
ReverseThatApp
@reversethatapp
Developer/Develop tweak and patch iOS binary/ Reverse Engineering iOS apps (arm, arm64)/ Learning kernel!!
ID: 567254445
https://reversethat.app 30-04-2012 12:04:21
429 Tweet
354 Followers
812 Following

Unrestrict the restricted mode for USB on iPhone. A first analysis The Citizen Lab #CVE-2025-24200 👉 blog.quarkslab.com/first-analysis…





Thanks to a lot of work put in by Duncan Ogilvie 🍍, IDACode has finally gotten an official update again after 3 years of inactivity! It features stability improvements as well as IDA 9 compatibility improvements! Thanks a lot to everyone involved <3 github.com/ioncodes/idaco…



Community Write-Ups from 8kSec Mobile Security Battlegrounds Our free Mobile Security Labs have inspired some excellent technical deep dives. Below is a running list of community write-ups that detail their techniques, tooling, and exploitation steps. 🤖Android Labs 0xf0rk3b0mb





Really enjoyed #flareon12 — especially challenges 7, 8, and the brutal but fun final challenge (9). 🧠🔥 Thanks to Mandiant (part of Google Cloud) for another amazing RE CTF. #CTF #ReverseEngineering #CyberSecurity


Tried out Harmony for the first time. It’s super handy for reverse engineering obfuscated C# binaries, especially when it comes to automation. I used to struggle automating steps in dnSpy, but Harmony made it seamless. Checkout my writeup on Securinets CTF kos0ng.gitbook.io/ctfs/write-up/…





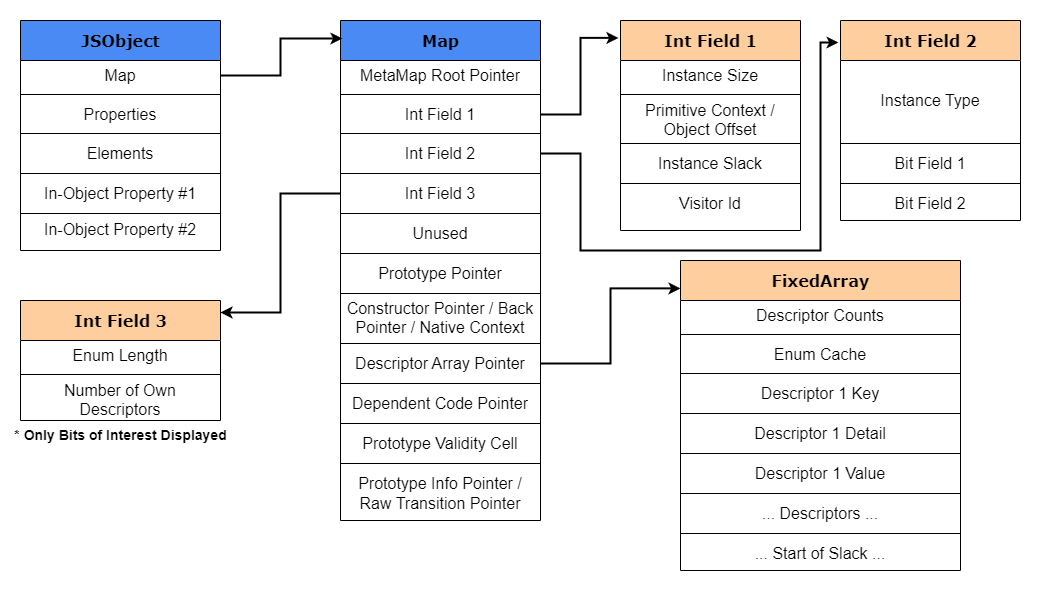
A three part blog series by Jack Halon provides a great introduction into v8 and JS internals, compilation pipeline and ends with analyzing and exploiting CVE-2018-17463 a JIT vulnerability in Turbofan: jhalon.github.io/chrome-browser… jhalon.github.io/chrome-browser… jhalon.github.io/chrome-browser…

CSCG 2026 is live (until 01.05.)! 🥳 Jump in, solve challenges, learn something new, and climb the scoreboard. This year CSCG also serves as the OpenECSC for ECSC 2026 Germany. European Cybersecurity Challenge play.cscg.live


