Security researcher, bug bounty hunter, employee of the month & owner at Offensi
ID: 880716657576079361
https://offensi.com 30-06-2017 09:16:28
915 Tweet
2,2K Followers
1,1K Following

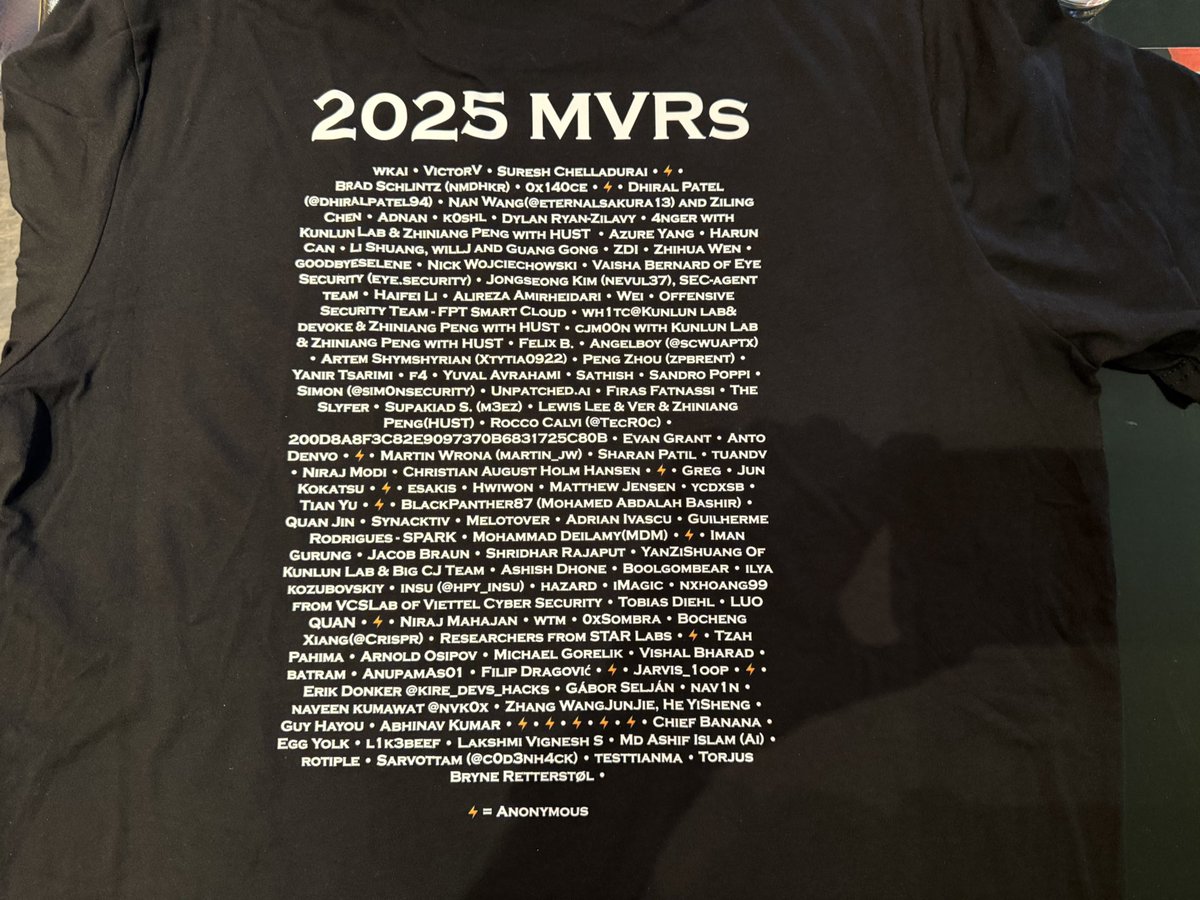
The MSRC team and I are excited up to connect and learn from security researchers and the community at Black Hat & DEF CON this week! If you spot me, I might have a shirt with your name on it. #blackhat2025 #blackhat #defcon Microsoft Security Response Center


Don’t post here much, but this one’s worth it. Managed to win the MVH award at the Google VRP (Google Bug Hunters) 0x0g bugSWAT event in Vegas 🤩


Amazing work! Congrats Dima! 👊🫶Dzmitry Lukyanenko


Thank you for the swag Microsoft Security Response Center ! Nice and soft sweater 😃💪🏻




Today was huge! Ciarán Cotter and I took 2nd place in the Google VRP (Google Bug Hunters) Mexico BugSwat and won Best AI VRP Researchers!


Wrapping up an amazing time at Google #bugSWAT Mexico 2025. It was a privilege meeting so many brilliant people including Ezequiel Pereira, Sreeram KL, Sivanesh Ashok and more. Thrilled that my report was featured in init.g and used to inspire students. That's truly rewarding.







New Google VRP writeup "Hacking Gemini: A Multi-Layered Approach" for a bounty of $20,000 by Valentino Massaro: buganizer.cc/hacking-gemini…