Phising Guide
#cybersecurity #pentesting #informationsecurity #hacking #DataSecurity #CyberSec #bugbountytips #Linux #websecurity #Network #Network Security #cybersecurity awareness


Incident Response Process
#cybersecurity #pentesting #informationsecurity #hacking #DataSecurity #CyberSec #bugbountytips #Linux #websecurity #Network #Network Security #cybersecurity awareness


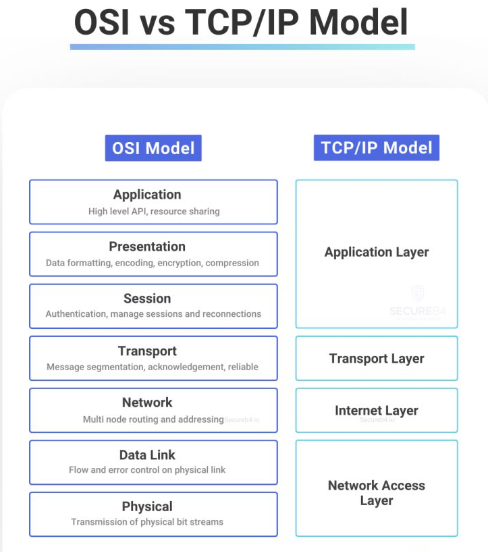
OSI vs TCP/IP Model
#cybersecurity #pentesting #informationsecurity #hacking #DataSecurity #CyberSec #bugbountytips #Linux #websecurity #Network #Network Security #cybersecurity awareness


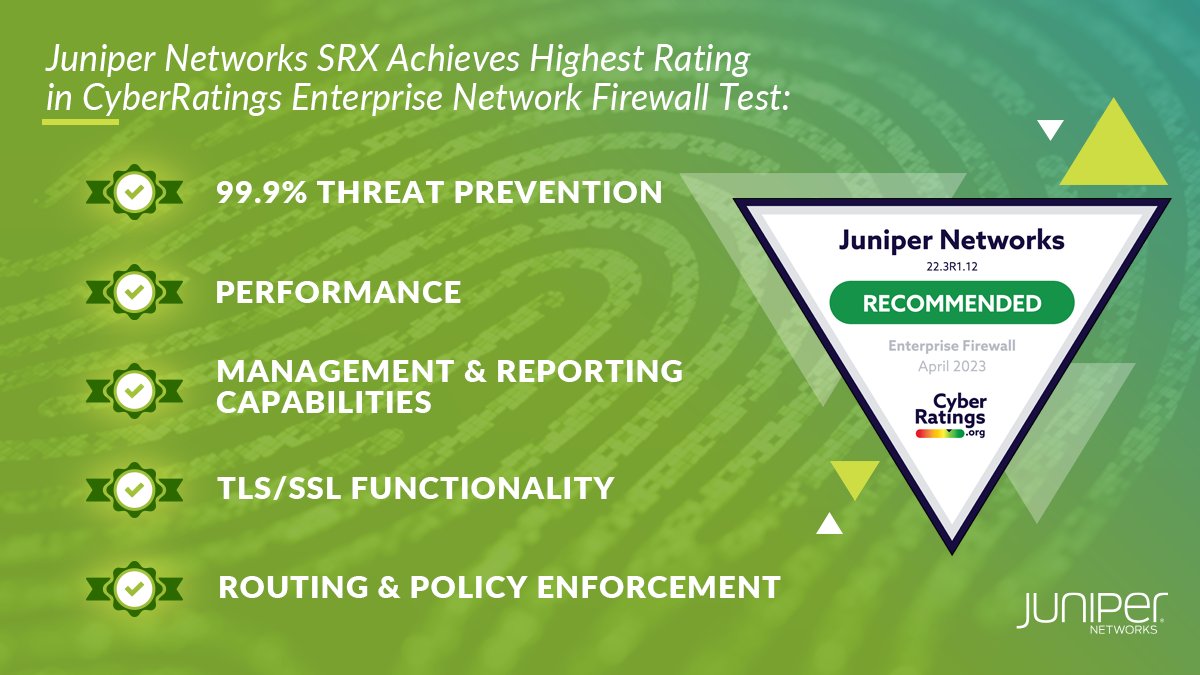
🔐 Settle for nothing less than superior #cybersecurity for your network. Our line of products will shield your organization from cyber threats with confidence.
See why we received the highest rating from CyberRatings.org. juni.pr/3NlhR2c

