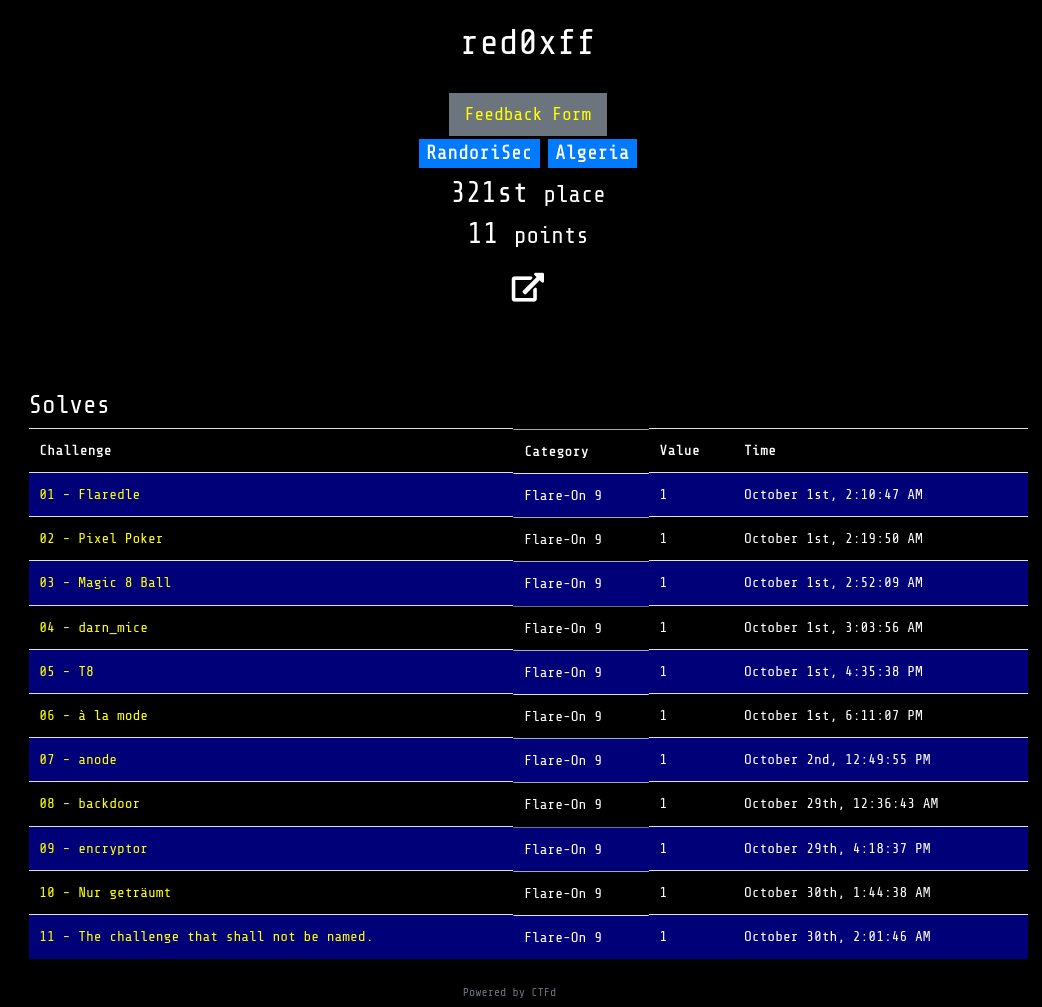
red0xff
@red0xff
Vulnerability research at @apple
Open Source / Offensive Security
ID: 1288423090196746244
https://red0xff.github.io/about/ 29-07-2020 10:36:40
37 Tweet
498 Followers
696 Following











Hajime! We are glad to announce our second ring0 sponsor! 🙏 Thank you RandoriSec for helping us to gather the infosec community in Paris ⛩️ To find out more about RandoriSec, visit their website at randorisec.fr #HEXACON2022


Heap buffer overflow within the Netfilter subsystem of the Linux kernel (CVE-2022-34918). ps: Metasploit Project module coming soon. randorisec.fr/crack-linux-fi… #netfilter #0day