Samuel Chevet
@w4kfu






New blog post! A bug in GTA San Andreas lay dormant for over 20 years, until unrelated changes in Windows 11 24H2 triggered it. This is a deep dive into how a simple coding mistake erased all seaplanes from the game and made them completely unusable. cookieplmonster.github.io/2025/04/23/gta…

TyphoonCon🌪️ is already over, but we enjoyed every minute ! During our talk "Journey To Freedom", we disclosed for the first time the details on the Windows LPE we used at Pwn2Own Vancouver 2024 after escaping from VirtualBox. Slides are already available: reversetactics.com/publications/2…


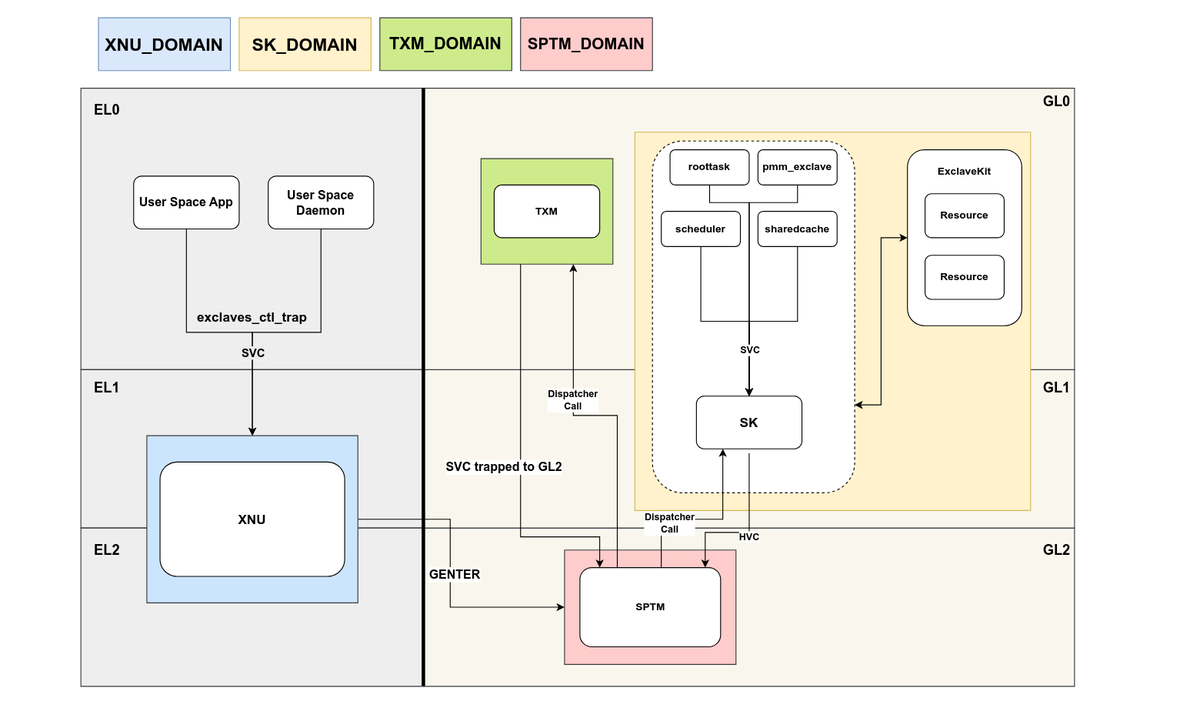
🔺iPhone models announced today include Memory Integrity Enforcement, the culmination of an unprecedented design and engineering effort that we believe represents the most significant upgrade to memory safety in the history of consumer operating systems. security.apple.com/blog/memory-in…