KingKor
@siniskor
pizza,style,music
ID: 845356567
25-09-2012 11:32:35
16 Tweet
10 Followers
321 Following





New version of #AADInternals out now, including remote dumping of #ADFS configuration database🔥 Read the blog at: o365blog.com/post/adfs/ Credits to Vesa Tikkanen, Doug Bienstock, Austin Baker, Dirk-jan, 🥝🏳️🌈 Benjamin Delpy, 📔 Michael Grafnetter, and Roberto Rodriguez 🇵🇪 for your help and previous work!




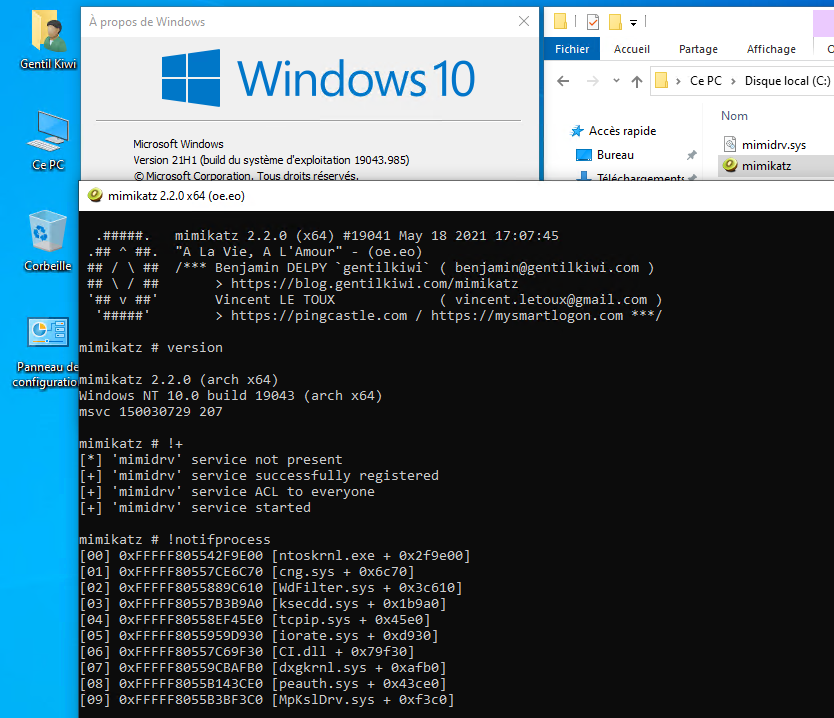
Want to try to decode SCCM passwords in SC_UserAccount table with #mimikatz ? 🥝 (hints, lots of them have usually admin rights 🤪) A little POC here: github.com/gentilkiwi/mim… So Jonas Vestberg can try it ;)