking-apple

Th3g3nt3lman 5️⃣ Write-up: AWS Document Signing Security Control Bypass Ozgur shares a cool way of abusing application logic to bypass AWS Document Signing! ozguralp.medium.com/write-up-aws-d…