Andre Pawlowski
@sqall01
IT-security enthusiast. Maker. Member of @FluxFingers. Author of alertr.de
ID: 108678255
https://pawlowski.dev 26-01-2010 18:24:37
1,1K Tweet
666 Followers
70 Following




If you run an open source project and need to protect your infrastructure, Sandfly Security will give you a free full license. Reach out at our website or here with a DM and we'll get you sorted. We do this for other projects and want to protect the integrity of your hard work.






Pitfalls of relying on eBPF for security monitoring (and some solutions) from Trail of Bits Very nice overview and production problem you could encountered creating a security solution based on ebpf. And even some bypass 😁 blog.trailofbits.com/2023/09/25/pit…

It is back. Contribute if you can to this nice project. And good to see that Gynvael Coldwind's health is up for doing side projects again :)

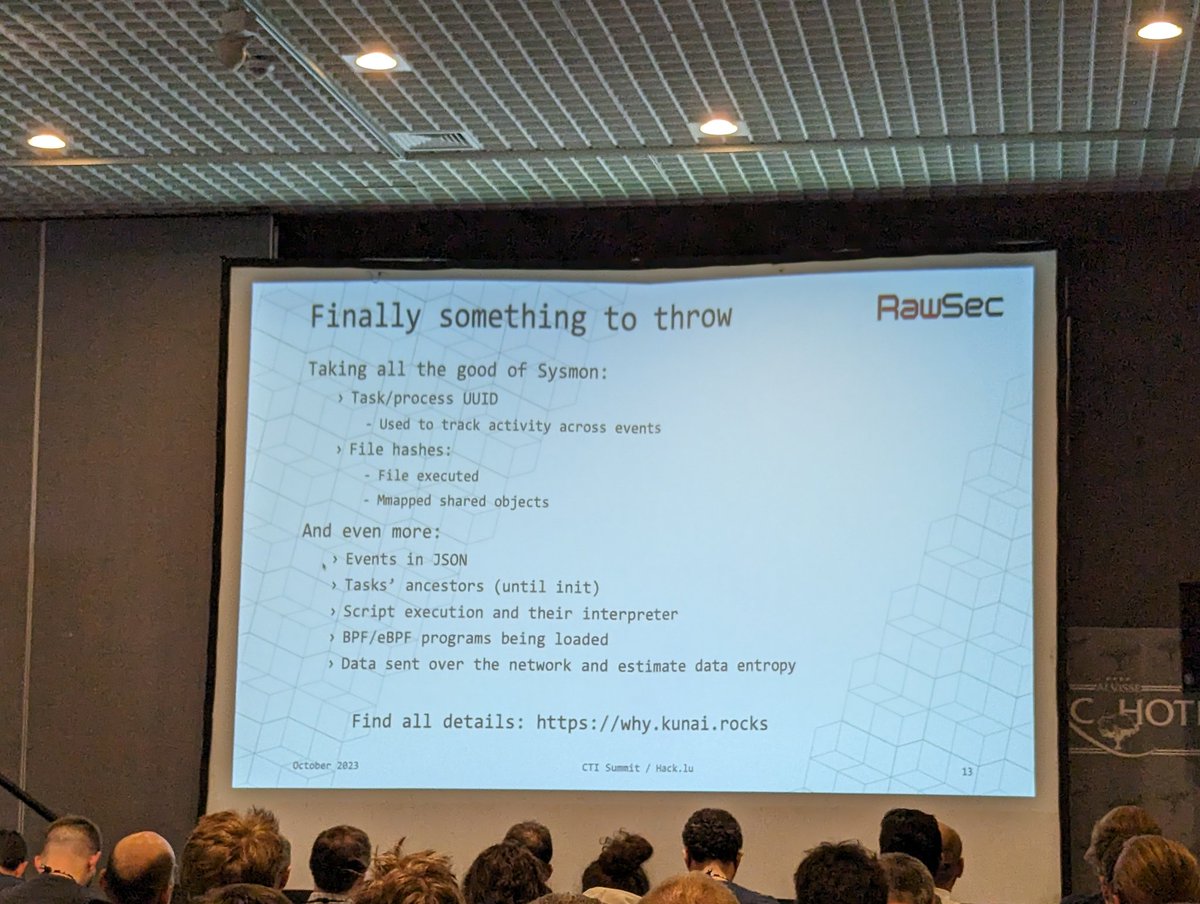
Kunai is an open source sysmon "clone" developed in rust and based on eBPF (cc Alexei Starovoitov) that has just been presented at #hacklu github.com/0xrawsec/kunai