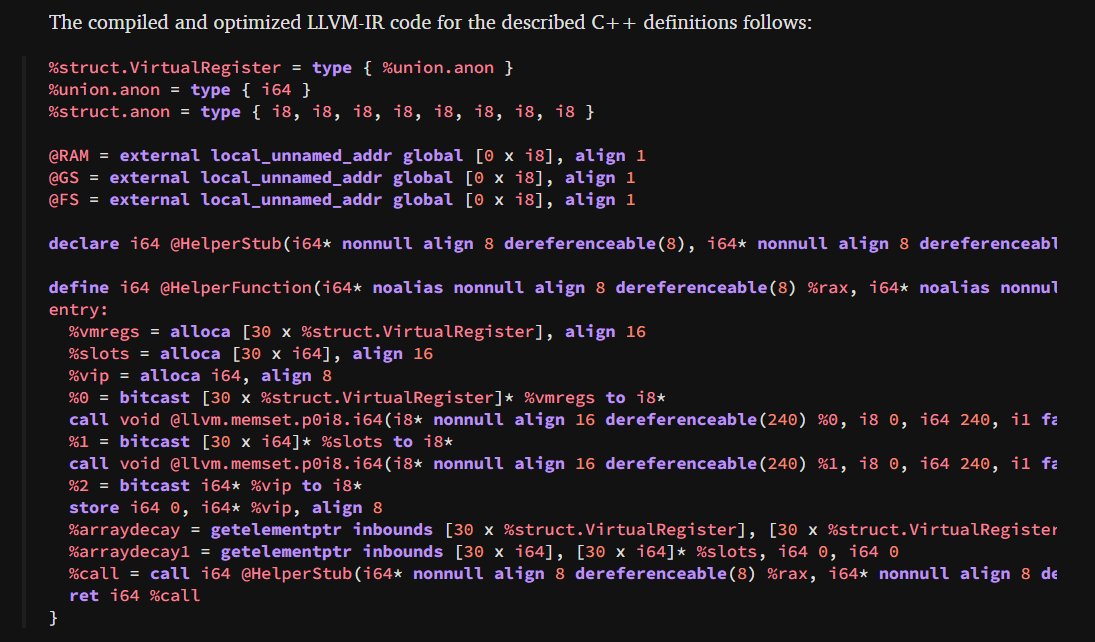
Daniel Jary
@janieldary
Security researcher
ID: 1429795320993562627
https://github.com/JanielDary 23-08-2021 13:20:32
55 Tweet
140 Followers
356 Following



In my new blog for Check Point Research I propose a new injection technique, using the Thread Name API - check it out! 💙

At #VB2024 Daniel Jary will dig into techniques used to maliciously load Shared Objects & describe ways to detect them. He'll present a tool that identifies SO injection, shellcode injection, process hollowing &entry point manipulation of running processes virusbulletin.com/conference/vb2…





Virus Bulletin (VB) just released my talk & white paper on Shared Object injection & detection on Linux. Pleasure to be invited & attend. Great conference guys! Virus Bulletin #VB #VirusBulletin #Linux virusbulletin.com/conference/vb2… youtube.com/watch?v=x6pHvr…


I created a hypervisor-based emulator for Windows x64 binaries. This project uses Windows Hypervisor Platform to build a virtualized user-mode environment, allowing syscalls and memory accesses to be logged or intercepted. elastic.co/security-labs/… Project: github.com/x86matthew/Win…




