Steve Linford
@stevelinford
Founder & Chairman of @Spamhaus ⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀ ⠀⠀⠀ ⠀ ▶︎ For Spamhaus Support see: spamhaus.org ⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀ ⠀⠀ ⠀⠀ Views are my own.
ID: 77398418
26-09-2009 04:41:59
170 Tweet
176 Followers
168 Following












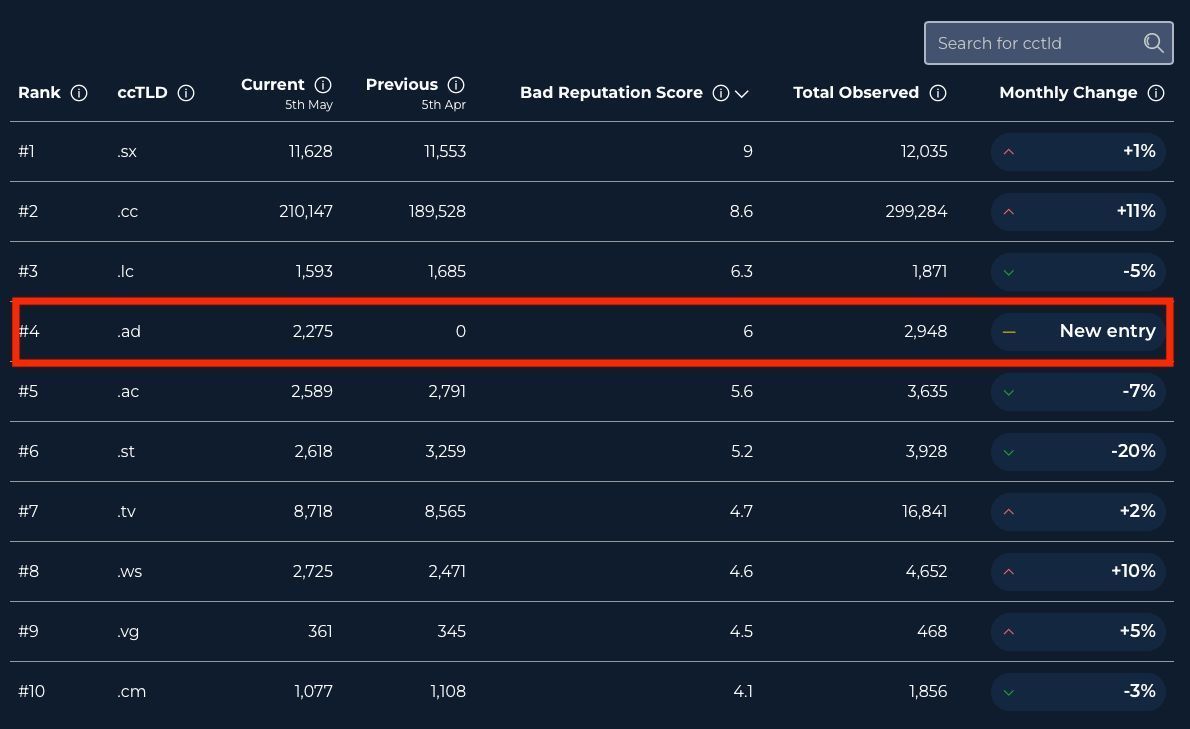
Hola cesar marquina, no sé a qui he de portar això a l'atenció de seguretat d'@andorratelecom, però és un problema urgent per als dominis .AD







💡 An insightful read from Sven Krohlas, Detection Engineer at Spamhaus Technology on how modern blocklists have advanced, enabling threat classification with far greater precision, from: 👉 IPs to domains, URLs, email addresses, and crypto wallets 👉 binary blocking to targeted rate