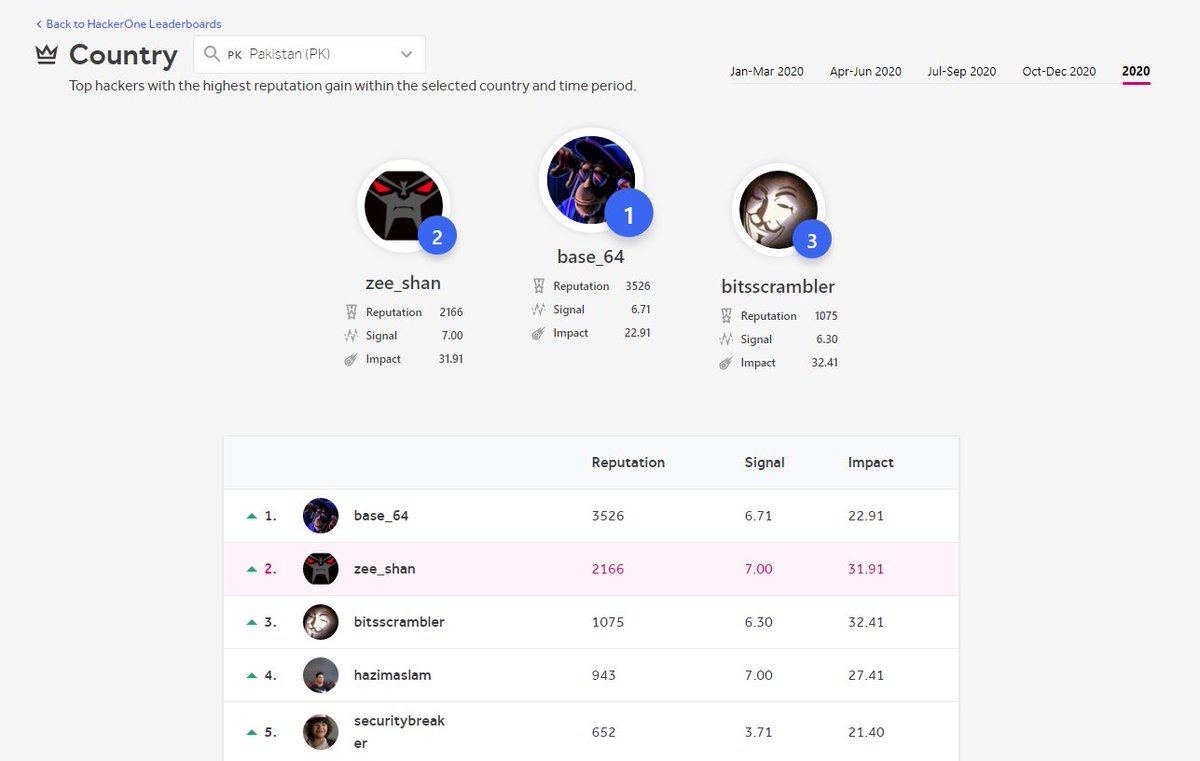
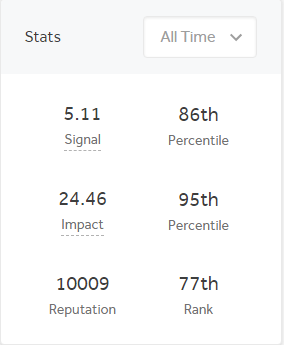
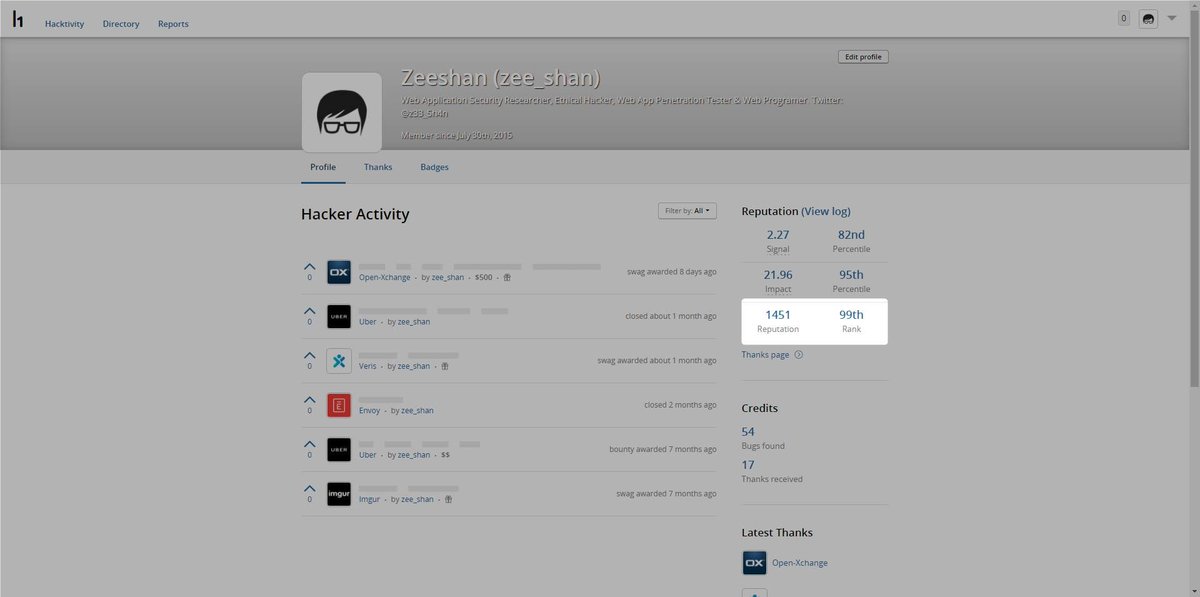
Zeeshan Khalid
@z33_5h4n
Ethical Hacker, Web Application Security Researcher & Web Programmer.
ID: 705968556333076480
http://zeeshankhalid.com 05-03-2016 04:09:54
124 Tweet
1,1K Followers
99 Following


