ifhsec
@redchen5
Web application security ⚡ |
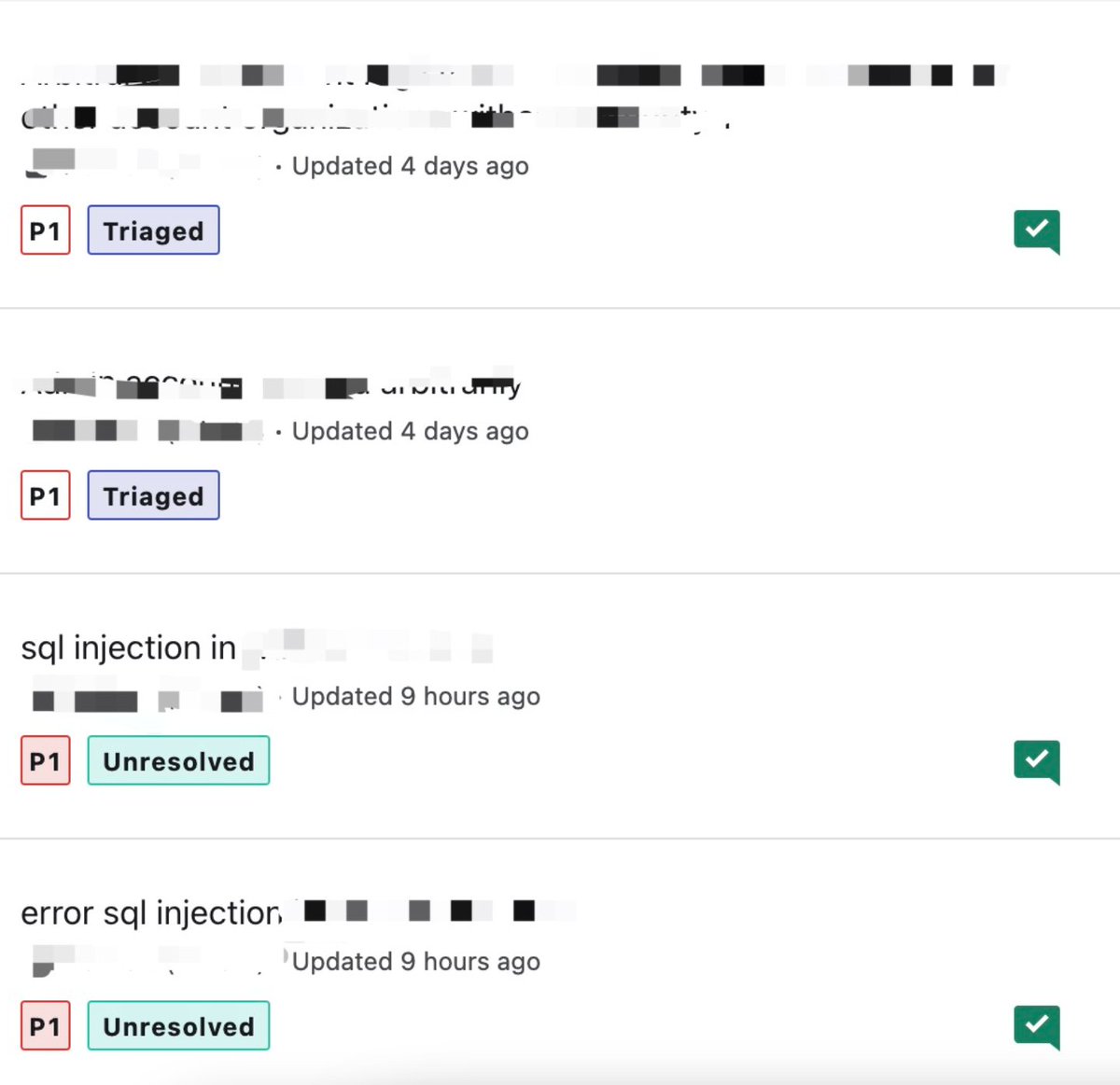
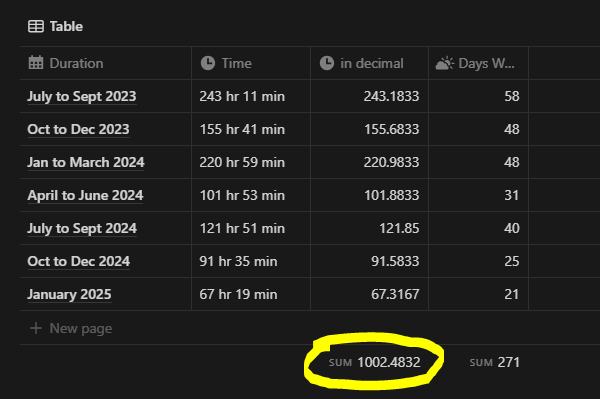
@Bugcrowd P1 vulnerability submission top 20, overall ranking top 100,from ifhsec security team
ID: 794356851617861632
https://bugcrowd.com/ifhsec 04-11-2016 01:53:26
68 Tweet
199 Followers
782 Following









I decided to make a homage-post to Egor Homakov and Nir Goldshlager about different OAuth-token leakage methods I've been researching – ten years after their blog posts that inspired me to start hunt for bugs ♥️ thank you. labs.detectify.com/2022/07/06/acc…