apxsec
@runresponder
security guy | pen tester | social engineer
ID: 980719544368029696
02-04-2018 08:12:15
199 Tweet
85 Followers
859 Following

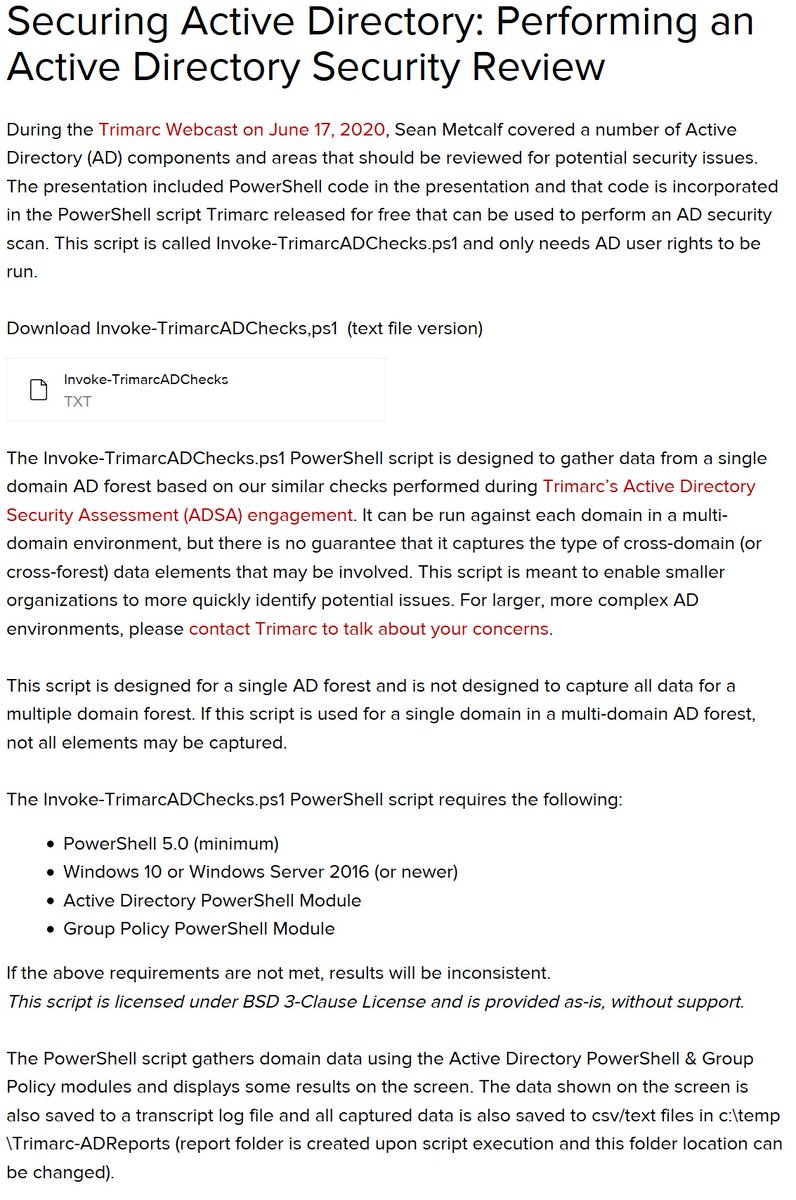
Trimarc just released a free PowerShell script "Invoke-TrimarcADChecks" that Sean Metcalf (Sean Metcalf) covered in his recent Webcast trimarc.co/tw61720 Download the script along with what it gathers, what to review, & Trimarc recommendations trimarc.co/ADCheckScript



Sean O'Mahony DebugPrivilege mRr3b00t Lars Karlslund Separate admin accounts for cloud use Protect cloud from on-prem: techcommunity.microsoft.com/t5/azure-activ… Excellent recommendations for securing privileged access: docs.microsoft.com/en-us/azure/ac… Recommendation for cloud emergency accounts: docs.microsoft.com/en-us/azure/ac…








😶🌫️While working on Nikhil Mittal outstanding Azure Red Team course I've developed a handy powershell toolkit combining various Azure Red Team tactics. Sharing it now, maybe someone will find it useful✨ github.com/mgeeky/AzureRT