Solvo
@solvocloud
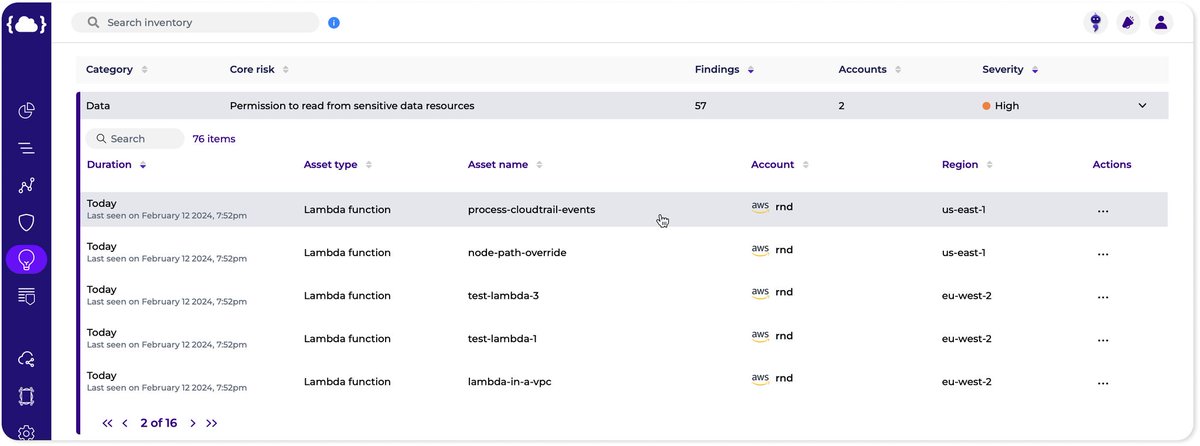
identifying, prioritizing, and automatically mitigating risks associated with cloud access permissions and entitlements
ID: 1297486022020931586
http://www.solvo.cloud 23-08-2020 10:49:19
386 Tweet
160 Followers
165 Following




Join the conversation about Solvo's rise - from our roots to becoming a contender in CIEM and CSPM spaces. Is Solvo the missing piece in your security puzzle? Explore the latest research from S&P Global Market Intelligence to find out: hubs.li/Q02gX81B0