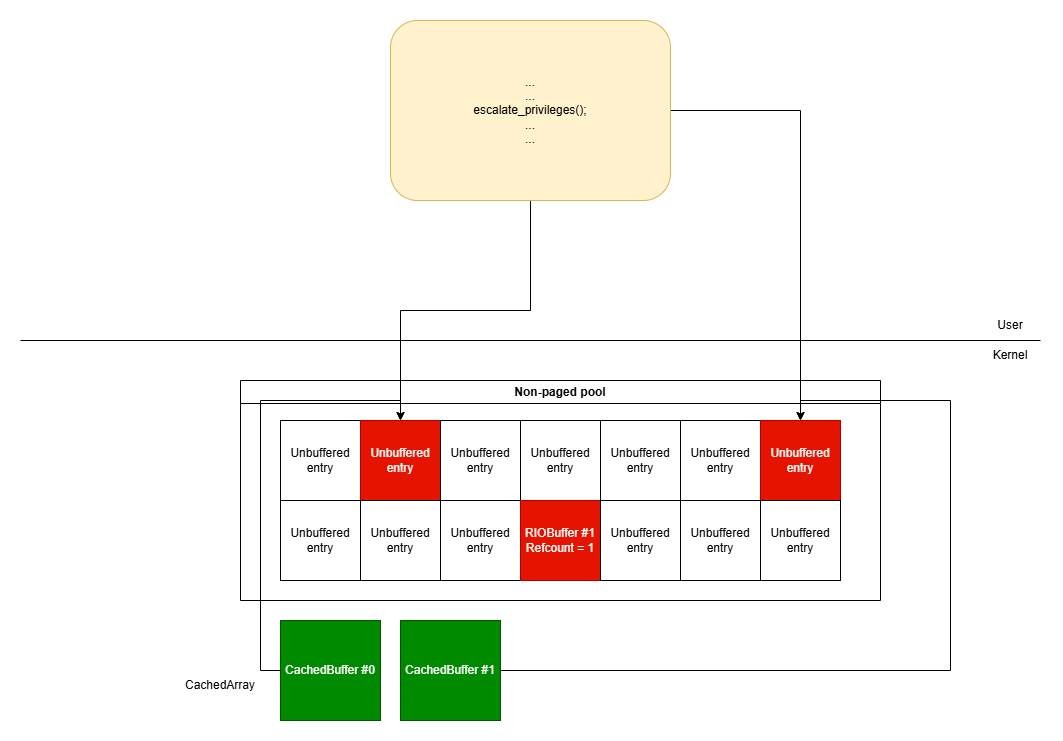
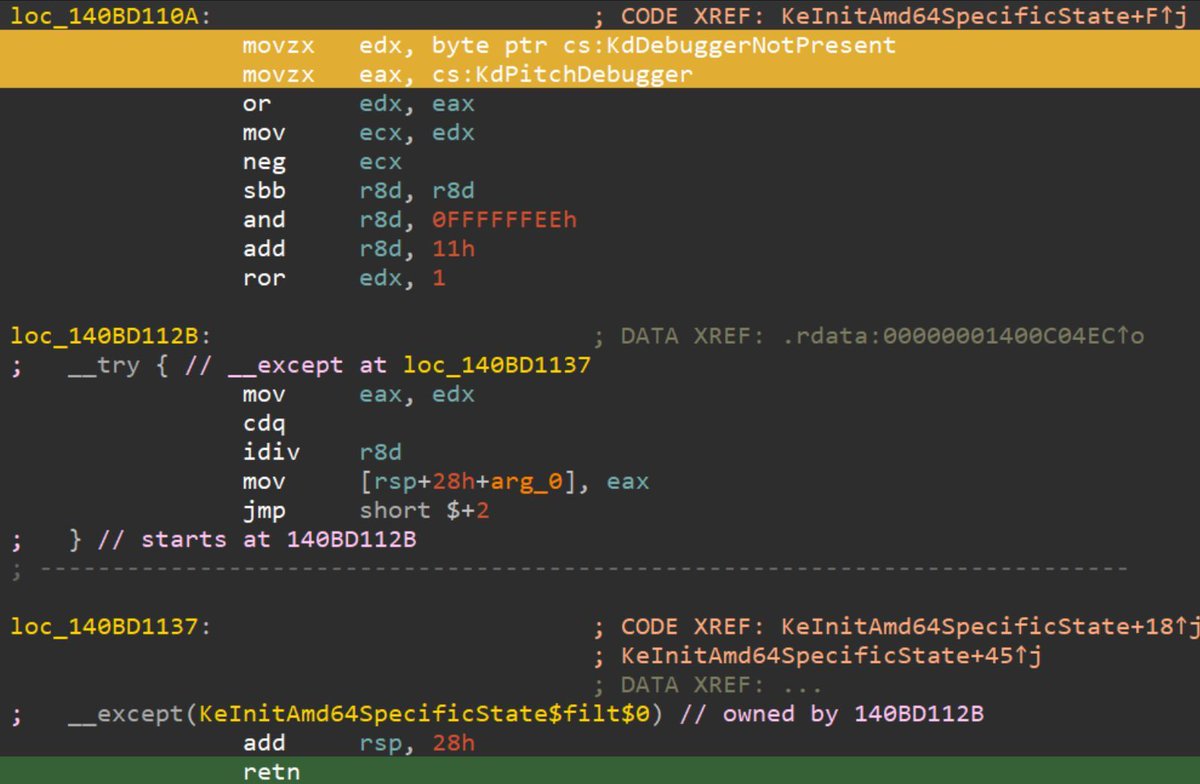
Thread Execution Hijacking is one of the well-known methods that can be used to run implanted code. In this blog we introduce a new injection method, that is based on this classic technique, but much stealthier - Waiting Thread Hijacking. Read More : research.checkpoint.com/2025/waiting-t…