Roger Sels
@selsroger
Founder & Chief Vision Officer, VentureX. Wide interest spectrum. Dad, athlete (racer).
ID: 1276847922
https://www.linkedin.com/in/rogersels 18-03-2013 05:28:18
14,14K Tweet
1,1K Followers
1,1K Following





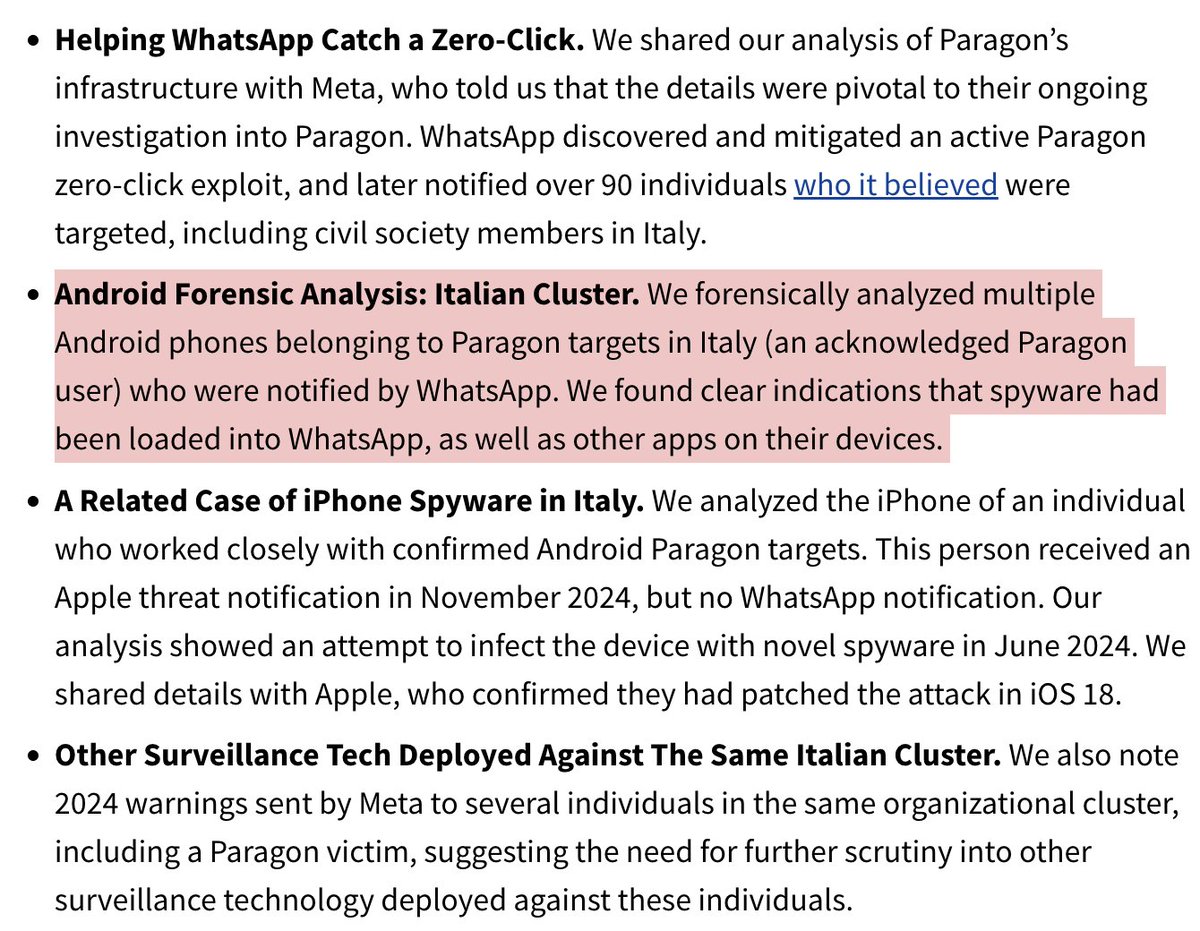
🚨NEW REPORT: first forensic confirmation of #Paragon mercenary spyware infections in #Italy... Known targets: Activists & journalists. We also found deployments around the world. Including ...Canada? And a lot more... Thread on our The Citizen Lab investigation 1/
NEW: North Korea is reportedly launching a new cybersecurity research unit called Research Center 227, which will be housed within the intelligence agency Reconnaissance General Bureau (RGB), and will focus on AI-based hacking and stealing digital assets. techcrunch.com/2025/03/20/nor…