Security Addicted
@securaddicted
Builder & Breaker @MDSecLabs - Lifelong learner
ID: 387571333
http://www.securityaddicted.com 09-10-2011 09:06:58
5,5K Tweet
376 Takipçi
1,1K Takip Edilen

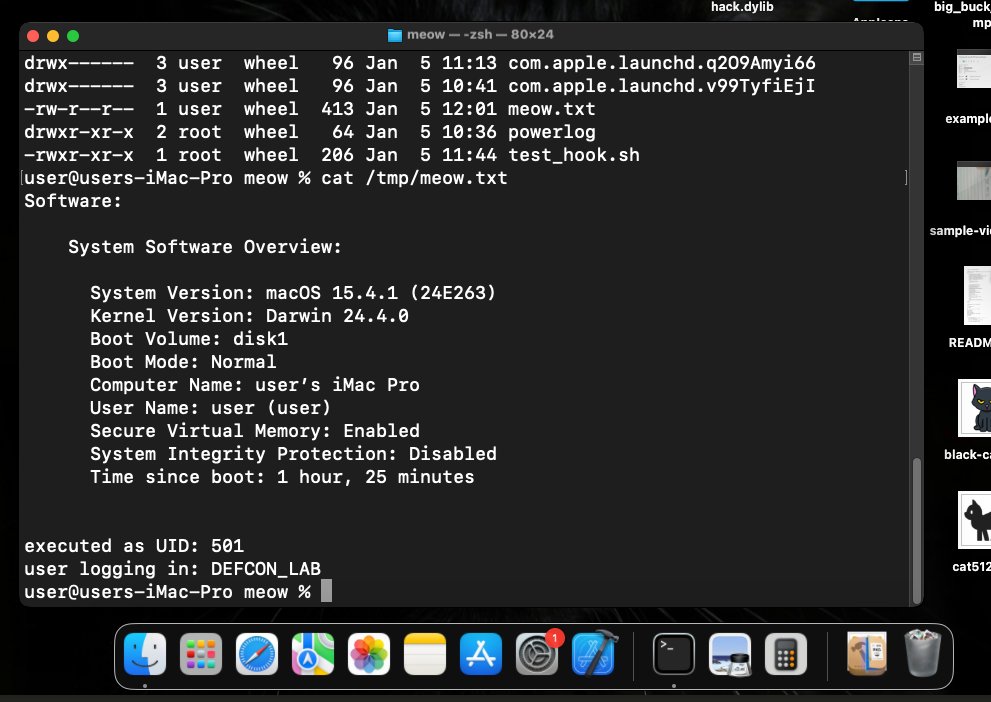
🦠 MacOS Malware Persistence Series Part 1 (LaunchAgents): cocomelonc.github.io/macos/2026/01/… Part 2 (Shell environment hijacking): cocomelonc.github.io/macos/2026/01/… Author: zhassulan zhussupov







🪲 Rust for Malware Development Blog: bishopfox.com/blog/rust-for-… Author: Bishop Fox