#bugbounty #bugbountytips Automate sql injection 1.Browse all the application 2. Save all requests from burp to a file 3.Use github.com/Miladkhoshdel/… to automate . If WAF use github.com/m4ll0k/Atlas .thanks Hussein Daher for showing this. Thanks tool creators !!


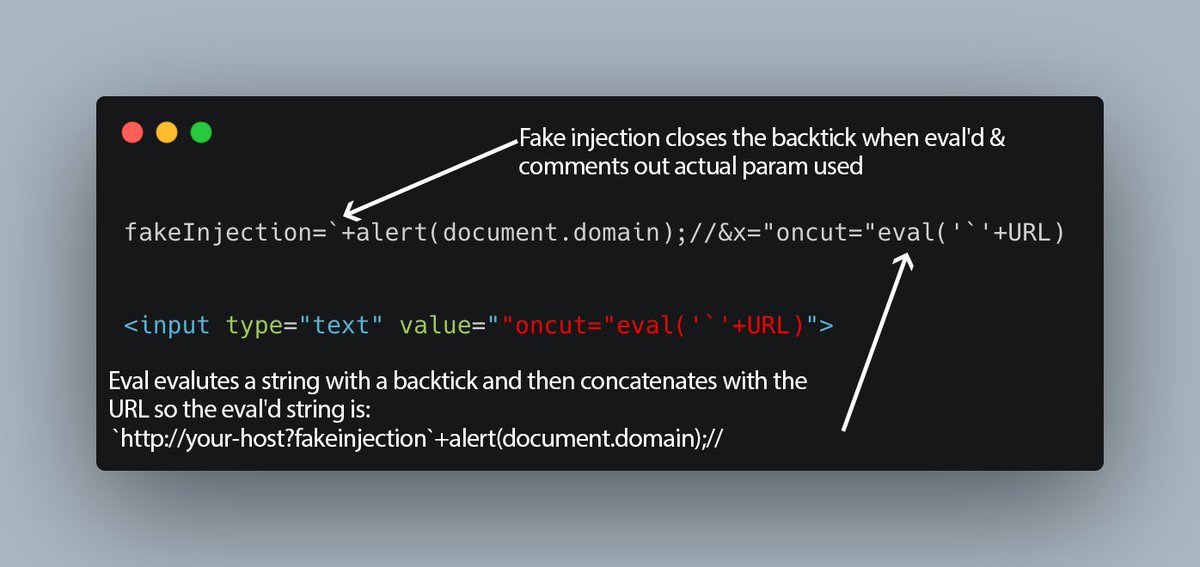
Here's an explanation of the wonderful vector by William Bowling that successfully solved one of our "impossible" labs. The original submission can be found here: jsfiddle.net/vakzz/g2two0qs/ The vector no longer works because the length restriction is reduced.


We've added a VueJS section to the XSS cheat sheet. With a new very short vector from Gareth Heyes \u2028 <x v-html=_c.constructor('alert(1)')()> also contains vectors from Cure53 and Eduardo Vela Sebastian Lekies koto portswigger.net/web-security/c…