Mohamed Ashraf
@x__junior
Detection @nextronsystems, Challenges Developer @CTFCreators, CTF Player @F1R3F411. Interested in #RE #Malware #Cryptography #WindowsInternals #DFIR.
ID: 1292714287216066561
https://x-junior.github.io/ 10-08-2020 06:48:04
145 Tweet
1,1K Followers
477 Following


[Blog 📚] LOLBINed - Abusing Sysinternals BgInfo nasbench.medium.com/lolbined-abusi… An additional abuse vector, for a #LOLBIN first discovered by Oddvar Moe #lolbas




Checkout our latest report written by Jonathan Peters and me



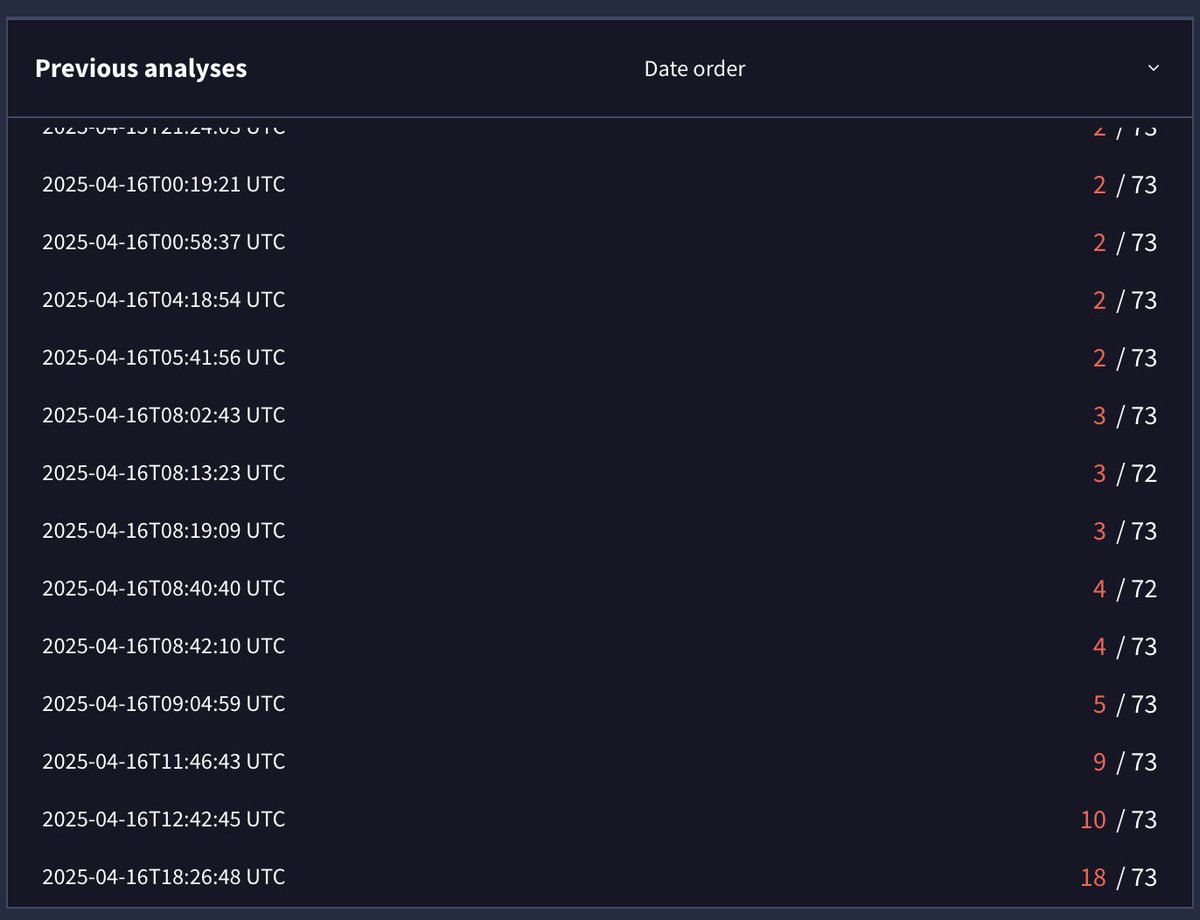
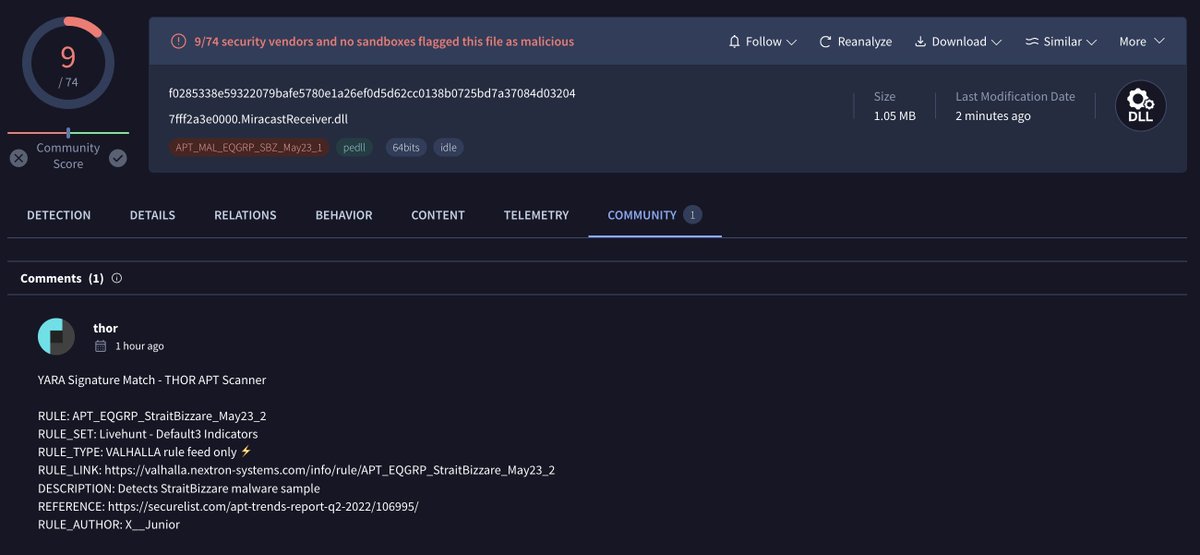
In case you're interested in EQGRP malware, you should take a look at this memory dump of an SBZ implant uploaded from Panama today Mohamed Ashraf and me wrote rules for it virustotal.com/gui/file/f0285…




