Victor Sergeev
@stvetro
I help enterprises to find and remediate complex cyberthreats
ID: 939045252035362816
08-12-2017 08:13:29
126 Tweet
91 Followers
98 Following





This week I learned that resource-based constrained delegation can be (ab)used as a means for LPE. Low priv shell -> create machine account -> Webdav -> coerced auth -> RBCD -> LPE Special thanks to Adam Crosser from Praetorian for his blog. Ref: praetorian.com/blog/red-team-…





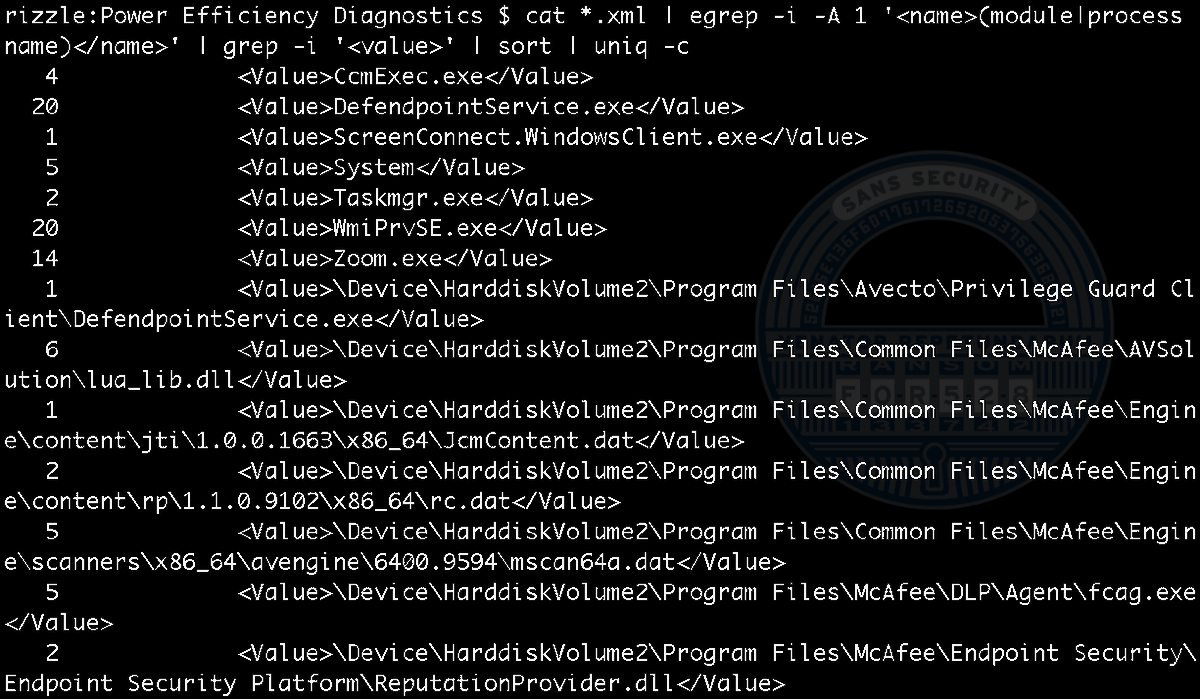
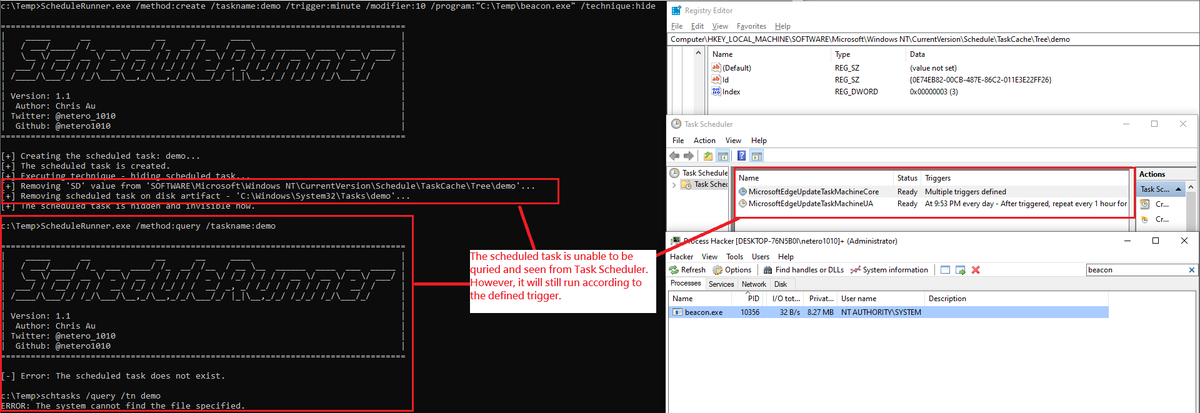
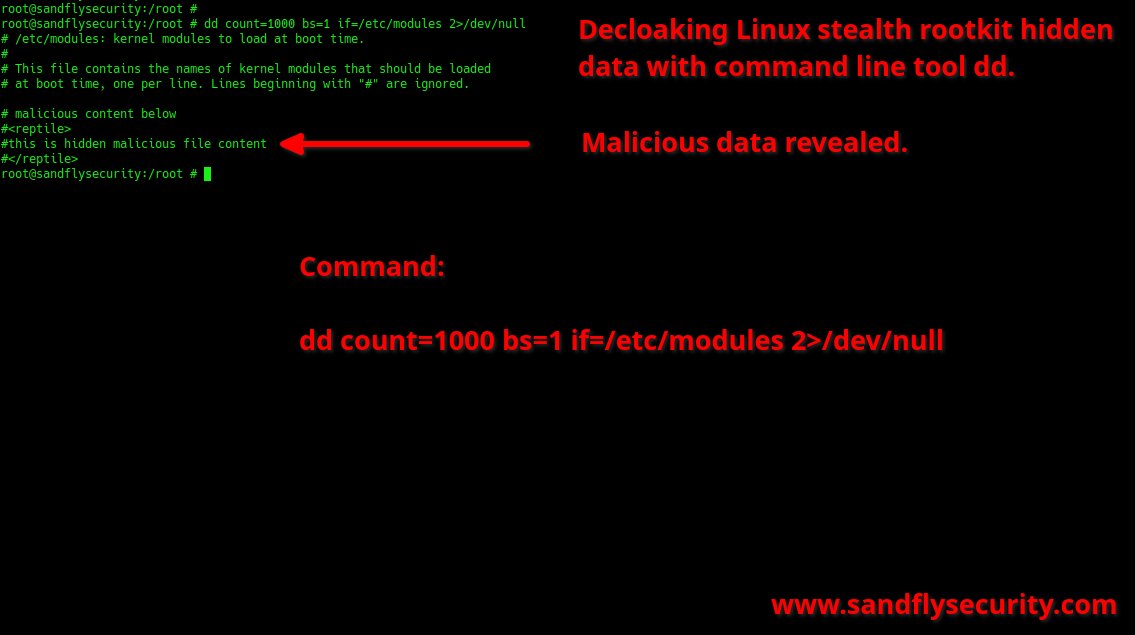
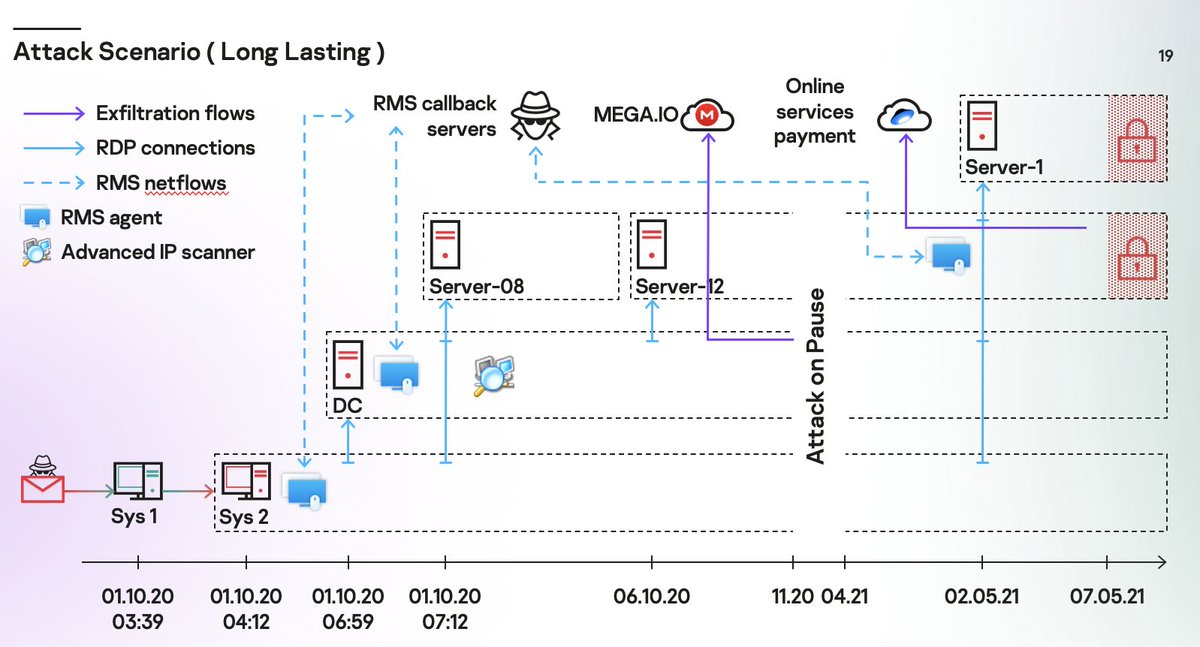
Significant raise in vulnerability exploitation as initial access vector. Analysis of incident response practice in Ayman Shaaban webinar brighttalk.com/webcast/15591/… and analyst report github.com/klsecservices/… #dfir #incidentresponse #threathunting





5 #pros and #cons of using #GenerativeAI during #IncidentResponse securitymagazine.com/articles/99984… #fintech #cybersecurity #AI #ArtificialIntelligence #MaachineLearnig Victor Sergeev Kaspersky SECURITY Magazine

A 'compromise assessment service' in #CyberSecurity is an evaluation that identifies potential unauthorized access or possible breaches in a computer network by analysing system data and logs. Want to learn more? SOC Experts Victor Sergeev & A.Khlief explain 👇 kaspersky.com/blog/understan…