Str4thus
@str4thus
if it works, it works
ID: 1324701532521172992
06-11-2020 13:15:45
128 Tweet
35 Followers
168 Following


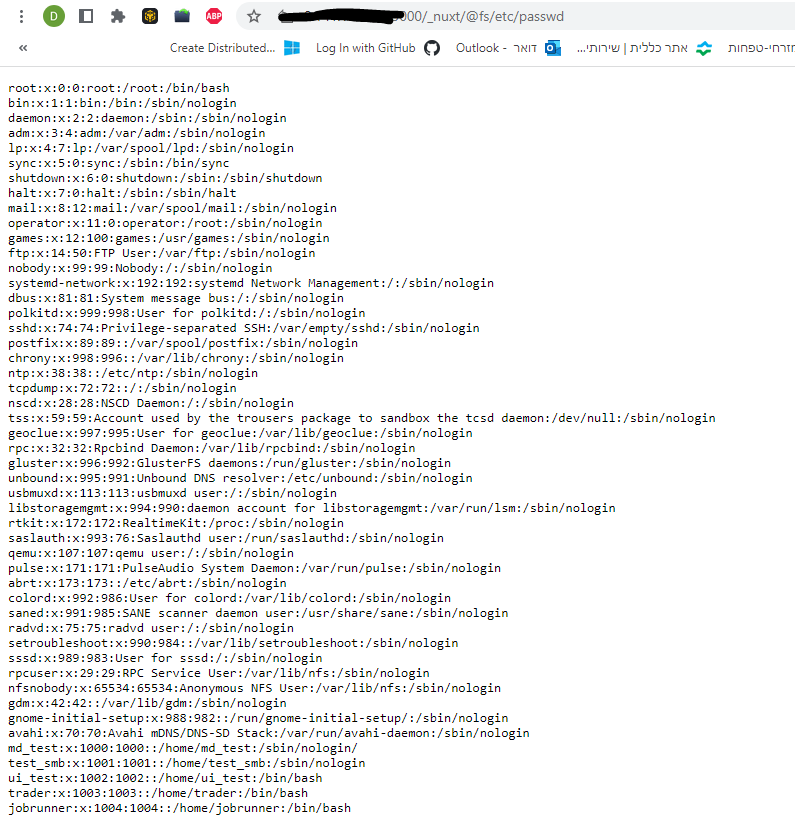
Path traversal in nuxt huntr.dev/bounties/4849a… when you "/_nuxt/Felipe Silva" in JS script or even in HTML that mean the Dev is enable :) have fun




In our latest post, Matt Johnson details how we were able to publish a malicious VSCode extension to the marketplace and leverage it for initial access during a red team mdsec.co.uk/2023/08/levera… vimeo.com/853281700?shar…


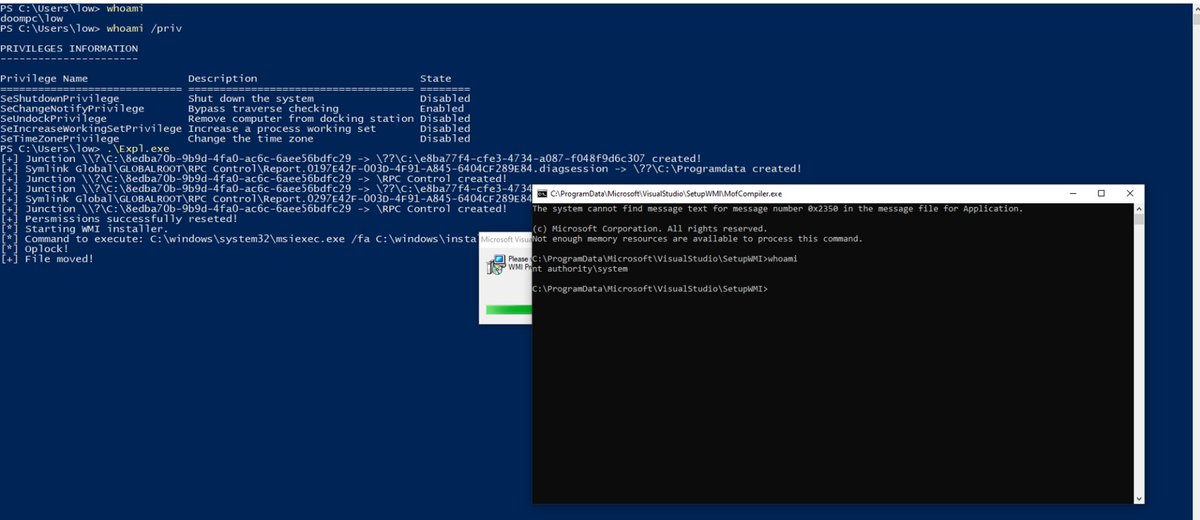
Exploiting CVE-2024-20656, a Local Privilege Escalation in the VSStandardCollectorService150 Service mdsec.co.uk/2024/01/cve-20… - new research from Filip Dragovic




Excited to announce our new blog post on new event handlers to trigger XSS! Huge thanks to Bojan Zdrnja for making this happen and to PortSwigger Research for their awesome XSS cheat sheet, now featuring these techniques. infigo.hr/en/insights/46…

Sharing a new mini research technique that abuses HTML injection to leak data cross-domain. This blogpost connects couple of client-side concepts and a Chrome/RFC Referrer-Policy bug. Inspired by Gareth Heyes \u2028 recent CSP bypass techniques, enjoy :) infigo.is/en/insights/47…

Great Shazzer vector from Mateo Hanžek shows what characters don't change the host after the domain shazzer.co.uk/vectors/6779e4…