Thierry Franzetti
@thierryfranzett
Security oriented, I like to understand how things work on Windows. A bit of reversing, a bit of ethical hacking and a lot of low-level things.
ID: 892911973
20-10-2012 09:53:32
795 Tweet
137 Followers
58 Following







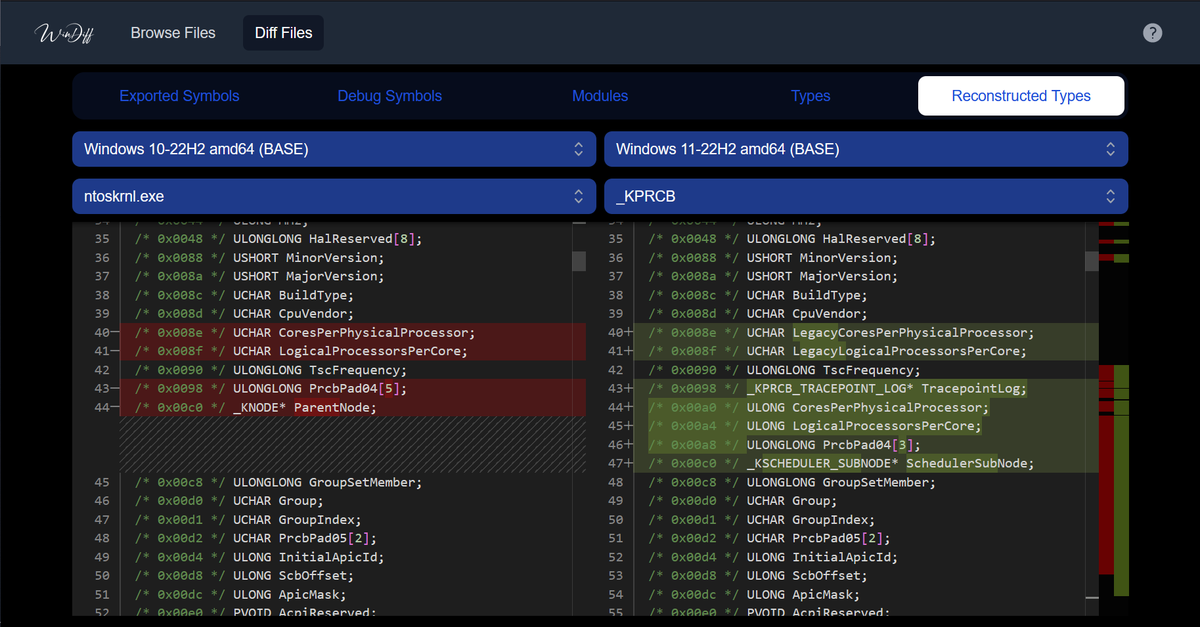
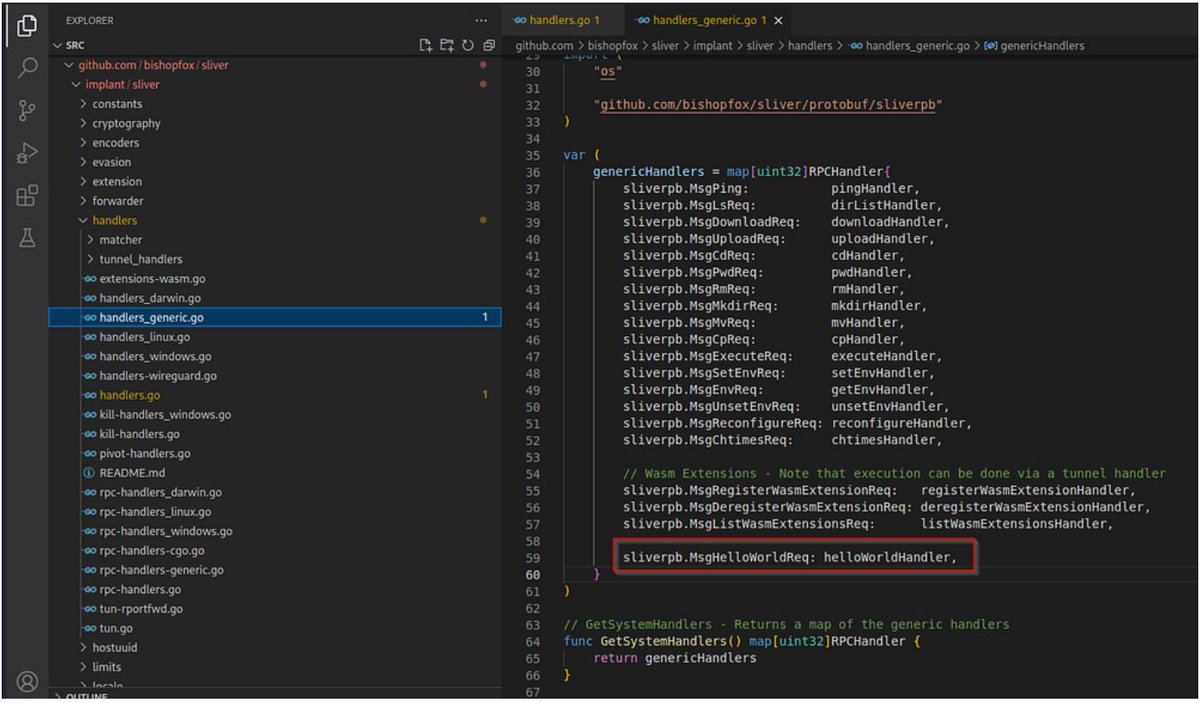
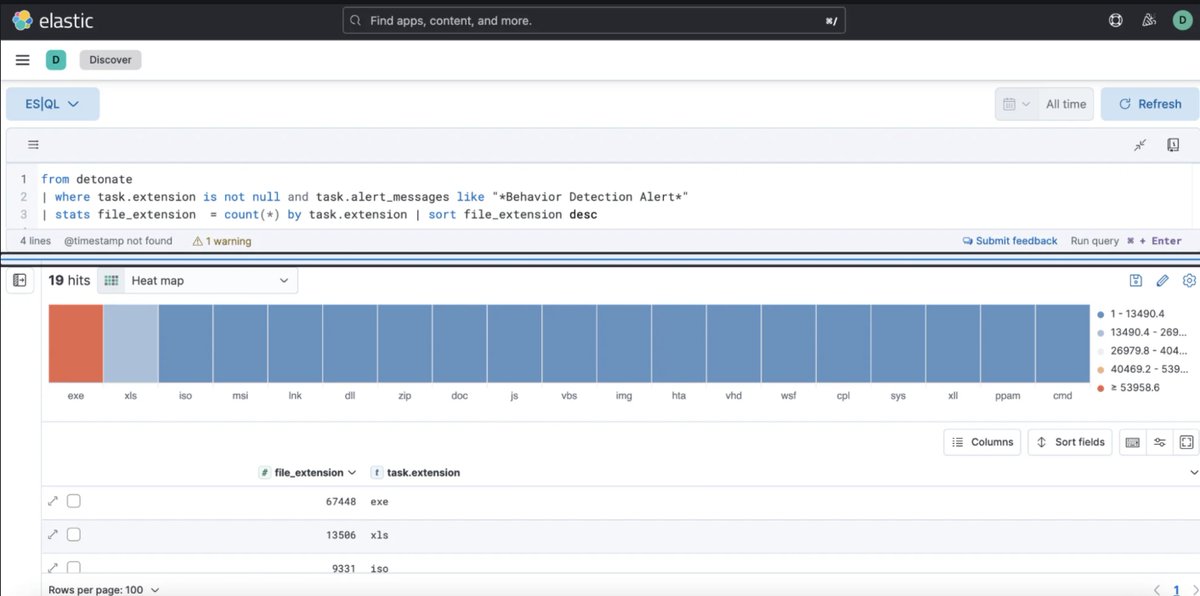
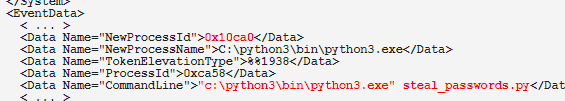
My new blog post for Hunt & Hackett is out! 