Alpy_yop🇵🇪
@who_4m1
Alpy_yop
ID: 205530383
21-10-2010 02:26:27
11,11K Tweet
140 Followers
1,1K Following













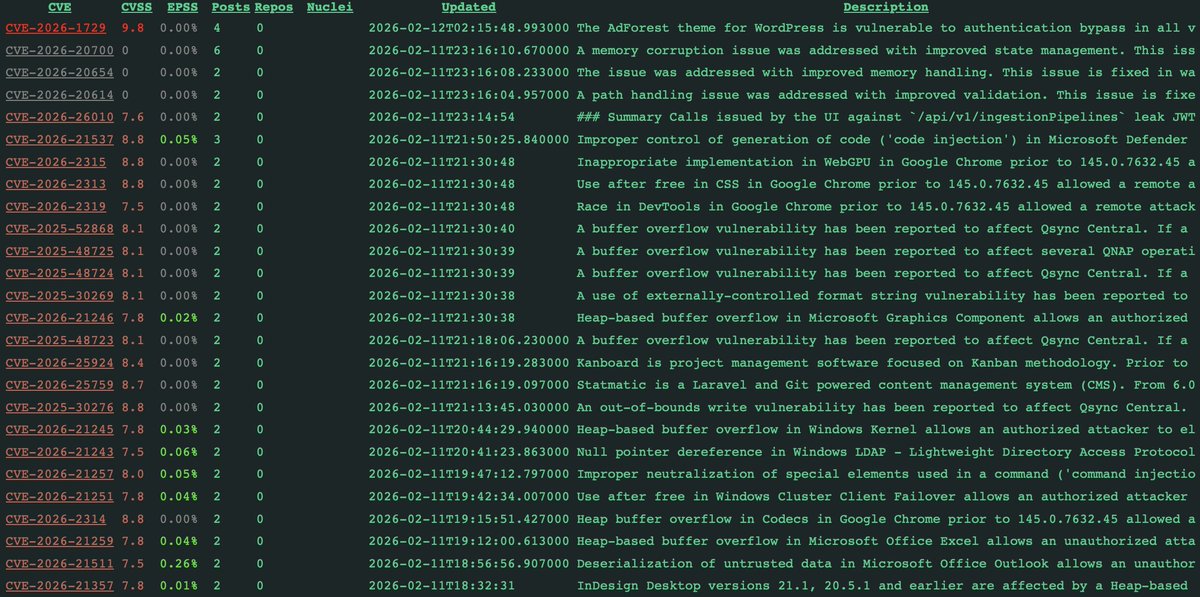
vx-underground PoC: github.com/dogukankurnaz/…