Cyber Sirene
@shreya4n6
CTI Researcher @Fortinet
ID: 1223297669034127364
31-01-2020 17:31:21
73 Tweet
154 Takipçi
689 Takip Edilen






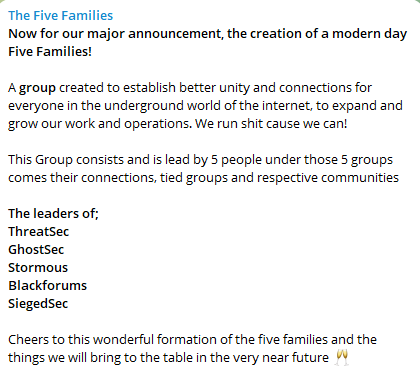
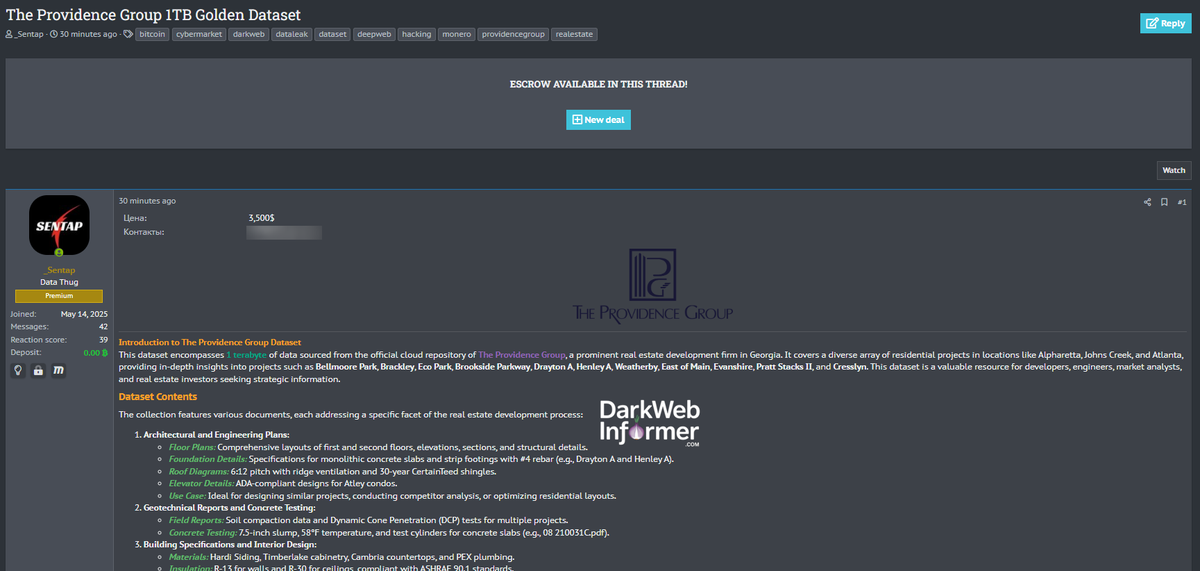
In this post I, Shreya Talukdar and @hacback17 authored a document that delves into The Five Families' Cyber Operations and their overall impact on the web across the globe. Feel free to share your suggestions 👇 #CTI #fivefamilies #hacktivists linkedin.com/posts/shreya4n…