yauv
@yauvme
just for fun
ID: 1592346311436558336
15-11-2022 02:42:48
1,1K Tweet
66 Followers
1,1K Following









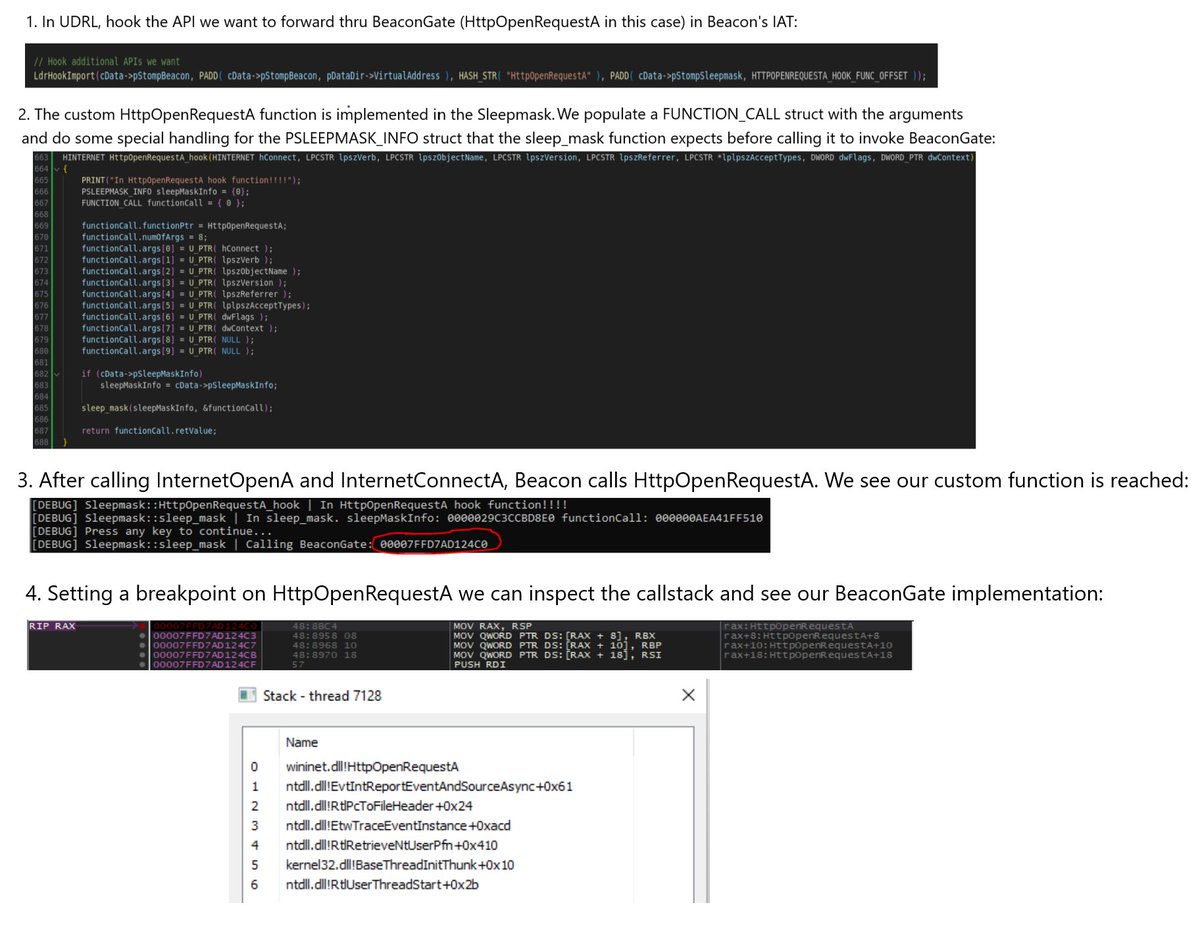
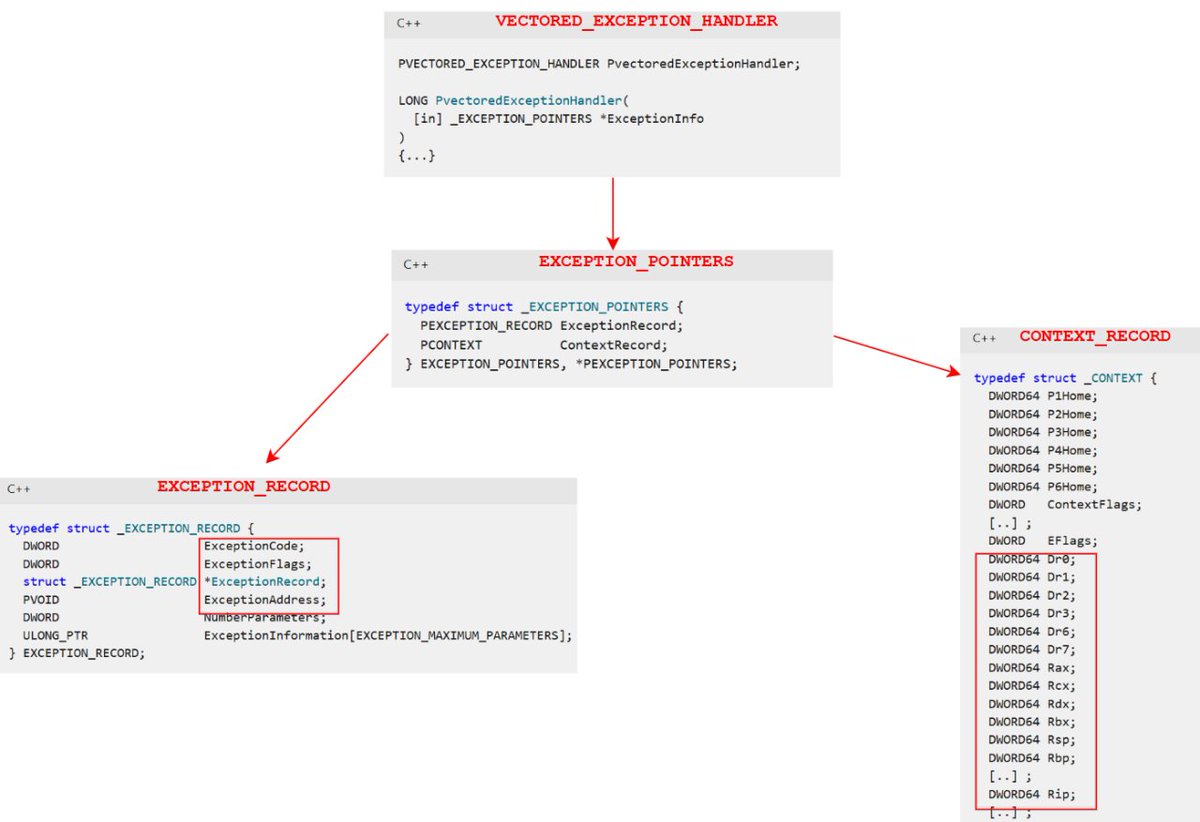
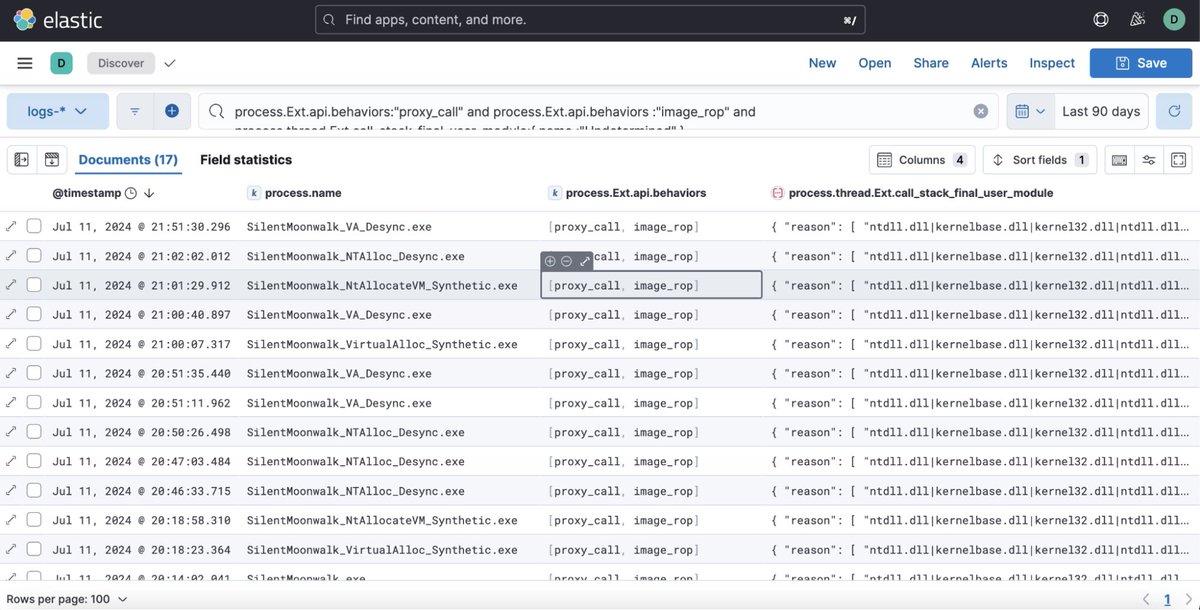
An increased visibility into threads' call