
Joezid
@yossefzidann
Malware Analyst @EG_CERT
ID: 1025367307349045248
03-08-2018 13:06:31
140 Tweet
693 Followers
193 Following








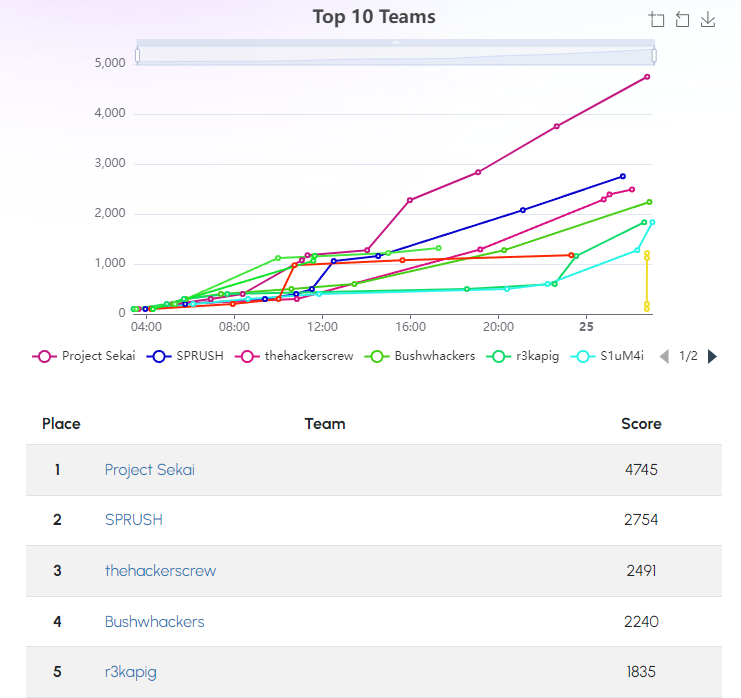
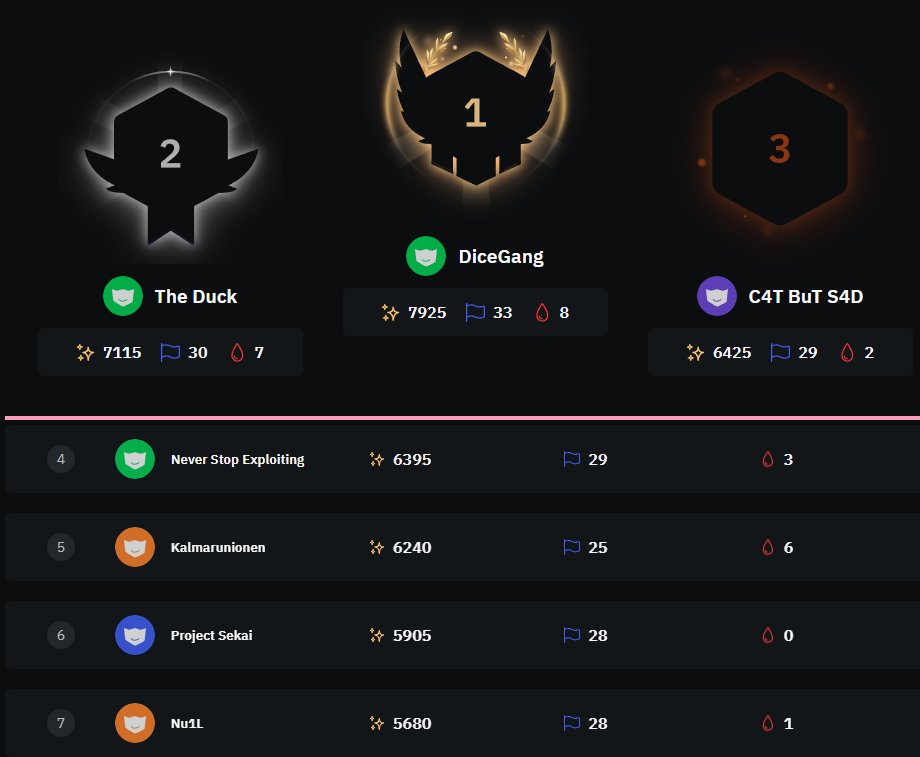
Thanks to Hack The Box for the wonderful event, we managed to clear all challenges and stay in Top 5 :)







Defeating #dotRunpeX — New #virtualized .NET injector abusing advanced techniques to deliver numerous malware families. CP<r> provides an in-depth analysis of this threat introducing several PoC techniques for reversing protected/virtualized #dotnet code. research.checkpoint.com/2023/dotrunpex…

Co-authoring Regexplore, a new volatility 3 plugin, with ChatGPT😄 to bring Registry Explorer plugins' Eric Zimmerman tool to Volatility. 🛠️ Contribute and help improve its features!: github.com/0xHasanM/regex… 🔗 #Volatility #DigitalForensics #RegistryExplorer #ChatGPT









![Georgy Kucherin (@kucher1n) on Twitter photo It turned out there are many more payloads used in the Notepad++ attack! To stay undetected, its masterminds were COMPLETELY changing execution chains about every month.
Here are more IPs used in the attack:
45.76.155[.]202
45.32.144[.]255
Read below for many other IoCs! [1/8] It turned out there are many more payloads used in the Notepad++ attack! To stay undetected, its masterminds were COMPLETELY changing execution chains about every month.
Here are more IPs used in the attack:
45.76.155[.]202
45.32.144[.]255
Read below for many other IoCs! [1/8]](https://pbs.twimg.com/media/HANLJTgXQAEx-rW.png)