Saint_I_Aint
@s41ntsec
FT Purple-Teamer @ A Place You've Heard Of. | Early Career | Windows Focus | 🏳️🌈 -
I share Atk+Def resources, and adore obscure/intricate attack chains.
ID: 1053727499497160704
20-10-2018 19:19:47
3,3K Tweet
56 Takipçi
264 Takip Edilen




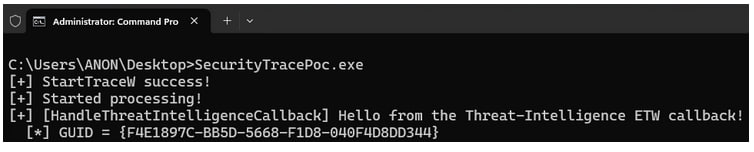
Updated InlineExecuteEx to remove a dependency that was causing failures on arbitrary versions of Windows. Thanks to João Victor for the heads up! github.com/0xTriboulet/In…