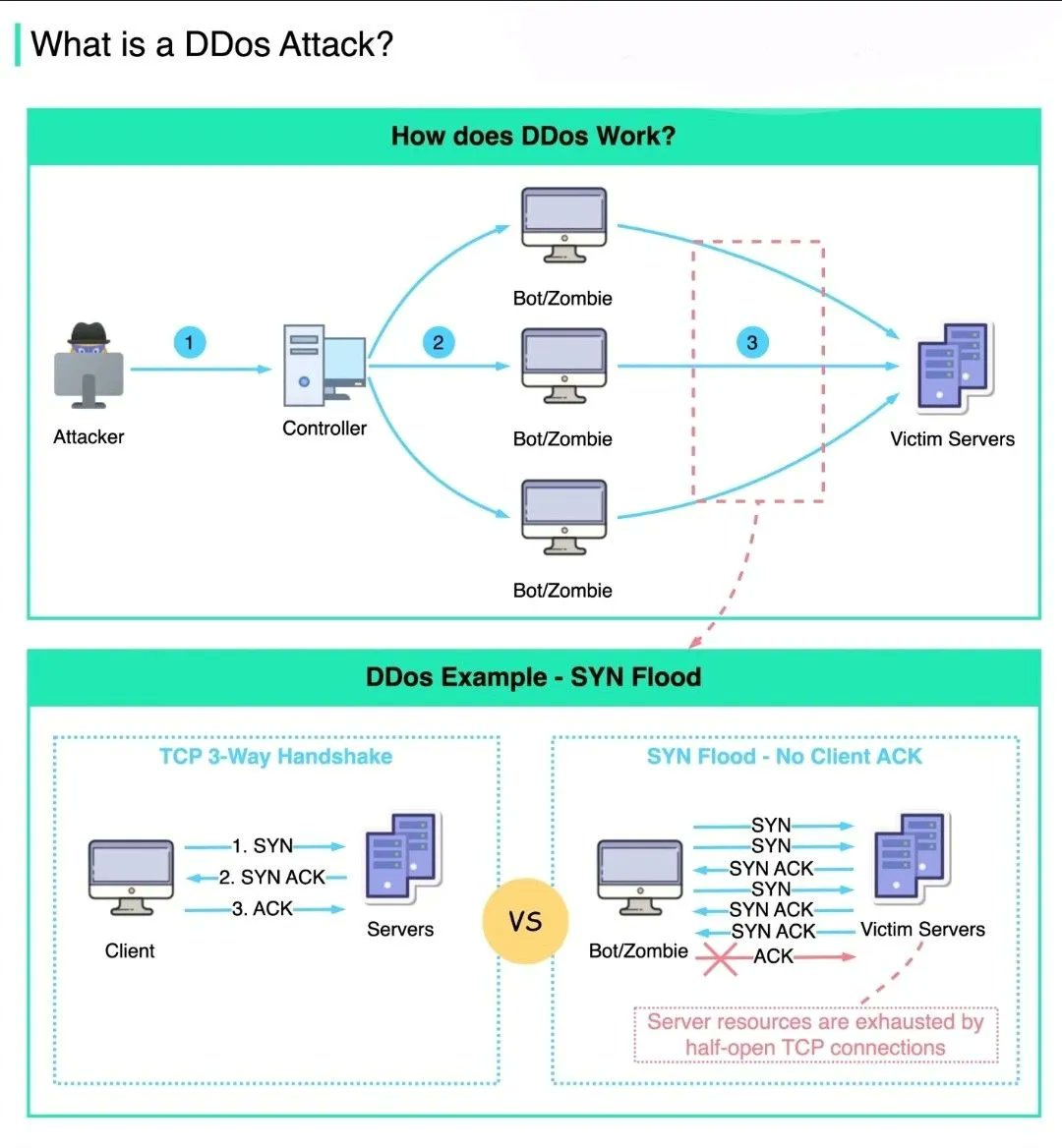
Basics of DDos Attack
#cybersecurity #pentesting #informationsecurity #hacking #DataSecurity #CyberSec #bugbountytips #Linux #websecurity #Network #Network Security #cybersecurity awareness


Incident Response Process
#cybersecurity #pentesting #informationsecurity #hacking #DataSecurity #CyberSec #bugbountytips #Linux #websecurity #Network #Network Security #cybersecurity awareness


