Worawit Wang
@sleepya_
ID: 233819752
04-01-2011 05:23:18
702 Tweet
1,1K Followers
39 Following












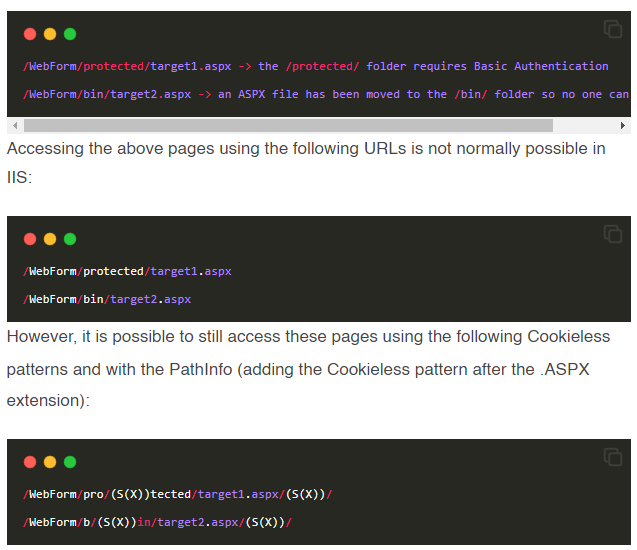
The new Cookieless variant (CVE-2023-36560) has been added to soroush.me/blog/2023/08/c… Markus Wulftange 😇

We're revealing details of an obscure debugging feature in the Apple A12-A16 SoC’s that bypasses all of the hard-to-hack hardware-based memory protections on new iPhones. Its not used by the firmware and we don't know how the attackers found out about it. securelist.com/operation-tria…

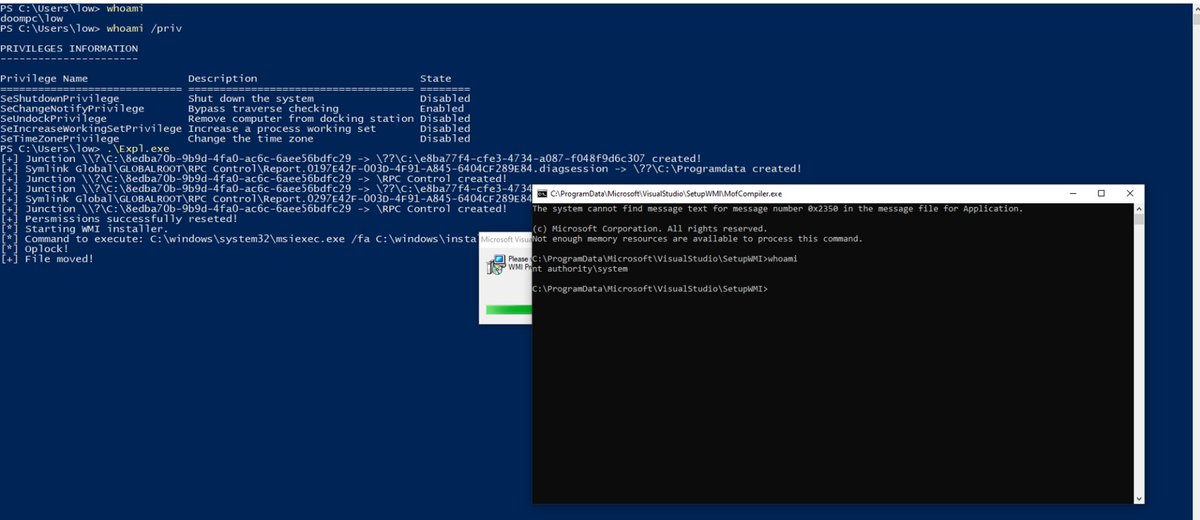
Exploiting CVE-2024-20656, a Local Privilege Escalation in the VSStandardCollectorService150 Service mdsec.co.uk/2024/01/cve-20… - new research from Filip Dragovic

The award-winning Qualys Threat Research Unit (TRU) has discovered a critical vulnerability in OpenSSH, designated CVE-2024-6387 and aptly named "regreSSHion." This Remote Code Execution bug grants full root access, posing a significant exploitation risk. blog.qualys.com/vulnerabilitie…

The detailed version of our #WorstFit attack is available now! 🔥 Check it out! 👉 blog.orange.tw/posts/2025-01-… cc: splitline 👁️🐈⬛