stacks helps with more reliable malware detection. The approach is based on ETW telemetry and module's Export Directory data for information enrichment. A post by John Uhlmann of Elastic Security Labs. Great read! #redteam #blueteam #maldev





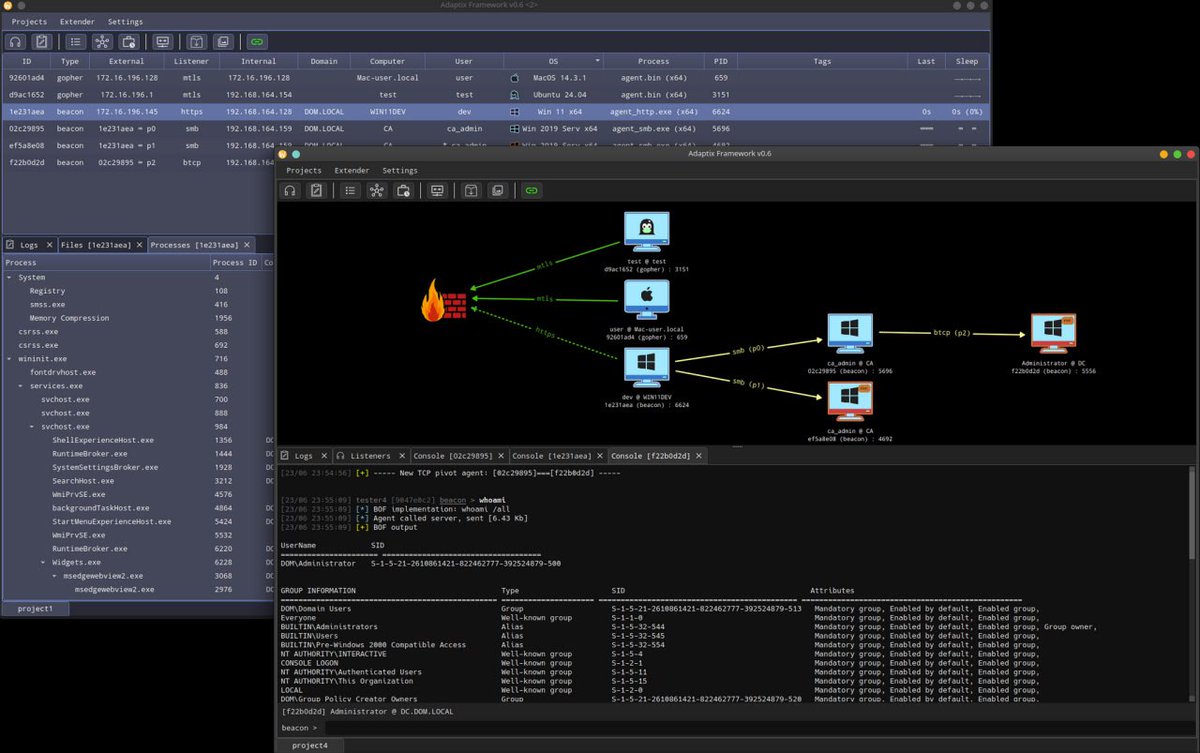
Introducing Havoc Professional: A Lethal Presence We’re excited to share a first look at Havoc Professional, a next-generation, highly modular Command and Control framework, and Kaine-kit our fully Position Independent Code agent engineered for stealth! infinitycurve.org/blog/introduct…