Yoroi Malware Z-Lab
@zlab_team
Z-Lab - The @yoroisecurity malware research team
Yomi Sandbox - yomi.yoroi.company/upload
ID: 1087671979346481156
https://yoroi.company/category/research/ 22-01-2019 11:23:02
374 Tweet
767 Takipçi
163 Takip Edilen

Another excellent analysis by @TelsyTRT Emanuele De Lucia OPERATION “SPACE RACE”: REACHING THE STARS THROUGH PROFESSIONAL SOCIAL NETWORKS telsy.com/operation-spac… Malware Patrol Denis O'Brien Antonio Pirozzi
Dee TG Soft Pierluigi Paganini - Security Affairs another azorult c2 login panel @ zi-chem.]co/PL342/panel/admin.php ip 217.195.154.94🇳🇱 shock hosting blacklisted on CyberCrime-Tracker VT: 8/80 INV05390 Document 56.exe signed by CN bazaar.abuse.ch/sample/fe86c6a… panel stats and authenticode
![Antonio Pirozzi (@_antoniopirozzi) on Twitter photo <a href="/ViriBack/">Dee</a> <a href="/VirITeXplorer/">TG Soft</a> <a href="/securityaffairs/">Pierluigi Paganini - Security Affairs</a>
another azorult c2 login panel @
zi-chem.]co/PL342/panel/admin.php
ip 217.195.154.94🇳🇱 shock hosting
blacklisted on CyberCrime-Tracker
VT: 8/80
INV05390 Document 56.exe
signed by CN
bazaar.abuse.ch/sample/fe86c6a…
panel stats and authenticode <a href="/ViriBack/">Dee</a> <a href="/VirITeXplorer/">TG Soft</a> <a href="/securityaffairs/">Pierluigi Paganini - Security Affairs</a>
another azorult c2 login panel @
zi-chem.]co/PL342/panel/admin.php
ip 217.195.154.94🇳🇱 shock hosting
blacklisted on CyberCrime-Tracker
VT: 8/80
INV05390 Document 56.exe
signed by CN
bazaar.abuse.ch/sample/fe86c6a…
panel stats and authenticode](https://pbs.twimg.com/media/EkpvHxIWkAATSVQ.jpg)

Our report on #kimsuky #apt cited by us-cert in an advisory coauthored by FBI USCYBERCOM Cybersecurity Alert Cybersecurity and Infrastructure Security Agency.. references n.36 and 37.. Yoroi Malware Z-Lab Yoroi Antonio Pirozzi Marco Ramilli lc4m
[ALERT] #smishing campaign against Intesa Sanpaolo customers.. - some non legit domains registered between 2020-10-22 and 2020-1-25.. - non legit certificate created (fingerprint in the screen) Francesco Bussoletti Cert AgID Gianni Amato Pierluigi Paganini - Security Affairs TG Soft
![Antonio Pirozzi (@_antoniopirozzi) on Twitter photo [ALERT] #smishing campaign against <a href="/intesasanpaolo/">Intesa Sanpaolo</a> customers..
- some non legit domains registered between 2020-10-22 and 2020-1-25..
- non legit certificate created (fingerprint in the screen)
<a href="/FBussoletti/">Francesco Bussoletti</a>
<a href="/AgidCert/">Cert AgID</a>
<a href="/guelfoweb/">Gianni Amato</a>
<a href="/securityaffairs/">Pierluigi Paganini - Security Affairs</a>
<a href="/VirITeXplorer/">TG Soft</a> [ALERT] #smishing campaign against <a href="/intesasanpaolo/">Intesa Sanpaolo</a> customers..
- some non legit domains registered between 2020-10-22 and 2020-1-25..
- non legit certificate created (fingerprint in the screen)
<a href="/FBussoletti/">Francesco Bussoletti</a>
<a href="/AgidCert/">Cert AgID</a>
<a href="/guelfoweb/">Gianni Amato</a>
<a href="/securityaffairs/">Pierluigi Paganini - Security Affairs</a>
<a href="/VirITeXplorer/">TG Soft</a>](https://pbs.twimg.com/media/El1HjxYXUAE7hL4.png)

