Phish Stix
@stixphish
Just a phish
ID: 1620880360136445966
01-02-2023 20:23:04
38 Tweet
13 Takipçi
292 Takip Edilen

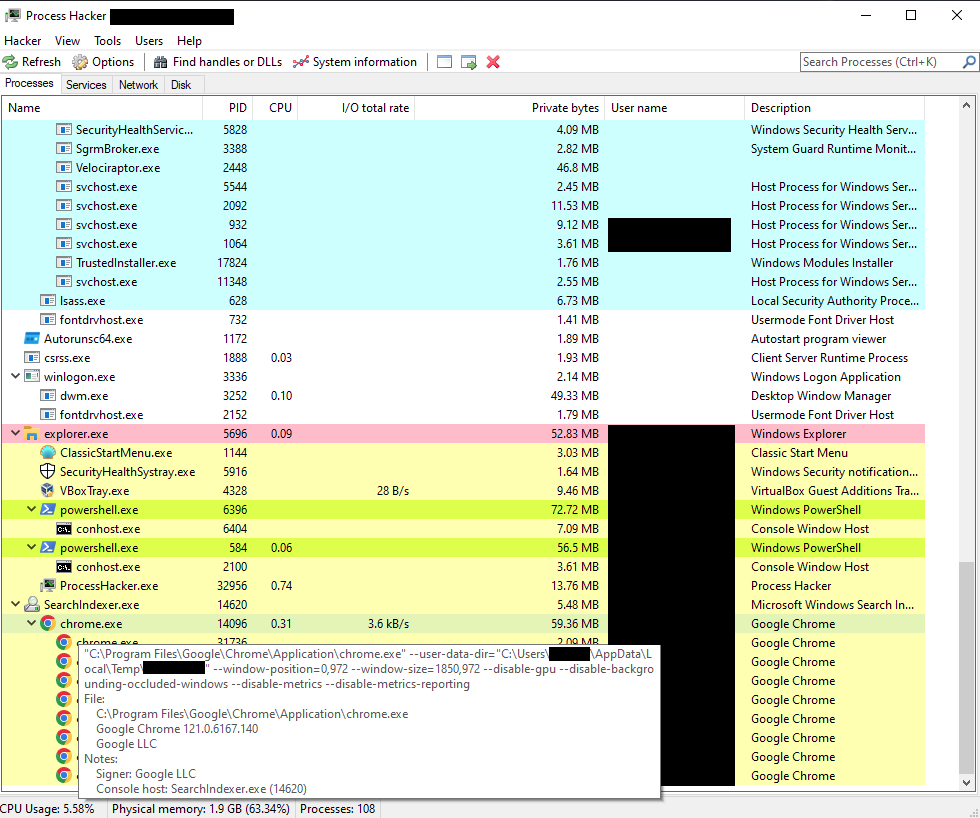
🚨New Report🚨 #Akira: The Old-New Style Crime by Joshua Penny & me Research based on methodology, versions of public #malware, all #CTI and detection opportunities of #TA 🔗Full report: rexorvc0.com/2024/06/19/Aki… #RE #intel #ransomware #TA