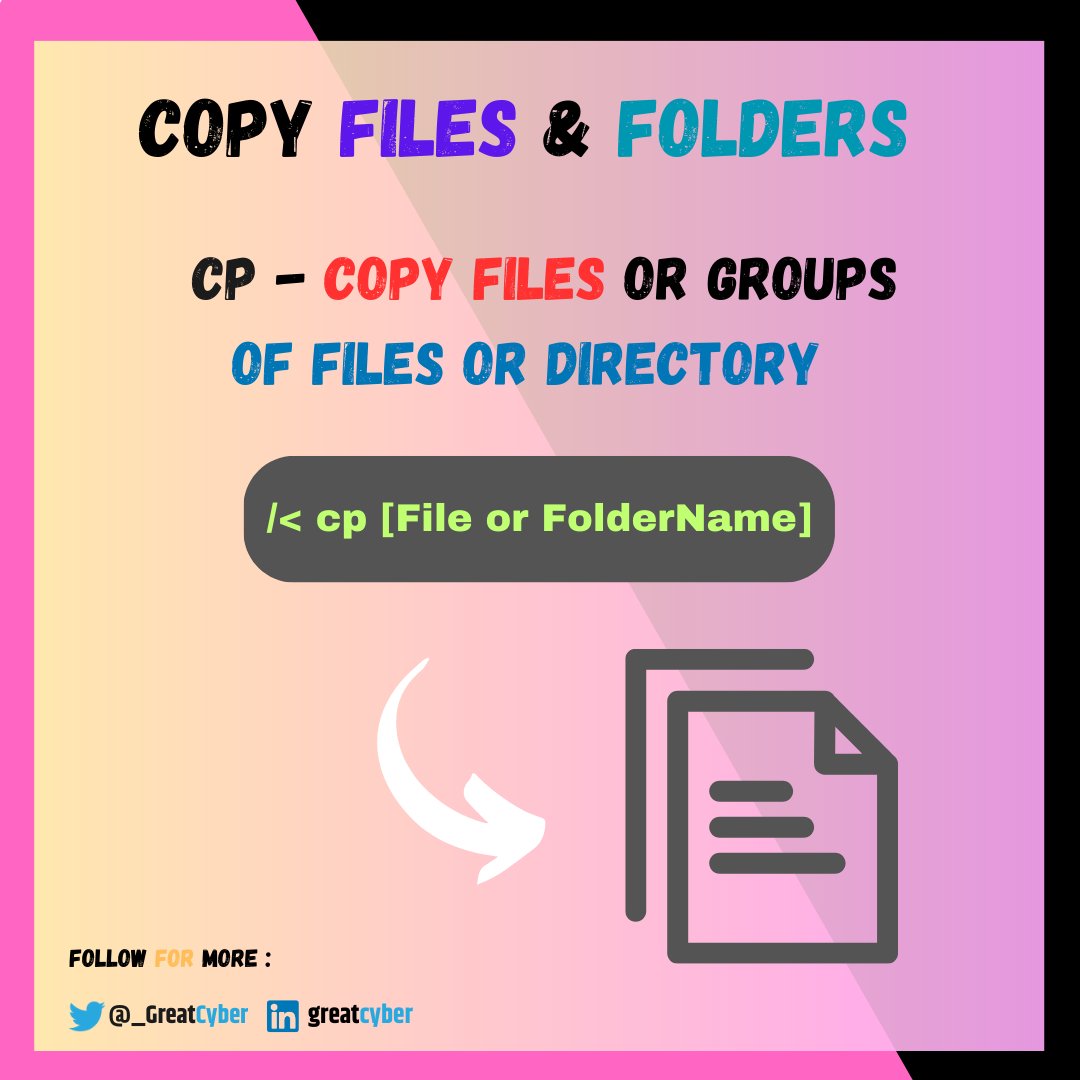
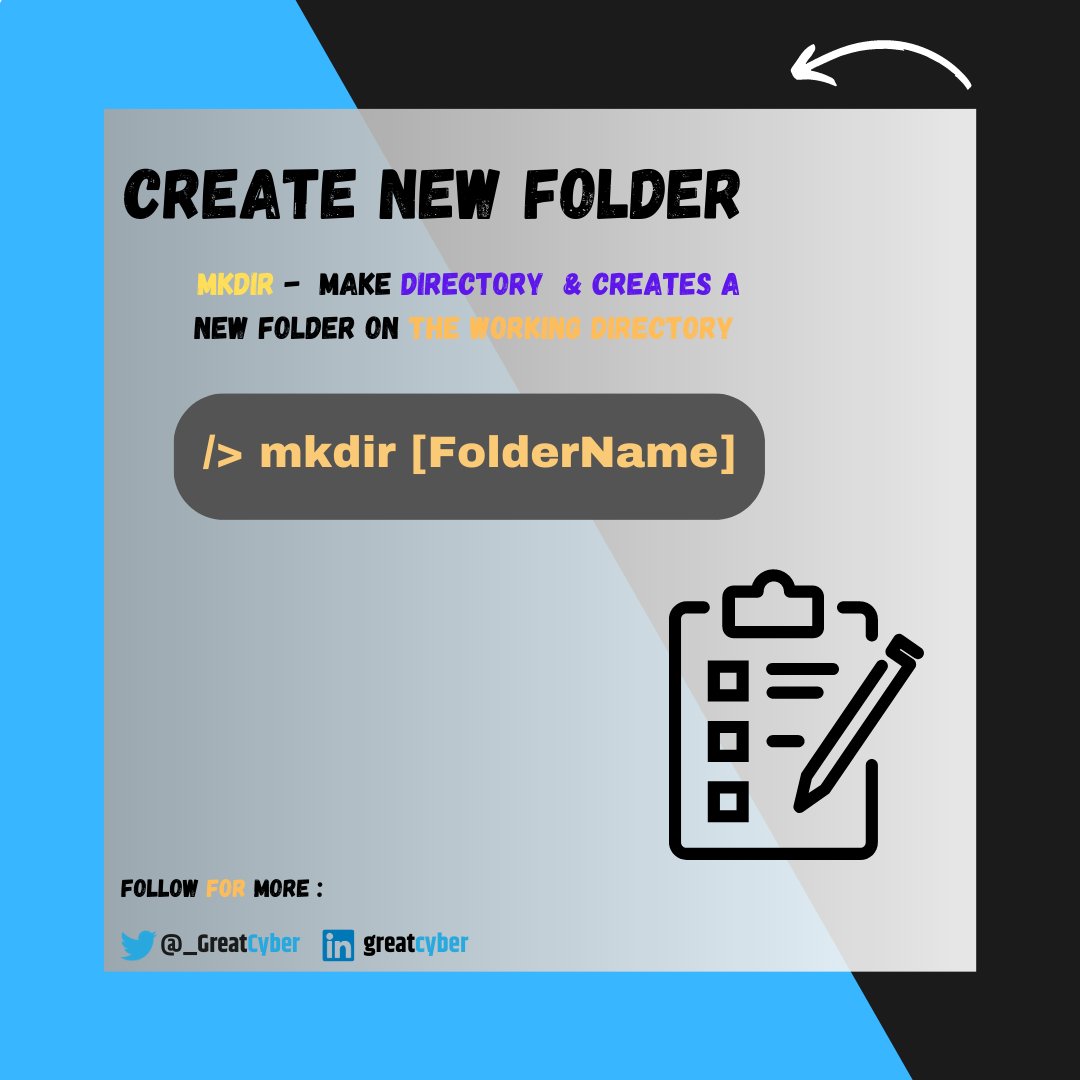
Must Know Basic Cmd Commands !💻
Windows '🔥
#cybersecurity #pentesting #informationsecurity #hacking #DataSecurity #CyberSec #bugbountytips #Linux #websecurity #Network #Network Security #cybersecurity awareness

