
Tamara Rezk
@tamararezk
Researcher in Computer Security @Inria
ID: 1252976754400153602
http://www-sop.inria.fr/members/Tamara.Rezk 22-04-2020 15:05:19
197 Tweet
286 Followers
96 Following


Become a PhD student with us at Chalmers Chalmers University of Technology Chalmers ICT and join the Chalmers Security & Privacy Lab cse.chalmers.se/research/group… Apply here: chalmers.se/en/about-chalm…





Interested in Kernel Safety, KASLR, or formal methods in the Spectre Era? Don't miss the talk by my student, Davide Davoli, at ACM CCS 2025 on October 15th, 16:15 in the Grand Ballroom, Salons A, B, C.



The first ever end-to-end cross-process Spectre exploit? I worked on this during an internship with grsecurity! An in-depth write-up here: grsecurity.net/cross_process_…

Excited to be part of the team receiving the ACM SIGSAC Distinguished Paper Award 🏆. Congrats Marco Guarnieri, @SCauligi, @YuvalYarom, Peter Schwabe, and w/o X handles: David Wu, David Romero, Chitchanok Cheungsatiansup, and Gilles Barthe!

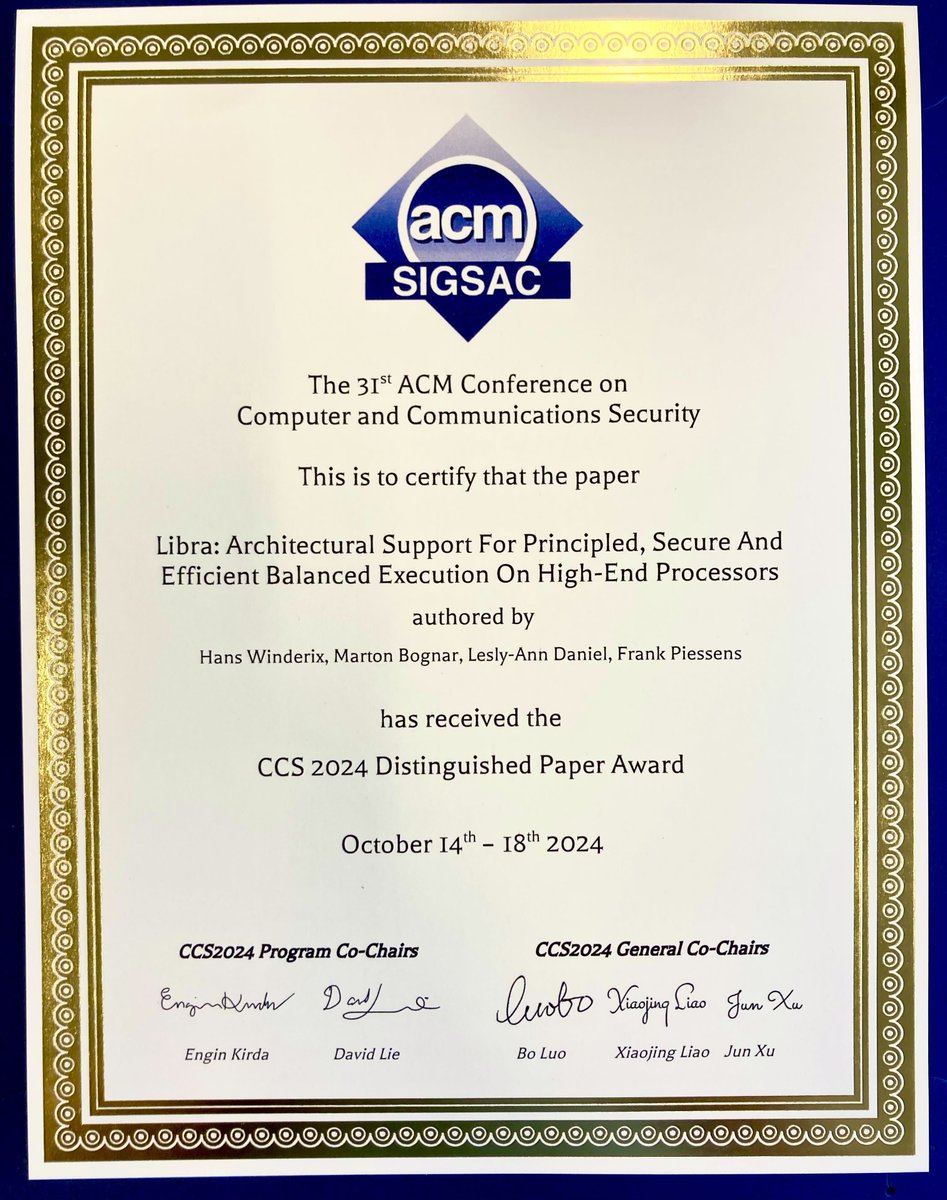
Our paper with Hans Winderix, Lesly-Ann Daniel, and Frank Piessens received the distinguished paper award at ACM CCS 2025! If you are interested in mitigating control-flow leakage, read the paper mici.hu/papers/winderi… and check out the repository github.com/proteus-core/l…


Big congrats to Mikhail Shcherbakov Mikhail Shcherbakov on his PhD thesis defense. Mikhail did great work on code reuse attacks in the web. Thanks to the opponent Yinzhi Cao, and grading committee members Anders Møller, Ben Stock, Emma Söderberg, and David Broman🍾🎉


The entire 3rd-edition of Ross Anderson's "Security Engineering" is available free as PDFs now! cl.cam.ac.uk/archive/rja14/…



Today, we announced the official release of OSV-SCALIBR, Google's software composition analysis library. If you are working in vuln management / security scanning, SCALIBR is for you! SCALIBR is powering most of Google's vuln scanning. Please RT security.googleblog.com/2025/01/osv-sc…

The purpose of the secret-erasure checker is to ensure that it did not happen and that no secret data remains in memory after the function returns. Check our TOPS paper for more details binsec.github.io/assets/publica… with Tamara Rezk and Lesly-Ann Daniel