An interesting analysis made by Yoroi Yoroi Malware Z-Lab on the new #UNC1945 (Mandiant (part of Google Cloud) ) spotted on 🇮🇹 Infrastructures. Catalin Cimpanu MalwareHunterTeam BleepingComputer Odisseus @arturodicorinto @malwaremustd1e yoroi.company/research/shado…
Thanks FortiGuard Labs for citing us for our discovery! fortinet.com/blog/threat-re… #malware #jsoutprox MalwareHunterTeam Yoroi James Bl4ng3l @hexfati lc4m Luigi Martire
Dissecting #STEELCORGI 🔥🔥🔥: Our last analysis about another piece of the #UNC1945 arsenal! yoroi.company/research/openi… @FireEye @Bank_Security MalwareHunterTeam Yoroi Yoroi Malware Z-Lab JAMESWT_MHT Pierluigi Paganini - Security Affairs James TG Soft Malware Patrol

Yoroi (Yoroi Malware Z-Lab ) on dissecting a #lockBit #exfil tool and #hunting the gang exfiltration infrastructure. lc4m Luigi Martire MalwareHunterTeam f_462_958 Mikhail Kasimov Odisseus Securityblog R. Catalin Cimpanu yoroi.company/research/hunti…

Decine di aziende manifatturiere italiane vittime di una serie di attacchi che infettano i sistemi informatici con finti documenti Office e Excel attraverso la botnet #Dridex Grazie Agi Agenzia Italia per aver segnalato il lavoro del Yoroi Malware Z-Lab #Yoroi agi.it/cronaca/news/2…


#threatactors are evolving their techniques. So we began a tracking adventure to spot new #ioc and to map their evolution over time. New IoC available 👇👇 yoroi.company/research/serve… lc4m Emanuele De Lucia JAMESWT_MHT James Yoroi Yoroi Malware Z-Lab

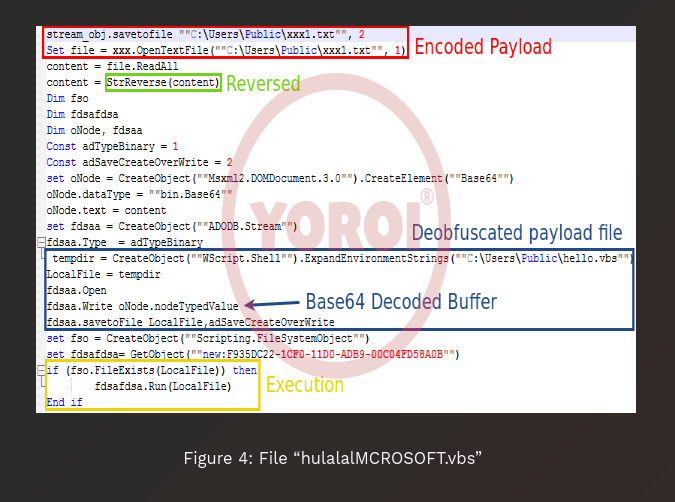
The #Yoroi Yoroi Malware Z-Lab is tracking the threat actor Aggah (TH-157) since 2019 along with PaloAlto UNIT42, HP and Juniper Networks, revealing a structured information stealing infrastructure, a campaign capable of quickly varying its distribution technique. yoroi.company/research/serve…



The Yoroi Yoroi Malware Z-Lab did a deep dive into the #BlueSky ransomware, providing a technical analysis of the #ransomware payload. #CyberSecurity #InfoSec #malware CVSoci.al/AToqc19m



Che sorpresa scoprire che il report del nostro Yoroi Malware Z-Lab su VETTALoader viene citato da Mandiant (part of Google Cloud) ! Yoroi è molto orgogliosa di questo riconoscimento a livello internazionale. 👉 Vedi l'articolo di Mandiant 👉mandiant.com/resources/blog… Marco Ramilli Luigi Martire
![Antonio Pirozzi (@_antoniopirozzi) on Twitter photo multiple C2 panel on 5.9.239.131
DT-Stealer: https://lodergord.]com/login.php
(credits by deity.developer]at]thesecure.]biz)
Azorult on 5.9.239.131/azorme/panel/admin.php
mainly targeting GB,US and RU..
also DarkSky..
<a href="/Hetzner_Online/">Hetzner</a>
<a href="/securityaffairs/">Pierluigi Paganini - Security Affairs</a>
<a href="/VirITeXplorer/">TG Soft</a> multiple C2 panel on 5.9.239.131
DT-Stealer: https://lodergord.]com/login.php
(credits by deity.developer]at]thesecure.]biz)
Azorult on 5.9.239.131/azorme/panel/admin.php
mainly targeting GB,US and RU..
also DarkSky..
<a href="/Hetzner_Online/">Hetzner</a>
<a href="/securityaffairs/">Pierluigi Paganini - Security Affairs</a>
<a href="/VirITeXplorer/">TG Soft</a>](https://pbs.twimg.com/media/EksqoiKXUAISHE7.jpg)