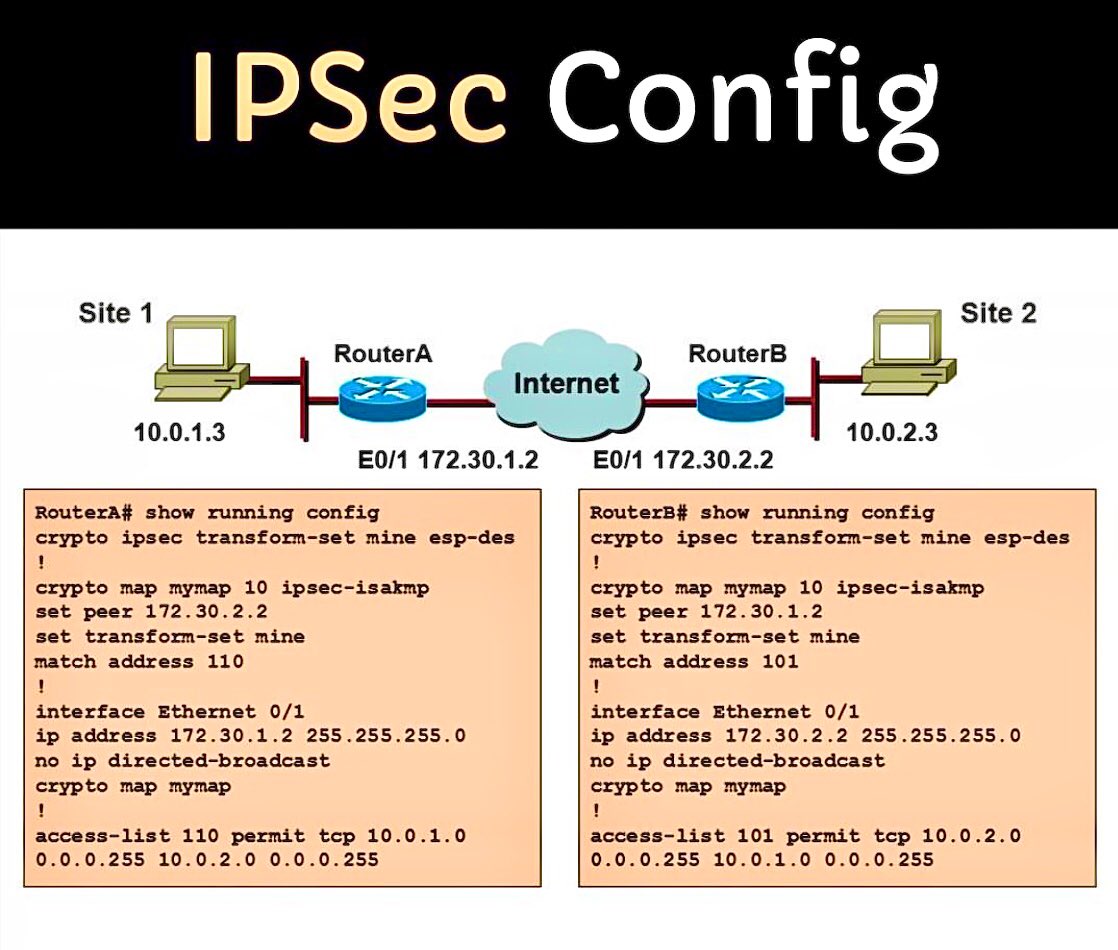
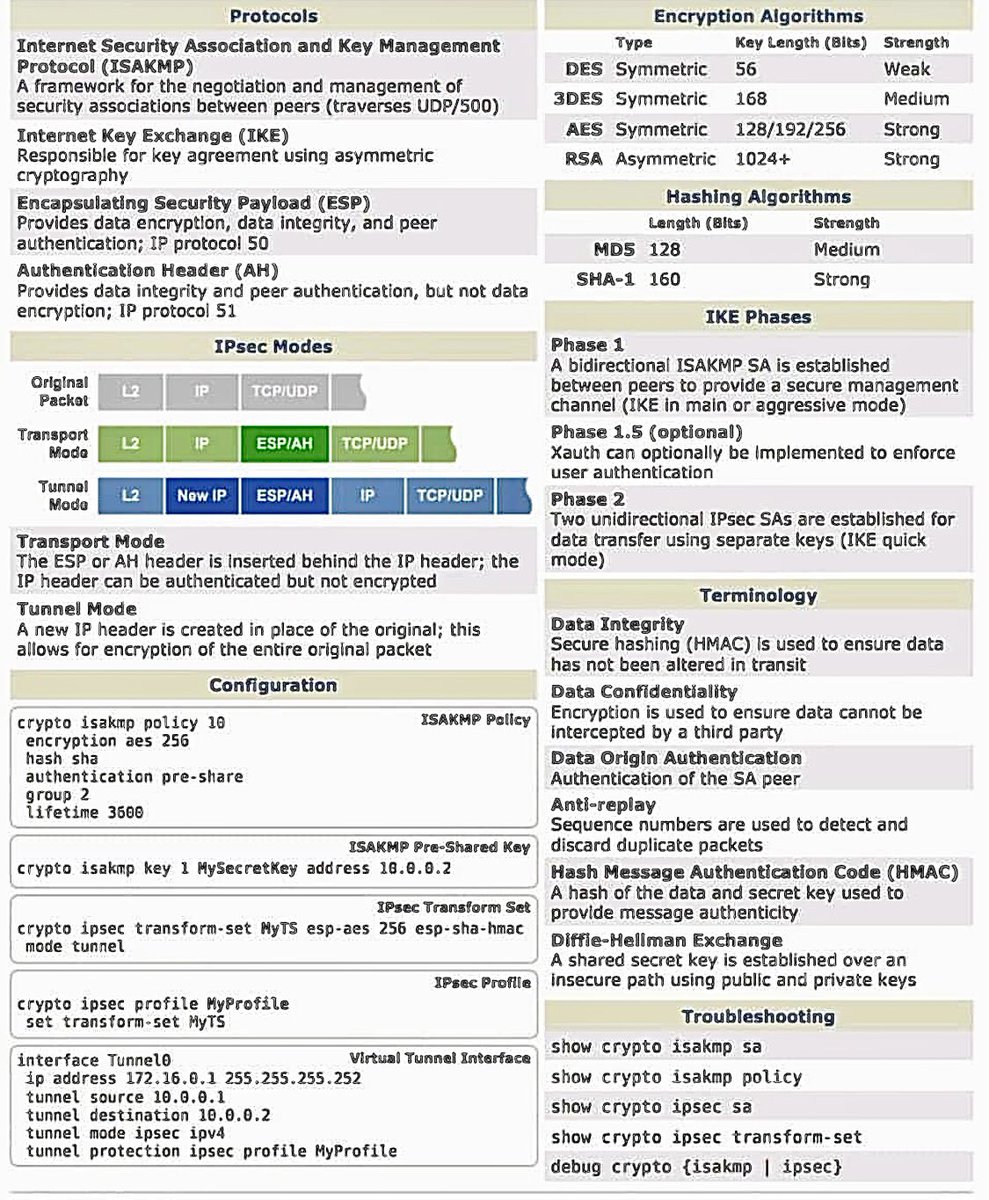
IPsec Config
#cybersecurity #pentesting #informationsecurity #hacking #DataSecurity #CyberSec #bugbountytips #Linux #websecurity #Network #Network Security #cybersecurity awareness

