James Brine
@referefef





There is a new feature on VirusTotal, you can now browse IOCs by threat actors and also get TTPs, pretty cool👌 #ThreatIntelligence #malware #ThreatHunting #infosec






🍯 honeydet A signature based, multi-threaded honeypot detection tool Supports hex, string, and regex signatures By James Brine github.com/referefref/hon…



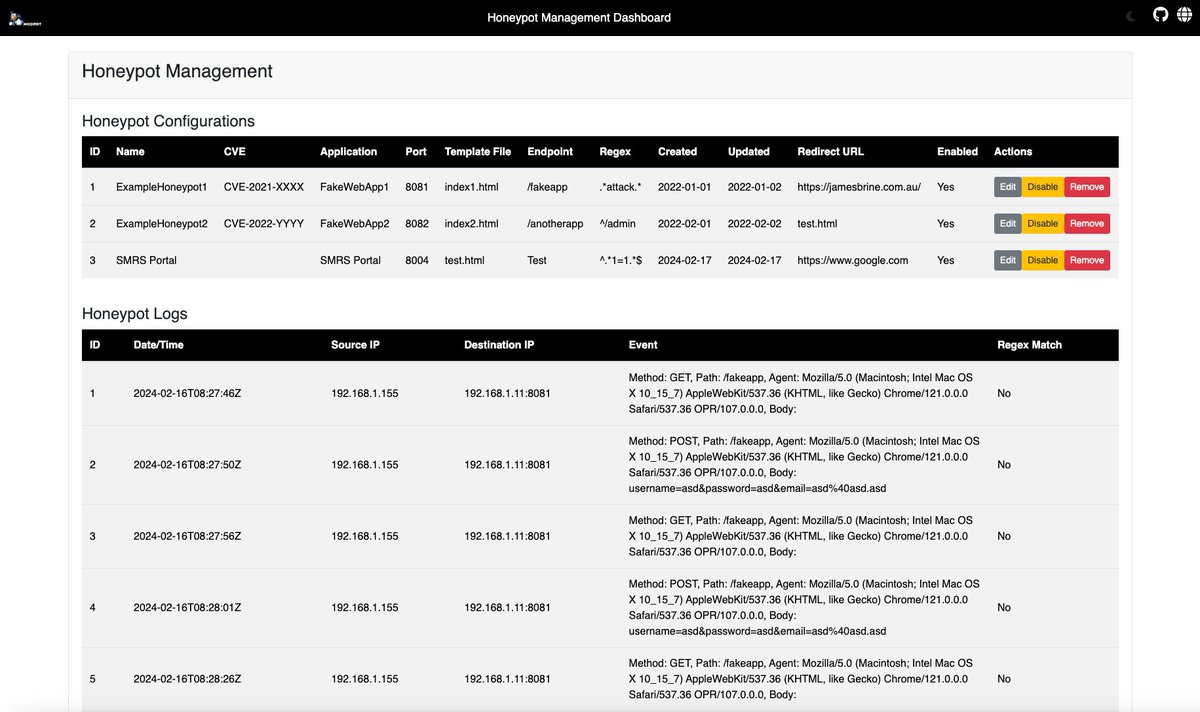
🍯 modpot A modular web-application honeypot platform built using go and gin Allows the user to deploy simple HTML/JS honeypots that mimic web apps in order to detect requests and form entries that are related to attacks By James Brine github.com/referefref/mod…

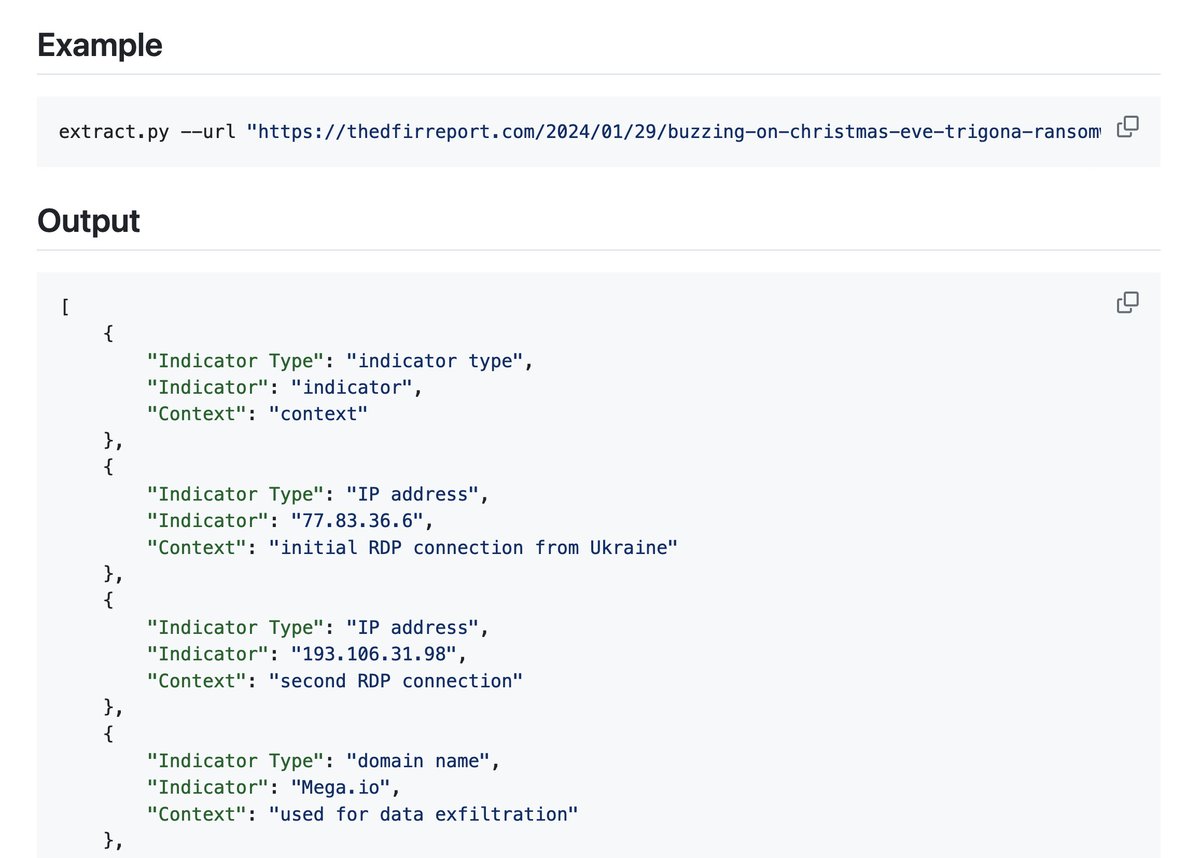
🔬 aiocrioc An LLM and OCR based Indicator of Compromise Extraction Tool Extracts IP addresses, domains, URLs, etc., from text using GPT-4 Then analyzes all text from images after OCR-ing them with Pytesseract By James Brine #cybersecurity github.com/referefref/aio…

🚪gitdoorcheck A static analysis tool that uses OpenAI's GPT-4 to scan git repos Checks each file for: * Potential backdoors * Extraction of credentials * Persistence * Any other potentially malicious functions By James Brine github.com/referefref/git…


🤖 Sinon A tool that automates the setup of Windows-based deception hosts Uses GPT-4 to generate content (files, emails, etc.) And a config file that supports various actions that emulate user behavior By James Brine #blueteam github.com/referefref/sin…