tlk
@tlk___
ID: 139346030
02-05-2010 09:27:52
649 Tweet
796 Followers
1,1K Following













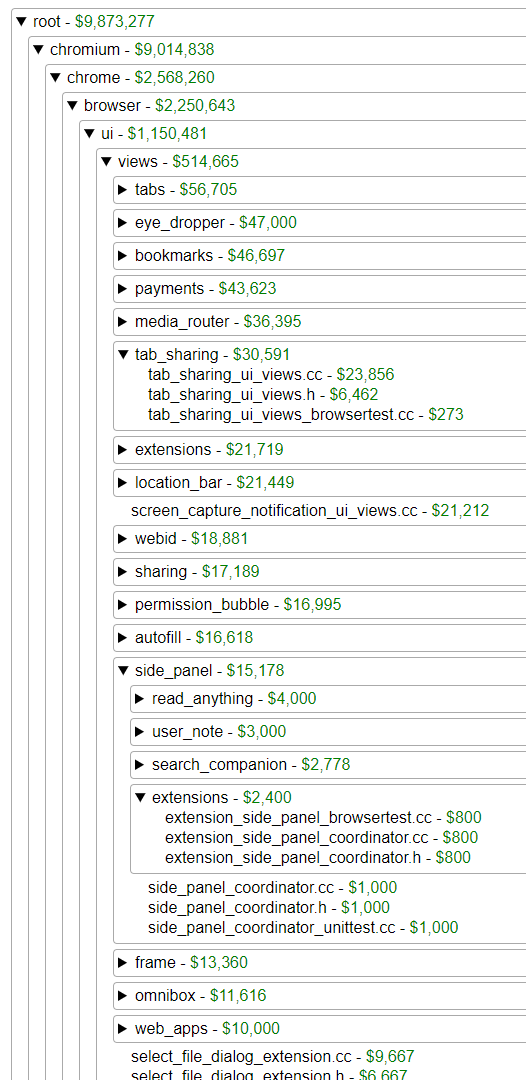
[Pwn2Own 2024](CVE-2024-2886)[330563095, 330575496] PinArrayBufferContent is insufficient to keep the backing store itself pinned and WebCodecs VideoFrame Race Condition UAF W -> RCE is now public with PoC, exploit and wp. issues.chromium.org/issues/3305754… issues.chromium.org/issues/3305630… Xion