Константин
@z3jpa29z
ID: 1158297972708392960
05-08-2019 08:45:31
74 Tweet
28 Followers
71 Following





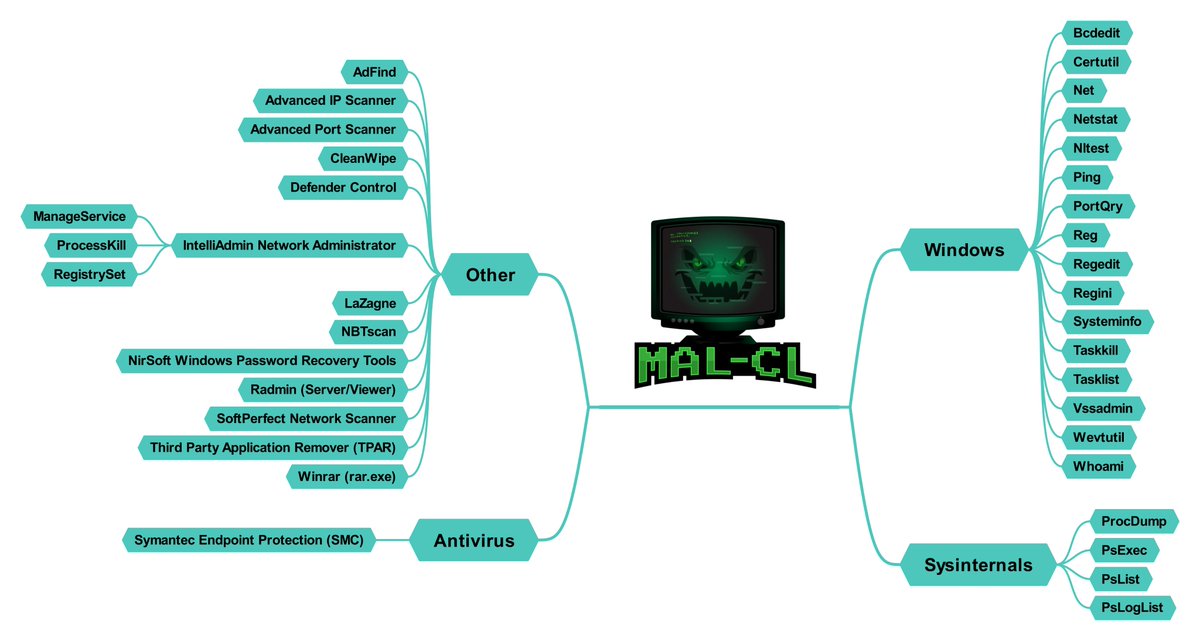
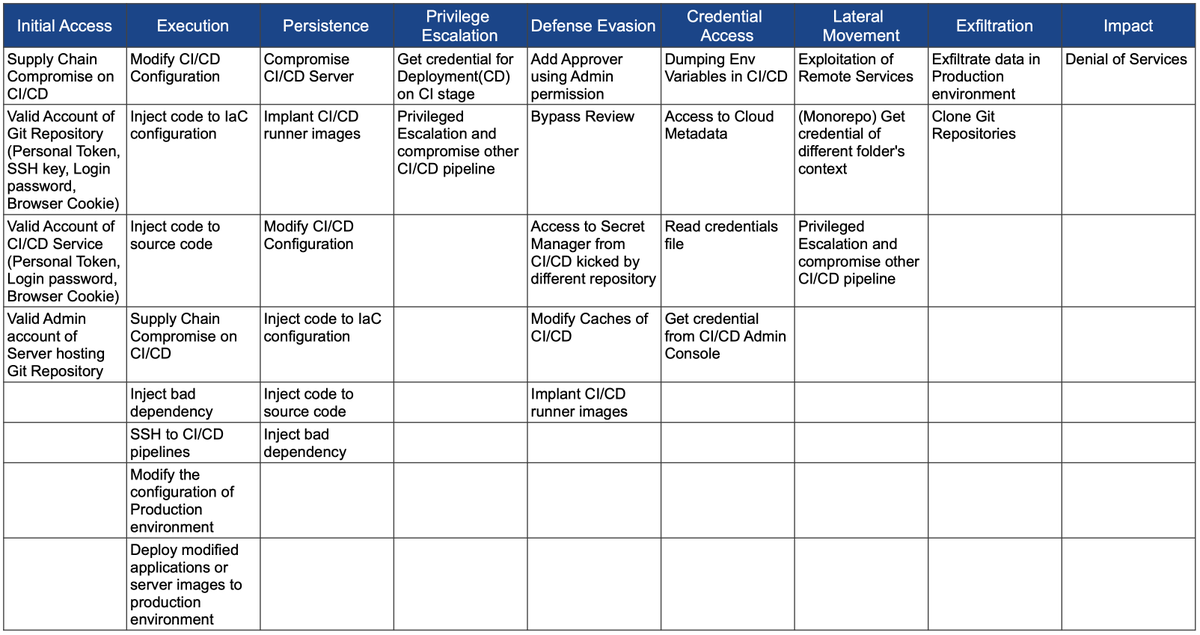
TTPs for compromising CI/CD pipelines, by Hiroki (rung) SUEZAWA github.com/rung/threat-ma…