🥳 It describes how it's possible to create a novel forensic tool that can reconstruct (malicious) executables on Windows without relying on collecting files or parsing attacker-controlled process memory. huntandhackett.com/blog/reconstru…








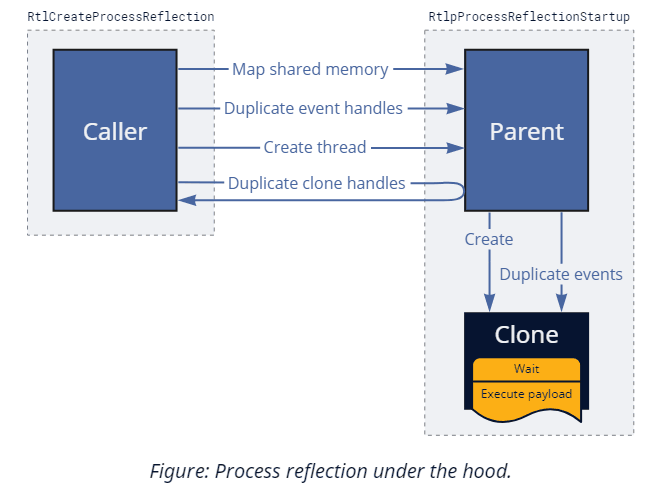
Thread Execution Hijacking is one of the well-known methods that can be used to run implanted code. In this blog we introduce a new injection method, that is based on this classic technique, but much stealthier - Waiting Thread Hijacking. Read More : research.checkpoint.com/2025/waiting-t…