Types of Computer Network
#cybersecurity #pentesting #informationsecurity #hacking #DataSecurity #CyberSec #bugbountytips #Linux #websecurity #Network #Network Security #cybersecurity awareness



IPSec Summarized
#cybersecurity #pentesting #informationsecurity #hacking #DataSecurity #CyberSec #bugbountytips #Linux #websecurity #Network #Network Security #cybersecurity awareness

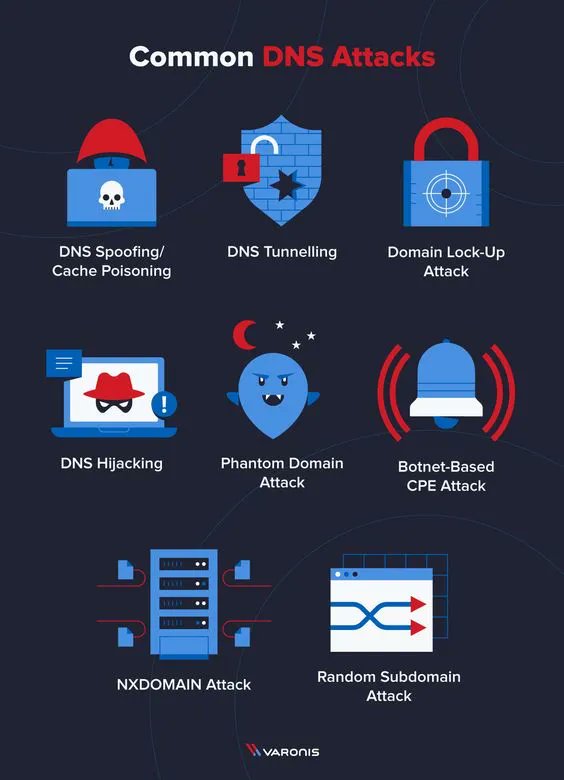
Common DNS Attacks
#cybersecurity #pentesting #informationsecurity #hacking #DataSecurity #CyberSec #bugbountytips #Linux #websecurity #Network #Network Security #cybersecurity awareness

