Thomas Houhou
@th0h0
Security researcher | reported vulnerabilities to @X, @OpenAI, @AnthropicAI, @Swisscom and more | occasional speaker | cybersecurity student @ETH
ID: 1497006549583245316
https://www.thomashouhou.com/ 25-02-2022 00:33:44
25 Tweet
290 Followers
732 Following


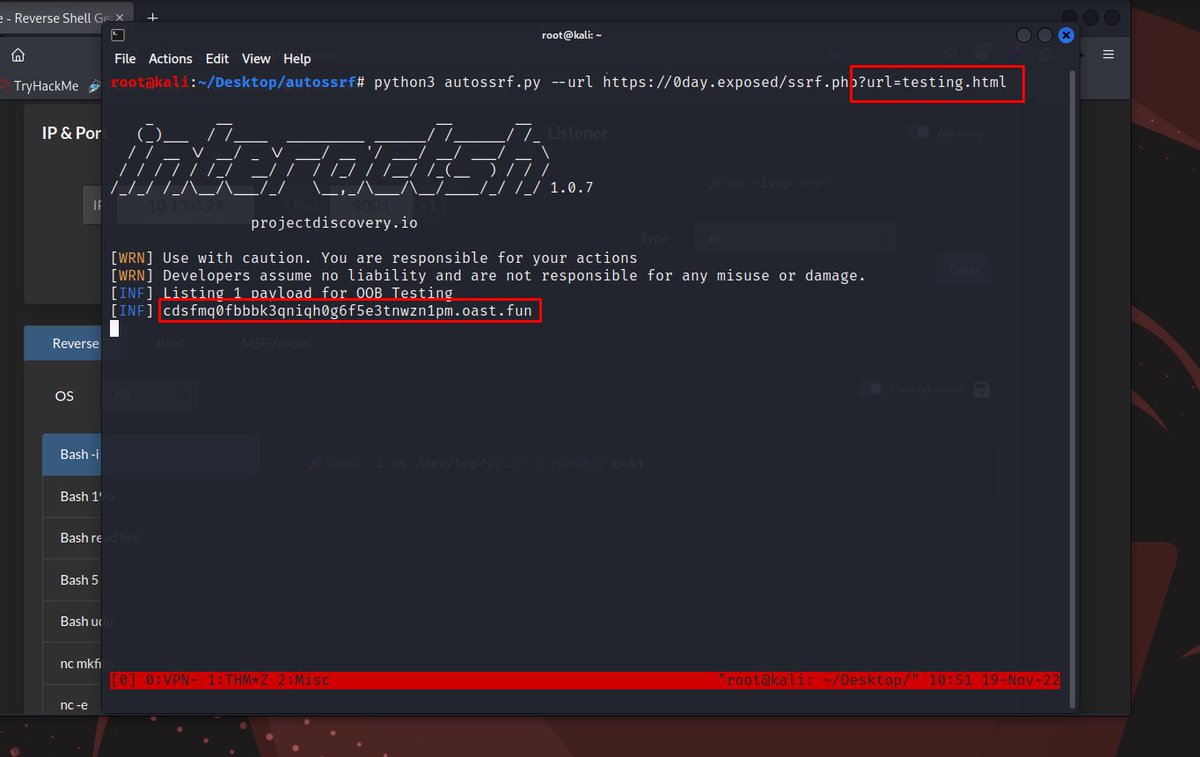
autoSSRF (Automatic SSRF Testing) - Smart fuzzing on relevant SSRF GET parameters and Context-based dynamic payload generation - Repo: github.com/Th0h0/autossrf - Creator: Thomas Houhou - - #CyberSecurity #bugbountytips #infosec #CTF #tools


Hey swisscyberstorm, would you mind approving my student ticket request? It's been a week since I sent you the e-mail 🥲





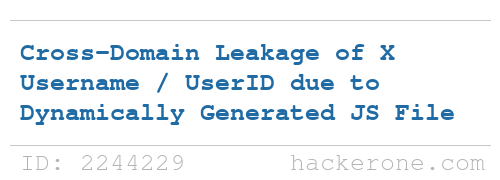
X (Formerly Twitter) disclosed a bug submitted by Thomas Houhou: hackerone.com/reports/2244229 - Bounty: $1,500 #hackerone #bugbounty