Rachel
@richardhu1230
computer science,hacks,sports,music,reading,travel
bbhunter-fkh1bc^
ID: 741620724847251460
11-06-2016 13:18:54
720 Tweet
69 Followers
833 Following

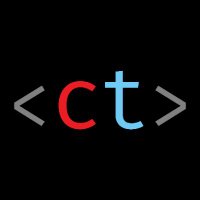
403 on /get_all_users 404 on /get_all_userz Then Justin Gardner fuzzed until a double-encoded “S” slipped past the NGINX filter. Result: 4.5M users' PII dumped. Bounty: $15K–$20K Full talk → youtu.be/PXqlHAoF2wc #BugBounty #DEFCON #BBV #AppSec #WebSecurity


Why spend time manually converting JSON to XML to test for XXE? Just ask Burp AI in Repeater: it handles the transformation and delivers the exploit. Ben Sadeghipour demonstrates this massive shortcut for finding complex, overlooked bugs. 👇



Free Bug Bounty course by Z-wink (the_IDORminator ) ranked #1 in the US on Bugcrowd! Learn from the best, especially if you're into IDOR & Broken Access Control: t.me/ZwinKU