Linux Permissions Explained
#cybersecurity #pentesting #informationsecurity #hacking #DataSecurity #CyberSec #bugbountytips #Linux #websecurity #Network #Network Security #cybersecurity awareness


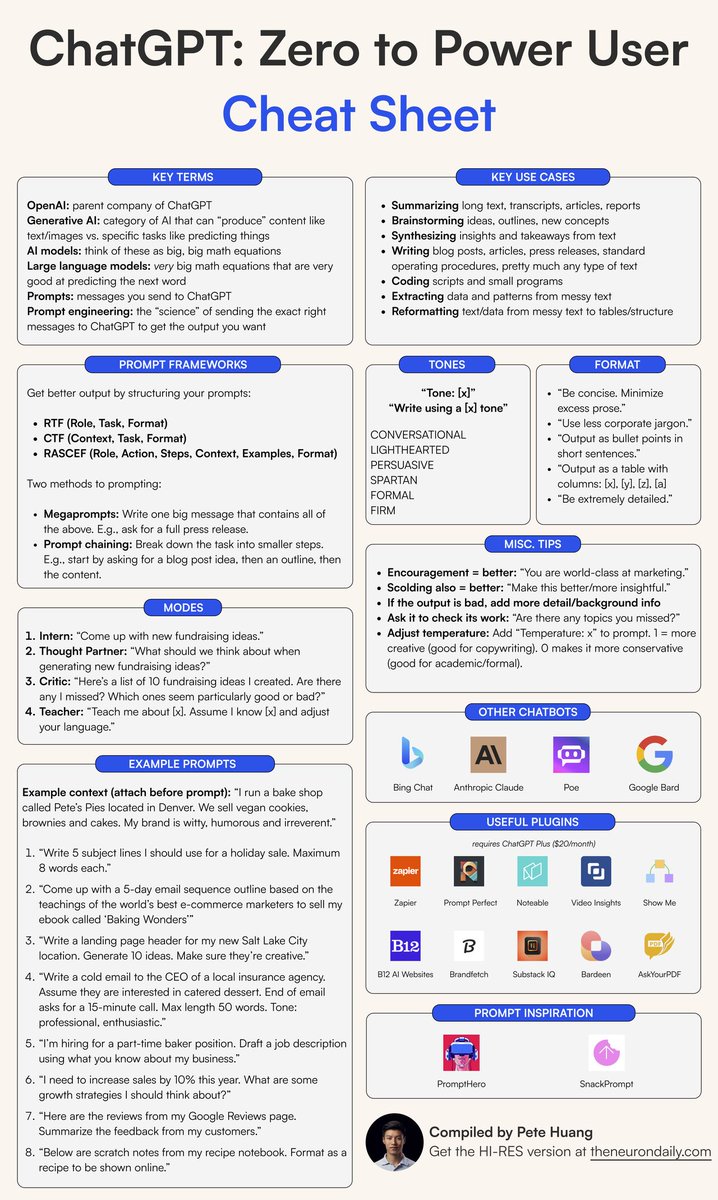
Chat GPT Cheat Sheet
#cybersecurity #pentesting #informationsecurity #hacking #DataSecurity #CyberSec #bugbountytips #Linux #websecurity #Network #Network Security #cybersecurity awareness

