Silv0123
@silv0123
Malware Analyst
#ThreatIntel #BlueTeam #DFIR #CTI
ID: 815265366326804481
31-12-2016 18:36:25
116 Tweet
1,1K Takipçi
840 Takip Edilen


New Kind of Network (NKN) C2 schema for malware comms. This could get interesting. Check it out: NKN: nkn.org/technology/our… RAT: github.com/Maka8ka/NGLite Files: virustotal.com/gui/domain/see… SDK: github.com/nknorg/nkn-sdk… Blog: maka8ka.cc/post/%E4%B8%80… h/t @NinjaOperator & Robert Falc





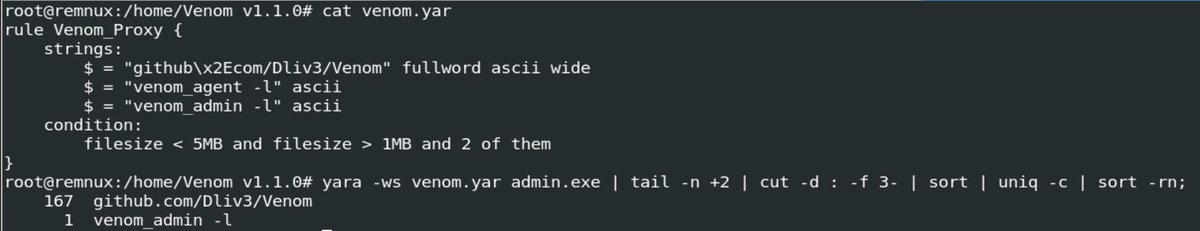
Thanks Florian Roth ⚡️ I would suggest editing APT_HKTL_Wiper_WhisperGate_Stage3_Jan22 keepc $xc1 but remove $s1 and change filesize limit to at least 5MB to detect b6563e61cdc02b6379efc51eb8792a43

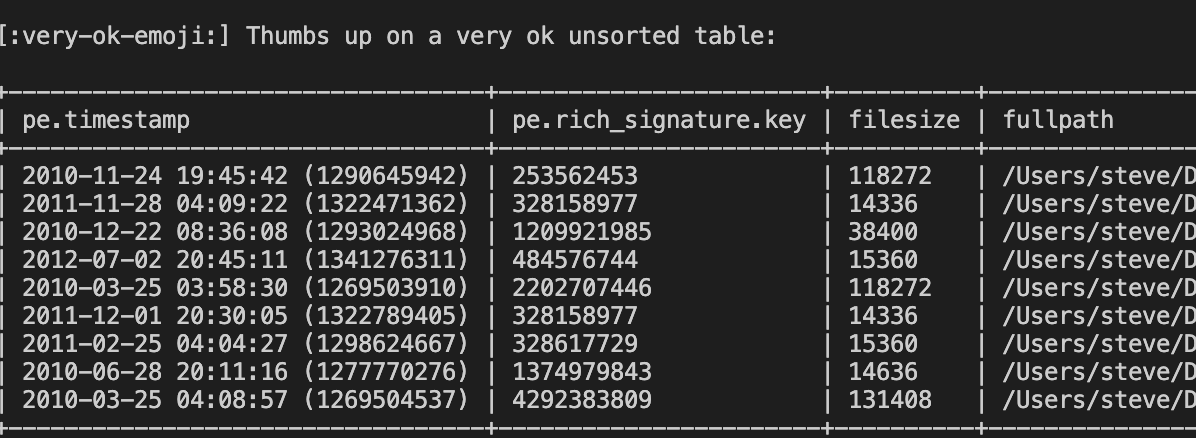
#100DaysofYARA #dailyyara Ransom path $ = /[A-Za-z]:[\x2F\x5C][\x00-\x7F]{0,300}[Rr][Aa][Nn][Ss][Oo][Mm][\x00-\x7F]{0,300}\.(pdb|go)/ ascii 6bc2a7555122ccaddd5ae0497f3a3419 Steve YARA Synapse Miller it would be awesome if you'll create new Go paths ruleset just like the pdb ones!










#100DaysOfYARA #dailyyara Always wanted to keep writing regex for perfect detections but would sacrifice performance 3 recommended things to enhance performance - file header - file size - regex position github.com/silv0123/yara-… I Hope Florian Roth ⚡️ won't come after me for this.



![Silv0123 (@silv0123) on Twitter photo Hey <a href="/ET_Labs/">ET Labs</a>
I would suggest editing sid 2035653 pcre to
/^[A-Za-z0-9\/_-+]{171}=$/ Hey <a href="/ET_Labs/">ET Labs</a>
I would suggest editing sid 2035653 pcre to
/^[A-Za-z0-9\/_-+]{171}=$/](https://pbs.twimg.com/media/FPTBastXEAAKb56.jpg)

![Silv0123 (@silv0123) on Twitter photo #ThreatIntel
Fresh #Emotet DLL detected by <a href="/kaspersky/">Kaspersky</a>
bc729f7827290a0899c0b811f91a8f09
www[.]nexxdecor[.]vn #ThreatIntel
Fresh #Emotet DLL detected by <a href="/kaspersky/">Kaspersky</a>
bc729f7827290a0899c0b811f91a8f09
www[.]nexxdecor[.]vn](https://pbs.twimg.com/media/FUngdbRXsAAewnz.jpg)