t4r4ntu1a
@t4r4ntu1a
Embedded security guy 💃
ID: 1492798741413339141
13-02-2022 09:52:42
888 Tweet
45 Followers
542 Following

SCADA Hacking: The Most Important SCADA/ICS Attacks in History Although it won't predict the future, it can provide insights to how SCADA hacks can be implemented and their potential impacts on a nation's or region's infrastructure. hackers-arise.com/post/scada-hac… OccupytheWeb



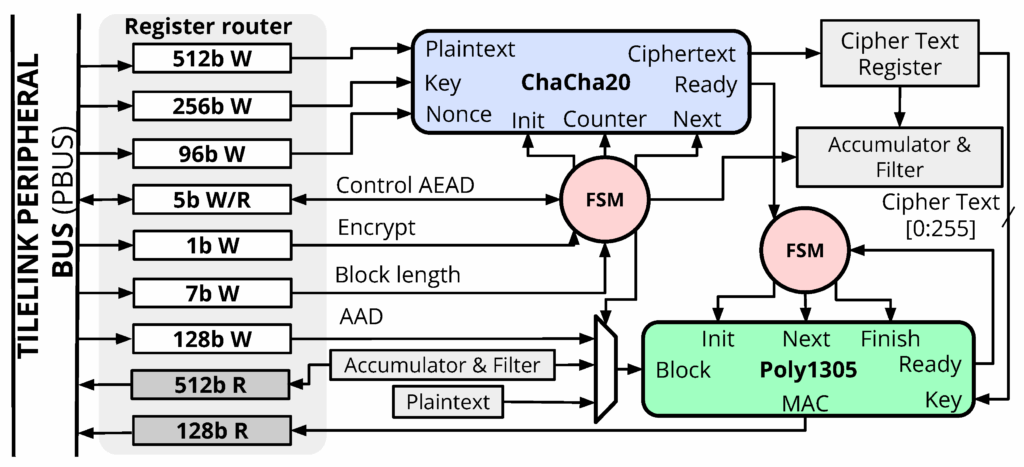
ChaCha20 is a cryptography algorithm built for speed, security, and simplicity. Learn more in our article about why it should be in your arsenal: hackers-arise.com/intermediate-c… OccupytheWeb Di Co11ateral