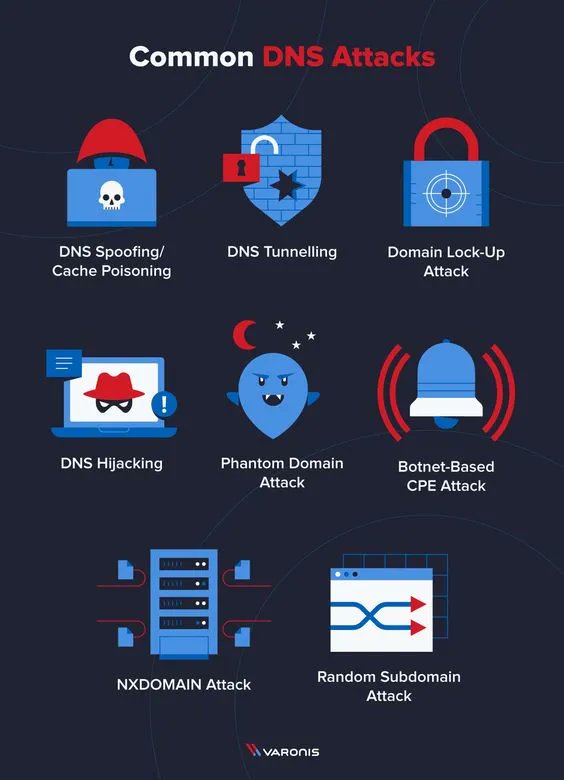
Common DNS Attacks
#cybersecurity #pentesting #informationsecurity #hacking #DataSecurity #CyberSec #bugbountytips #Linux #websecurity #Network #Network Security #cybersecurity awareness

Top 10 OSINT Tools
Credit: Hacker Combat™
#cybersecurity #pentesting #informationsecurity #hacking #DataSecurity #CyberSec #bugbountytips #Linux #websecurity #Network #Network Security #cybersecurity awareness


Information Security vs Cyber Security
#cybersecurity #pentesting #informationsecurity #hacking #DataSecurity #CyberSec #bugbountytips #Linux #websecurity #Network #Network Security #cybersecurity awareness


Must Know Basic Cmd Commands !💻
Windows ' 🔥
#linux #cybersecurity #pentesting #informationsecurity #hacking #DataSecurity #CyberSec #bugbountytips #Linux #websecurity #Network #Network Security #cybersecurity awareness

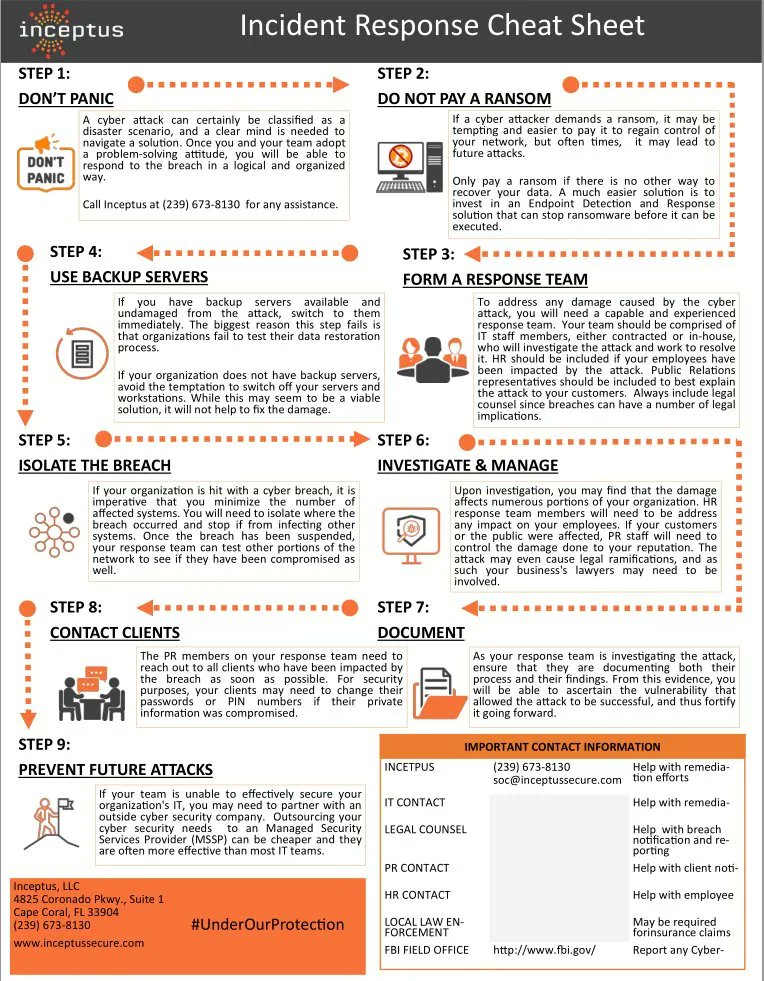
Incident Response Cheat Sheet
#cybersecurity #pentesting #informationsecurity #hacking #DataSecurity #CyberSec #bugbountytips #Linux #websecurity #Network #Network Security #cybersecurity awareness