📌Hunting for Persistence in #Linux (Part 1): Auditd, #Sysmon, #Osquery, and Webshells ➡️pberba.github.io/security/2021/… Author: Pepe Berba 🔥 #threathunting #blueteam #redteam #DFIR #Security



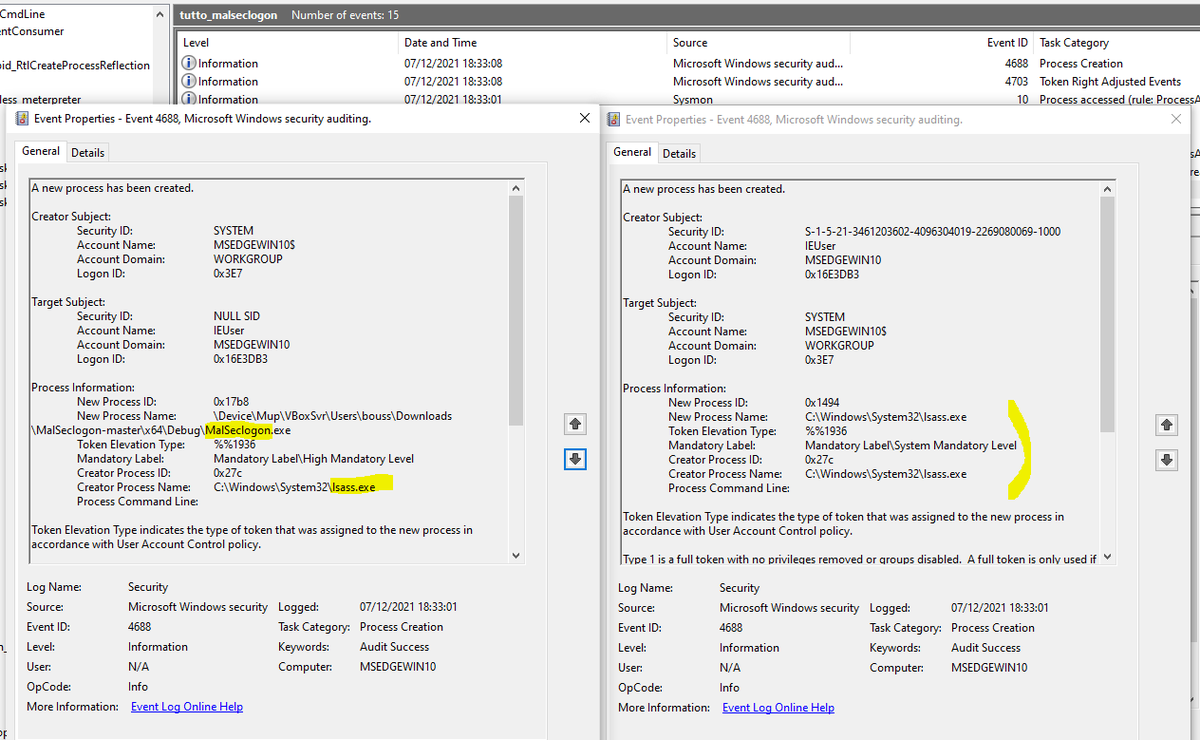
My small contribution to our teamwork. Thanks Metasploit Project for a fun weekend. #metasploitctf


So here are my 2 cents on Charlie Clark's CVE-2021-42287/CVE-2021-42278 Weaponization - a quick & dirty way to exploit it with Python and #impacket remotely. The renameMachine[.]py script is based on rbcd[.]py example by Charlie Bromberg « Shutdown »: gist.github.com/snovvcrash/3bf…
![sn🥶vvcr💥sh (@snovvcrash) on Twitter photo So here are my 2 cents on <a href="/exploitph/">Charlie Clark</a>'s CVE-2021-42287/CVE-2021-42278 Weaponization - a quick & dirty way to exploit it with Python and #impacket remotely. The renameMachine[.]py script is based on rbcd[.]py example by <a href="/_nwodtuhs/">Charlie Bromberg « Shutdown »</a>: gist.github.com/snovvcrash/3bf… So here are my 2 cents on <a href="/exploitph/">Charlie Clark</a>'s CVE-2021-42287/CVE-2021-42278 Weaponization - a quick & dirty way to exploit it with Python and #impacket remotely. The renameMachine[.]py script is based on rbcd[.]py example by <a href="/_nwodtuhs/">Charlie Bromberg « Shutdown »</a>: gist.github.com/snovvcrash/3bf…](https://pbs.twimg.com/media/FGQPpWUWUAIK611.jpg)