
shri0x900x90
@shridong
ID: 2832550772
26-09-2014 05:00:26
915 Tweet
16 Takipçi
329 Takip Edilen


New update to nanodump! You can now force WerFault.exe to dump LSASS for you. Thanks to Asaf Gilboa for the original research. github.com/helpsystems/na…






Get an in-depth analysis of recent #Windows #vulnerability, CVE-2022-30136> from cybersecurity expert and #exploit writer Ricardo Narvaja coresecurity.com/core-labs/arti…










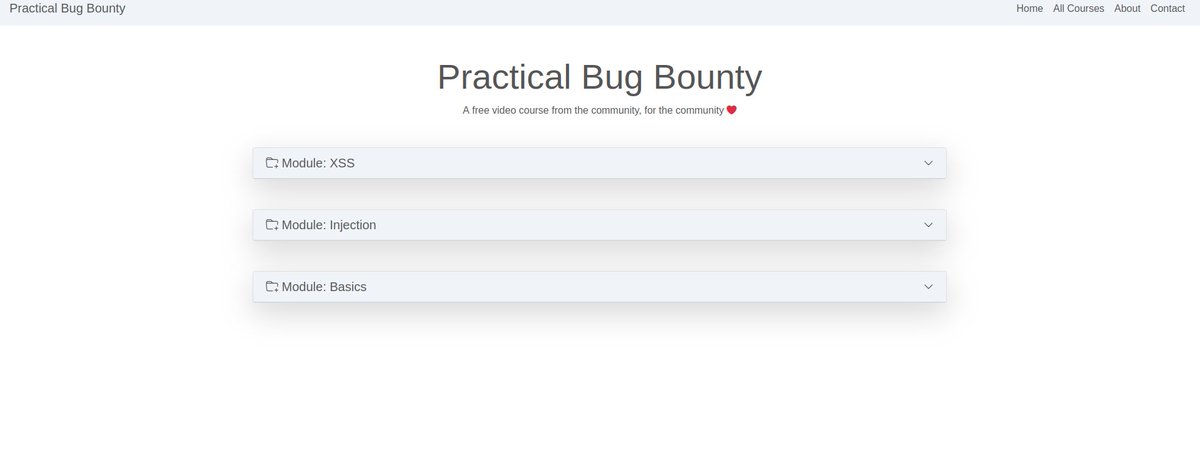
Practical Bug Bounty: A free video course from the community, for the community ❤️ Source: tbm.c3c.io CC: Patrik Grobshäuser #infosecurity #BugBounty #Hacking #infosec #bugbountytips #Pentesting #redteam #cybersecurity #cybersecuritytips #CyberSecurityAwareness
![Basant Karki🇳🇵 (@basant0x01) on Twitter photo Let's find some DOM-based Vulnerabilities [ DOM XSS & Open Redirections ]
Tips
1. Always Check ?returnurl=, ?next= and other redirection parameters before login.
#bugbountytipes Let's find some DOM-based Vulnerabilities [ DOM XSS & Open Redirections ]
Tips
1. Always Check ?returnurl=, ?next= and other redirection parameters before login.
#bugbountytipes](https://pbs.twimg.com/media/FVd8NfFacAAVzkZ.jpg)