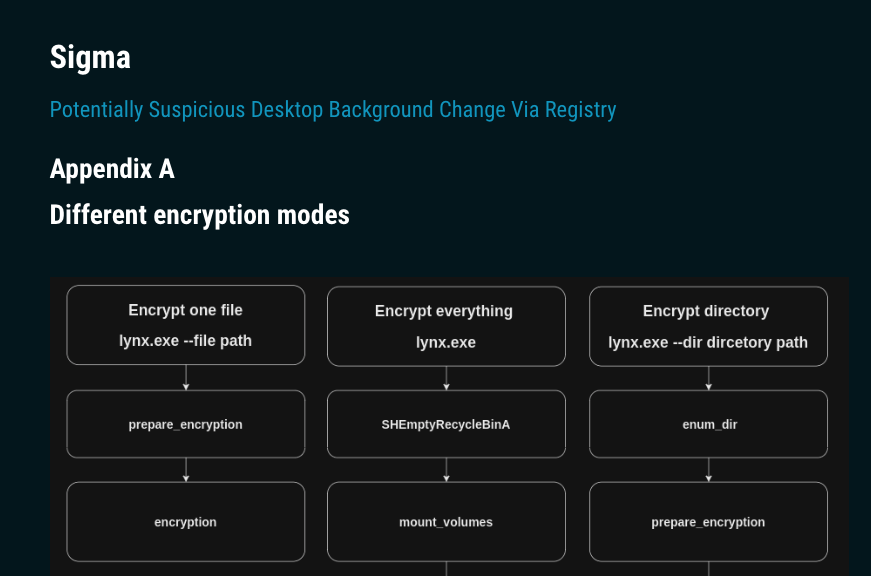
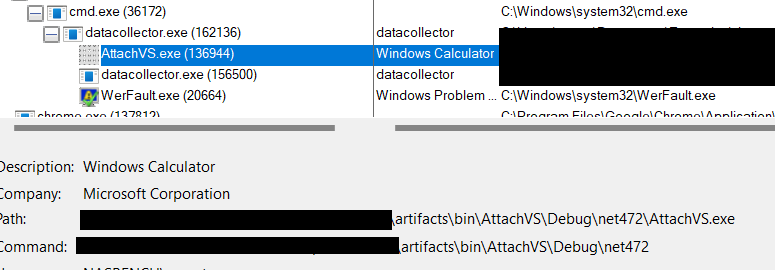
. Mohamed Ashraf from my team analyzed #Lynx ransomware and included a #YARA rule, IOCs and link to a Sigma rule that detects the activity