Jack Black, Jr
@xjrjackblack
ID: 1688799338938486784
08-08-2023 06:28:44
83 Tweet
15 Followers
252 Following










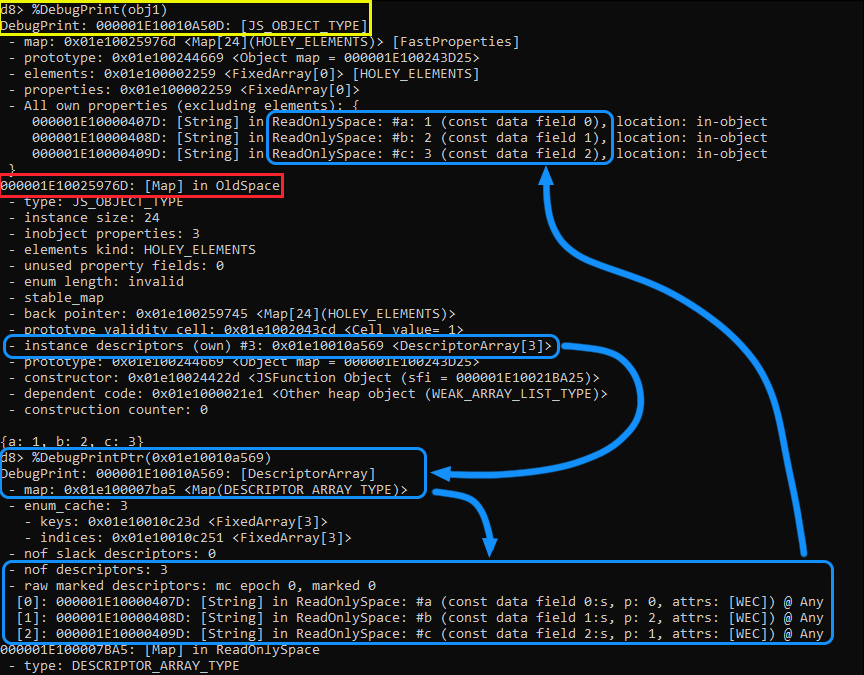
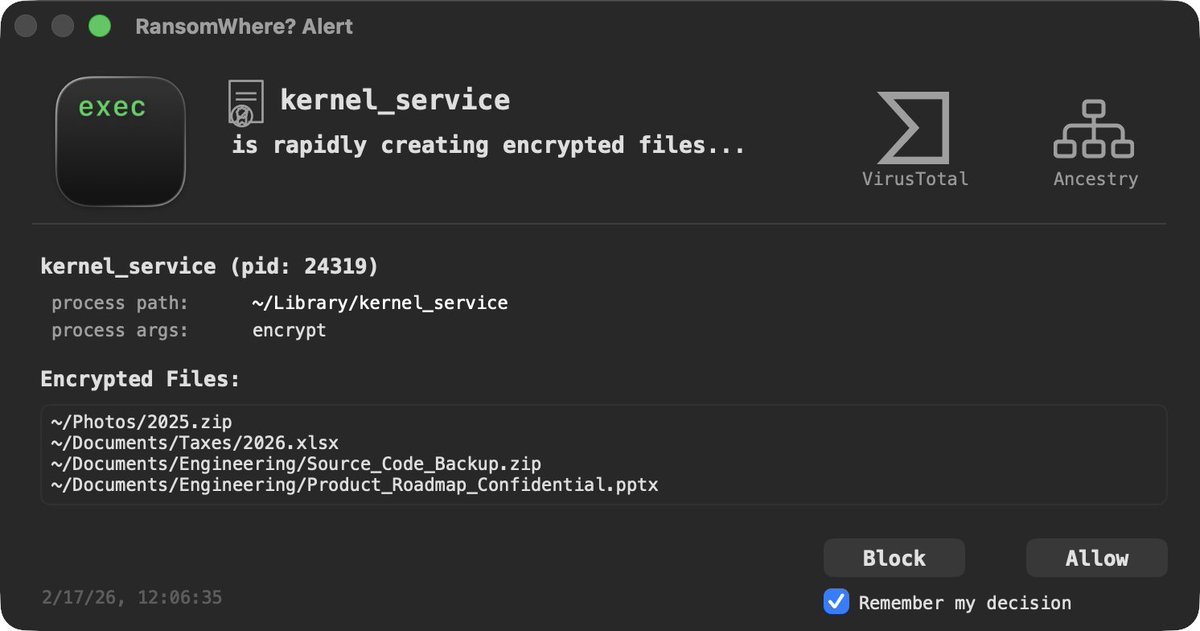
We take a closer look at the 2nd exploit, and sit down with Manfred Paul to learn about his research process. youtube.com/watch?v=NT1VCm…